Are you in search of the best Auth0 Alternatives to integrate authentication and authorization for web, mobile, and legacy applications?🤔
We got you covered in this guide. let’s Explore.
As we move to a technical and virtual working environment, maintaining the security of the operation and processes becomes more important than ever.
You must ensure that only authorized personnel access your data, devices, and system. Additionally, you need to keep track of employee logins and other user activities.
As such, you need a system that can help you with the need for having authorization and authentication processes and other security measures. You need an Identity Access Management System.
What is an Identity Access Management System?🤷♂️
An Identity Access Management System is a platform through which an organization can ensure the identity of the users accessing its systems and servers.
The system is used to authorize and authenticate the users into the organization’s system and data so that security can be ensured and there is no threat to the systems, data, or other servers.
Now there are many such systems that organizations can use. One of the most popular ones is Auth0. Let’s have a look at what Auth0 is and how it protects the security of your systems and servers.
What is Auth0?🤔
As mentioned, Auth0 is a platform for identity access management. Its service allows for authorization and authentication on various systems, servers, and applications.
As such, you can ensure higher security and be relieved that none of your organization’s systems and databases is at risk.
The service is highly compatible and useful for social media platforms and applications, and you can equip all your accounts with added security. Additionally, you can use Auth0 on applications like Zoom, Dropbox, etc., as well.
With this service, you can add user login ids and ensure access is available only to identify and authorize people and personnel.
Additionally, the service has other features and functionalities, such as authentication, account integration, database migration, etc., to further enhance the security of your systems.
The system also has an admin dashboard that can be used to assign, monitor, and manage user logins and activities. The admins can assign login ids and passwords by creating different user accounts.
Additionally, the admins can control users’ authorization and access by creating role-based accounts and authorizations.
With all these features and functionalities, it’s easier for the admins to know any unwanted user activity causing threats to the systems and control the same in real-time.
Auth0 is a service that every organization needs in its setting. However, it’s not the only authorization and authentication platform available for enhancing the security of your systems and applications.
Many other platforms are available with nearly the same features and functionalities, and these other options may work out just as well for you, if not better.
So, you might want to check them out. Here are some of the best Auth0 alternatives for you to try.
Best Auth0 Alternatives – Our Top Pick👌👌
With the constantly prying eyes of hackers and attackers on your systems, servers, and applications, securing them is more important than ever.
Authentication, authorization services, and platforms like Auth0 are perfect for your needs and requirements.
But Auth0 is not the only solution you have got for this purpose. There are many more applications, platforms, and services that you can use to secure your applications, systems, and databases.
Now, it never hurts to have your options handy. So, looking at them and seeing if something might work out better will only be wise.
So, here’s a list of some of the best Auth0 alternatives you can check out and try to secure your systems, servers, applications, and databases through end-to-end authorization and authentication.
1. Keycloak – Open-source Auth0 Alternatives
One of the best Auth0 alternatives is Keycloak. This auth0 alternatives open source software comes with a range of features and functionalities that are perfect for securing your systems, servers, applications, and databases and preventing them from unauthorized logins and access.
The software provides three different methods of authentication and authorization. You may choose any of the methods as you feel convenient based on the level of security you need for your systems and data.
Additionally, you can sync all your data within this application and ensure that it never falls into the hands of the wrong people. The best part is that it seamlessly secures your social media accounts.
This is helpful, especially when using social login for all your social media platforms and accounts.
With authorization and authentication put on your social media accounts, you can secure all of them at once. That will be added security, all in addition to the existing passwords you put on those accounts.
With all these features and functionalities, Keycloak is a great authentication and authorization platform, perfect for enhancing the safety and security of all the systems, databases, and accounts your organization is working on.
Auth0 vs keycloak:-
Auth0 and Keycloak are identities and access management solutions that provide authentication and authorization services to secure applications and APIs.
Here’s a table comparing Auth0 and Keycloak:-
| Feature | Auth0 | Keycloak |
|---|---|---|
| Identity protocols supported | OpenID Connect, OAuth2, SAML, LDAP, WS-Federation | OpenID Connect, OAuth2, SAML, LDAP |
| Social identity providers | Facebook, Google, Twitter, LinkedIn, GitHub, etc. | Facebook, Google, Twitter, LinkedIn, GitHub, etc. |
| Multi-factor authentication | Yes | Yes |
| Passwordless authentication | Yes | Yes |
| User management | Yes | Yes |
| Customizable user interface | Yes | Yes |
| Role-based access control | Yes | Yes |
| User federation | Yes | Yes |
| User self-service | Yes | Yes |
| Support for external identity providers | Yes | Yes |
| Integration with third-party apps and services | Yes | Yes |
| Pricing | Subscription-based, with free tier available | Open source, with optional paid support available |
Pros and Cons of Keycloak:-
Here is a table outlining some pros and cons of using Keycloak:-
| Pros | Cons |
|---|---|
| Open Source – Keycloak is an open-source identity and access management solution, which is free to use and customize to your specific needs. | Complexity – Setting up and configuring Keycloak can be a complex process, particularly if you are new to the platform or have complex requirements. |
| Ease of Use – Once you have Keycloak set up, it provides an intuitive and easy-to-use interface for managing users, roles, and permissions. | Limited Support – While Keycloak has an active community of users and contributors, support is primarily provided through community forums and documentation rather than a dedicated support team. |
| Centralized Management – Keycloak allows you to centralize user authentication and authorization for multiple applications, simplifying management and improving security. | Resource Intensive – Keycloak can be resource-intensive, particularly for large-scale deployments, leading to performance issues if not properly managed. |
| Single Sign-On (SSO) – Keycloak provides SSO functionality, meaning users only need to authenticate once to access multiple applications. | Limited Customization – While Keycloak is highly customizable, some advanced customization may require significant development effort. |
| Flexible Integration – Keycloak integrates with a wide range of programming languages, frameworks, and platforms, making it a good fit for many applications. | Lack of Scalability – Keycloak is not as scalable as other IAM solutions, which can concern larger organizations or applications with high traffic loads. |
| Strong Security Features – Keycloak provides robust security features such as multi-factor authentication, social login integration, and password policies. | Compatibility Issues – Keycloak may have compatibility issues with some legacy applications or applications with specific authentication and authorization requirements. |
2. Passport
Passport is another great authentication and authorization services platform supporting various applications and other third-party platforms.
It can connect and integrate with all your social media applications and secure them with multiple authentication methods and modules in-built into its settings.
There are also features and functionalities to help you manage sessions within the applications and platforms. You can control how much time someone can access your systems, databases, and social media accounts.
This way, your accounts remain more protected than ever since no one unauthorized can access your system, and even if they can pierce through the security walls, they wouldn’t get much out of the systems as they shall be logged out before they would know.
Additionally, there are many other features, functionalities, and modules for you to secure your systems and accounts, and you can choose from any of them per your preferences.
With all these features and functionalities, you can keep the hackers and attackers away from your accounts and be assured that you and your entire organization are working in a safe and secure environment where there are no risks of data theft, infringement, hacking, etc.
3. Okta
Okta is the authorization and authentication platform for working on cloud-based servers and environments. Security risks are maximized when working over the cloud, especially public clouds.
Most hackers and attackers keep their eyes on cloud-based applications, services, systems, and platforms and get access to them at the very first opportunity that comes into their hands.
So, you must protect and secure your cloud servers and systems more efficiently than anything else.
Okta is a platform that will help you with the same. Okta is made solely to secure and protect cloud-based systems and programs.
It can add password protection, authentication and authorization, and firewalls to cloud systems, applications, and software.
You can integrate all your cloud-based applications and accounts with Okta and secure them with firewalls.
This way, no unauthorized person can access your cloud applications and servers’ databases, accounts, and other confidential and important information.
Considering all these factors, Okta is a great alternative to Auth0. While it cannot directly protect your applications like Auth0, it’s perfect for your cloud-based programs and applications, which makes it a must-use option for enhancing the security of your cloud operations and functions.
Auth0 vs okta:-
Auth0 and Okta are leading Identity and Access Management (IAM) platforms offering robust authentication and authorization solutions.
while both platforms offer similar features, the target audience and pricing model may be the deciding factor for choosing one.
| Feature | Auth0 | Okta |
|---|---|---|
| Identity management platform type | Authentication and Authorization Platform | Identity and Access Management Platform |
| User authentication | Offers a range of authentication options, including social login, multi-factor authentication, and passwordless authentication. | Offers a range of authentication options, including social login, multi-factor authentication, and passwordless authentication. |
| API security | Offers JWT token validation and OAuth 2.0 support | Offers JWT token validation and OAuth 2.0 support |
| Integration and compatibility | Supports integration with various programming languages and frameworks, including JavaScript, React, Angular, .NET, and Java | Supports integration with various programming languages and frameworks, including JavaScript, React, Angular, .NET, and Java |
| User management | Offers user management features like user registration, user profiles, and user permissions. | Offers user management features like user registration, user profiles, and user permissions. |
| Scalability | Highly scalable and can handle millions of users with ease. | Highly scalable and can handle millions of users with ease. |
| Pricing model | Offers a range of pricing plans based on the monthly active users, with a free plan for up to 7,000 active users. | Offers a range of pricing plans based on the number of monthly active users, with a free plan for up to 1000 active users. |
| Customer support | Offers 24/7 customer support via email and phone, with additional support options for enterprise customers. | Offers 24/7 customer support via email and phone, with additional support options for enterprise customers. |
| Key customers | Atlassian, Autodesk, and Mozilla are some of its key customers. | Adobe, T-Mobile, and FedEx are some of its key customers. |
Pros and Cons of okta:-
Okta provides many benefits for organizations looking to improve security and identity management.
Still, it may not be the best fit for all organizations depending on their budget, specific needs, and the resources they have available for managing a complex platform.
| Pros of Okta | Cons of Okta |
|---|---|
| 1. Robust security features – Okta provides a range of security features, including multi-factor authentication, single sign-on, and adaptive authentication, to help protect user accounts and data. | 1. Cost – Okta can be expensive, especially for small businesses with limited budgets. |
| 2. Easy integration – Okta integrates easily with many third-party applications and services, saving IT teams time and effort. | 2. Complexity – Okta’s features and options can be complex, and some organizations may need additional training or support to use it effectively. |
| 3. Centralized identity management – Okta provides a centralized location for managing user identities and access to applications, which can simplify administration and increase security. | 3. Performance issues – Some users have reported slow performance or outages with Okta, which can be frustrating and impact productivity. |
| 4. Scalability – Okta is designed to scale with the needs of growing businesses, making it a good choice for companies anticipating future growth. | 4. Limited customization – While Okta offers many features, some organizations may find that the platform does not fully meet their specific needs. |
| 5. User-friendly interface – Okta’s interface is designed to be user-friendly, which can help increase adoption and reduce support needs. | 5. Dependency on third-party applications – Okta’s functionality depends on third-party applications and services, which can be a risk if those services experience issues or go offline. |
4. OneLogin
With an extremely easy-to-understand and simple-to-use interface, OneLogin is one of the most comfortable and convenient identity access management systems you can deploy within your organizational settings.
This platform doesn’t require you to go through any unnecessary integrations or other setups, as with other identity access management programs you use for authentication and authorization.
This application is directly compatible with all your on-premise and cloud systems and servers. You can create user identities for all your employees, and that’s it.
Only the people with these specific user identities can log in and access your systems and databases. Moreover, the program even deletes the user identities of those employees who no longer work with your organization.
With that, you need not worry that anyone shall have access to your systems, even after they exit your organization.
With that, the system is essentially simple and easy to maintain. You need not get into any hustle and bustle of changing the system’s passwords and credentials or setting up any authorizations, authentication, or other roles for the authorized personnel.
You only have to set up user ids, and your systems are all secured and free from unwanted and unauthorized access risks.
Considering this ease and simplicity of use, this is one of the great alternatives, especially when your need for an identity access management system is very limited.
5. FusionAuth
With highly advanced features and functionalities, FusionAuth is another great alternative to Auth0. It’s the closest identity access management program that matches the capabilities of Auth0.
Since the platform is multifunctional and compatible with several operating systems and programming languages, you are never restricted in its usage.
Be it a Mac device, Windows system, or Linux computer that you are using, you can secure the systems and applications on it using Auth0.
Additionally, since it’s compatible with several programming languages, you need not have trouble setting up the system.
With that, FusionAuth is extremely easy to set up and use. Moving on to the functionalities and features of this identity access management program, you can easily secure your systems and manage access using SSO and email authentication.
With such features, you can easily confirm the identity of any person accessing your systems and websites and ensure it’s safe from hackers and attackers. Additionally, this system comes with a single-tenant data structure.
So, only authorized users within your organization can access the data within your systems and servers. This further ensures the security of your systems’ confidential data, files, and other databases.
With all these features and functionalities, FusionAuth is a strong and useful alternative to Auth0. You can use it well to meet all your organization’s identity access management needs and requirements.
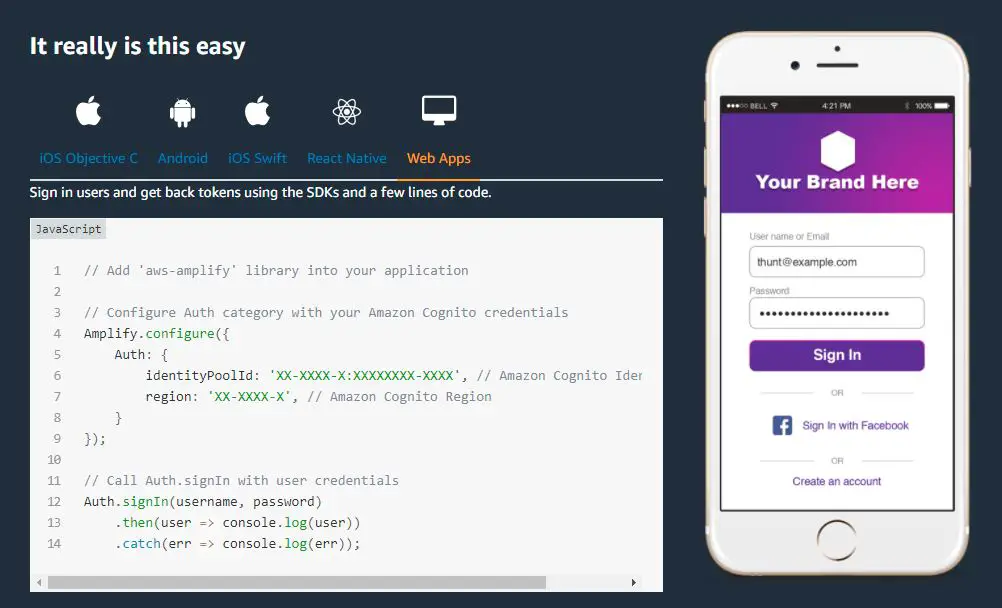
6. Amazon Cognito – Auth0 alternatives AWS
Amazon has established its name in many industry niches and areas, and the largest credit for the same goes to its cloud platform and services that go by the name of Amazon Web Services.
AWS offers over a hundred services, modules, and applications, and the number constantly keeps increasing.
With that, Amazon Web Services didn’t come back with systems, applications, and protocols that would ensure the safety and security of the systems, platforms, and servers for its users.
The uncompromised security of AWS makes it the leading cloud services platform of today’s times. So, AWS also came with an identity access management services platform as a great alternative to Auth0.
Amazon Cognito has excellent features and functionalities for maintaining the security and safety of the systems and servers in your organization.
You can easily secure your mobile applications and other databases and information over them using the authorization, authentication, and administration functionalities of Amazon Cognito.
The Amazon Cognito platform lets you secure the systems with user login ids. You can also put these ids on all your third-party applications and social media accounts.
This way, any application on your systems shall be opened only with these user ids.
As you set up the user ids, you start gaining control over your systems and applications, ensuring that only the authorized users access your systems and applications.
In addition to granting this safety and security for your systems, the application also comes with a separate Amazon Cognito ecosystem wherein you can view all the user activities and the billing of the services.
With all of that, Amazon Cognito is a pretty sleek alternative to Auth0, and you shall love the layer of security and protection it adds to all your applications and databases.
Auth0 vs cognito:-
Auth0 and Amazon Cognito are cloud-based authentication and authorization services that allow developers to easily add user sign-up, sign-in, and access control to their applications.
The two choices largely depend on pricing, integration with other services, and specific feature requirements.
Here’s a table comparing Auth0 and Amazon Cognito:-
| Feature | Auth0 | Amazon Cognito |
|---|---|---|
| Pricing | Auth0 offers a variety of pricing plans, starting at $0 for up to 7,000 active users per month and going up to custom enterprise plans. | Amazon Cognito offers a free tier with limited usage, and then charges per user per month for higher levels of usage. |
| Identity Providers | Auth0 supports many identity providers, including social logins (Facebook, Google, Twitter), enterprise logins (Active Directory, LDAP), and more. | Amazon Cognito supports fewer identity providers, but integrates well with other AWS services like AWS Identity and Access Management (IAM) and Amazon API Gateway. |
| Integration | Auth0 offers extensive documentation and SDKs for easy integration with various platforms and languages. | Amazon Cognito offers similar integration support, but is especially useful for developers already using other AWS services. |
| User Management | Auth0 offers a customizable dashboard for managing users, including support for user roles and permissions. | Amazon Cognito offers a similar level of user management functionality, with additional support for multi-factor authentication (MFA) and password policies. |
| Security | Auth0 offers advanced security features like anomaly detection, brute force protection, and real-time threat intelligence. | Amazon Cognito also offers advanced security features like MFA, adaptive authentication, and integration with AWS Shield for DDoS protection. |
| Customization | Auth0 offers a high degree of customization options for branding and user experience. | Amazon Cognito offers some customization options, but is more limited in this area. |
Pros and Cons of amazon cognito:-
| Pros | Cons |
|---|---|
| Simplifies user authentication and authorization | It may not be cost-effective for small-scale projects |
| Integrates with AWS services and third-party providers | Limited customization options for the user interface |
| Supports social identity providers and multi-factor authentication | Requires some knowledge of AWS to utilize fully |
| Offers scalable user management and data synchronization | Lack of support for certain authentication methods |
| Provides secure token-based authentication | Limited support for non-HTTP protocols |
| Allows for user sign-up and sign-in without backend development | It relies on AWS infrastructure, which may lead to vendor lock-in |
| It can be used for web and mobile applications | Debugging and troubleshooting can be challenging |
7. Akamai Identity Cloud
With a host of features, functionalities, and additional services. Akamai Identity Cloud is one of the most feature-rich Auth0 alternatives for identity access management, especially when dealing with a huge client base and your systems and operations are vast.
This identity access management service is most popular for its personalized and smooth user experiences. As such, you can deliver many important personalized experiences to your clients and users while also ensuring the safety and security of your systems and servers.
The platform is equipped with several authorizations and authentication functionalities and features.
You can easily configure the user identity and access in this platform and ensure that only authorized people enter your systems and applications. Additionally, you can set up different criteria for authorization and authentication.
In addition to helping secure the applications and systems with authorization and authentication requirements, this system also helps protect your data with seamless data analysis and monitoring.
As such, you can manage and analyze all your customer data and information using Akamai Identity Cloud and even use the services to bring profitable and lucrative conversions and sales for your organization.
So, not only does this system help with identity access management, but you can even use it to meet your marketing and sales needs and requirements.
With that, Akamai Identity Cloud is one of the most robust alternatives to Auth0, with many additional features and functionalities that can bring about amazing growth potential and success for your organization.
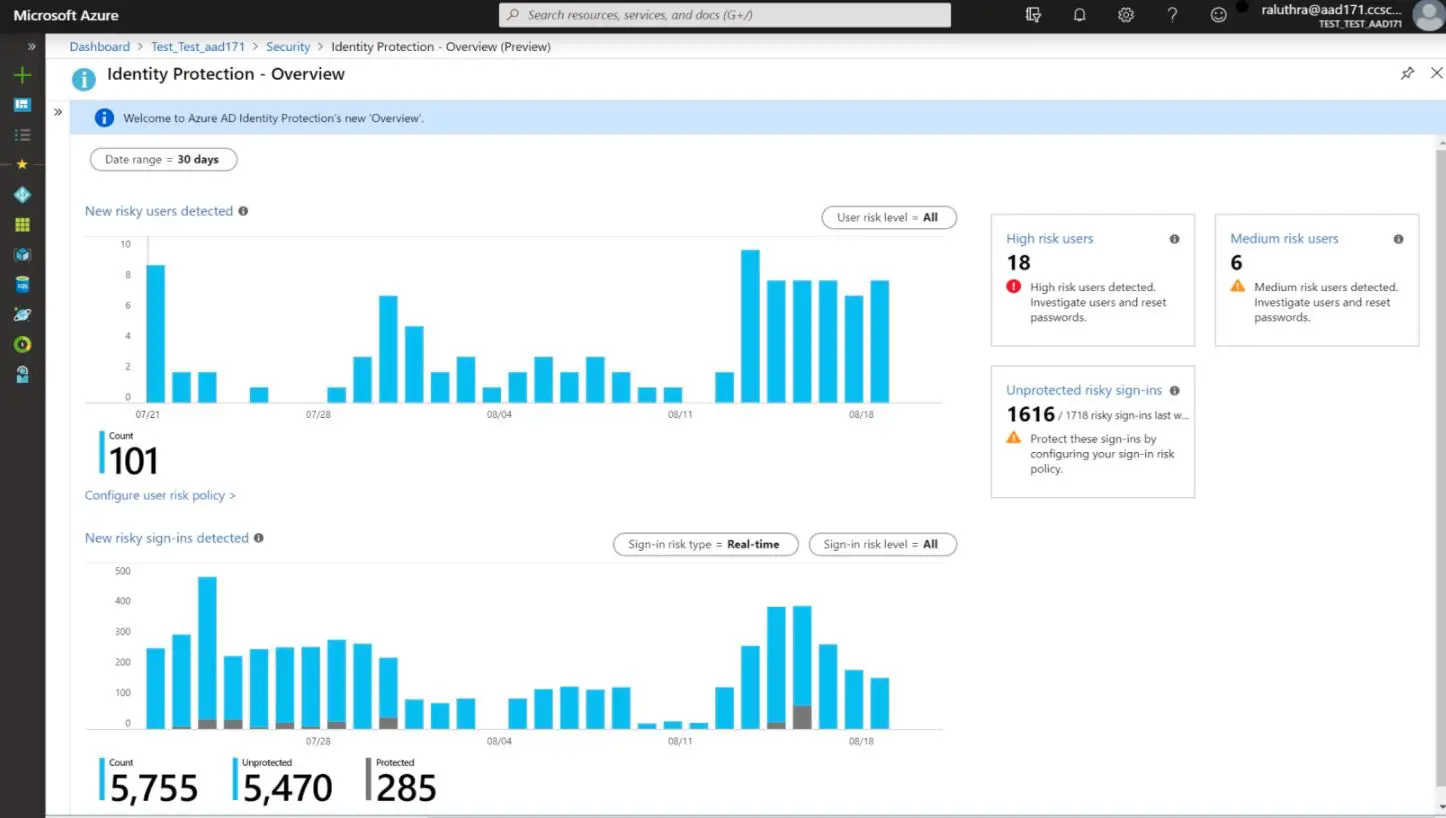
8. Microsoft Azure Active Directory
Microsoft Azure is another cloud-based service with a known name in the industry. It’s known for its phenomenally secure user experiences over its cloud platforms. Microsoft Azure has also developed a system to help organizations manage user identities and access.
Whether you want to manage access for your employees and other personnel in the organization or your clients and customers, Microsoft Azure Active Directory is a helpful solution for that purpose.
It’s an identity access management system and a complete user and operations management solution.
You can easily create user accounts and identities and assign roles for managing access to organizations’ systems and applications.
The entire software has multi-factor authentication systems that help ensure that only authorized people enter and access your systems and databases.
In addition to multi-factor authentication, this system allows you to manage and analyze user behavior and activities, immediately identifying any suspicious activity that can threaten the system and operational security.
Moreover, integrating third-party tools and applications also adds protection and security to those systems. Besides that, the system works well for cloud applications as well.
You can use Microsoft Azure Active Directory to create, edit, delete, and manage user identity and access for both on-premise and cloud applications.
With all these features and functionalities, Microsoft Azure Active Directory is a must-try identity access management system for user authentication and authorization and a great alternative to Auth0.
Auth0 vs Microsoft Azure Active Directory:-
the choice between Auth0 and Azure AD depends on the specific needs and requirements of the organization. Auth0 is ideal for smaller businesses that require comprehensive user management features and easy integration with various applications and platforms.
Azure AD is suitable for larger enterprises that require more advanced IAM capabilities and integration with other Microsoft products and services.
| Feature | Auth0 | Microsoft Azure Active Directory |
|---|---|---|
| User Management | Provides comprehensive user management features, including authentication, authorization, user registration, and user profile management. | It provides user management capabilities, including authentication and authorization, but focuses more on enterprise-level identity and access management. |
| Pricing | Offers a tiered pricing model based on the number of monthly active users (MAUs) and the features used. The pricing is relatively affordable for small to medium-sized businesses. | Pricing varies depending on the edition and features used. Azure AD can be expensive for smaller businesses but provides more value for large enterprises. |
| Ease of Use | Easy to use and can be integrated with various applications and platforms with minimal coding. | Complex and may require some technical expertise to set up and manage. However, it provides a high degree of customization and flexibility. |
| Security | Offers robust security features, including multi-factor authentication (MFA), single sign-on (SSO), and identity verification. | It offers similar security features as Auth0, but is more focused on enterprise-level security and compliance. |
| Scalability | Highly scalable and can handle millions of users and requests without any issues. | Designed to handle enterprise-level workloads and is highly scalable. |
| Integration | It can be easily integrated with various applications and platforms, including third-party APIs, social logins, etc. | Offers seamless integration with various Microsoft products and services, including Microsoft Office, SharePoint, and more. |
| Support | Provides excellent support and resources, including documentation, tutorials, and a vibrant developer community. | Offers support through various channels, including phone, email, chat, and community forums. |
Pros and Cons of Microsoft Azure Active Directory:-
| Pros | Cons |
|---|---|
| Provides robust security features such as multi-factor authentication, conditional access policies, and identity protection | It can have a steep learning curve, especially for users who are not familiar with Microsoft’s products and services |
| Integrates seamlessly with other Microsoft products and non-Microsoft applications | Requires a reliable internet connection to function properly, which can be a potential point of failure |
| Highly scalable, making it a good option for enterprises of all sizes | Some features, such as self-service password reset and group-based licensing, are only available in the paid versions of Azure AD |
| Offers centralized management of identities and access across multiple applications and platforms, making it easier to manage user accounts and access rights | It can be complex to set up and configure, especially for larger organizations with complex access management requirements |
| Cost-effective pricing plans, including a free plan for basic identity and access management needs | Since Azure AD is a Microsoft product, it may lead to vendor lock-in and limit the ability to switch to other identity and access management solutions in the future |
9. LoginRadius
If you need to manage the identity and access of your customers within your organization system, then LoginRadius is the solution you need.
This Auth0 alternative is a cloud-based identity access management system and solution with seamless features and functionalities for managing customer data and information.
It helps create customer identities with customer registration and incorporates an authentication system to ensure that only authorized customers access your applications and databases.
With all that, it’s easier to maintain and manage your customer information and identity and provide them with the most amazing and seamless user experiences while ensuring the system’s security is not compromised.
Considering these features and functionalities, we can say that while not a very robust identity access management system like Auth0, it still is quite feature-rich and can come as a good Auth0 alternative, especially when all you need from the authentication and authorization service is security for your customer information and data.
10. Simeio
Next and last on our list of options for the best Auth0 Alternatives and services platforms is Simeio, an efficient hosted management service for maintaining the security of your on-premise and cloud applications and databases.
The platform offers security and safety for your applications and resources by securing them with authorization and authentication keys. So, anyone who needs access to any of your databases would need to authenticate his/her identity as authorized personnel and user.
This way, you can remain assured that only known users you granted access to can look through your files, systems, and databases.
With this secure authentication functionality, Simeio is a considerable authentication and authorization service for meeting your identity access management system needs and requirements.
Of course, it lacks many features and functionalities possessed by Auth0; however, if your needs are limited, you can consider this platform a good alternative.
📗FAQ
What is equivalent to Auth0?
Some alternatives to Auth0 include Okta, Firebase, AWS Cognito, Keycloak, and Azure AD B2C.
What is the difference between Auth0 and Okta?
While both Auth0 and Okta offer identity and access management solutions, there are differences in their pricing, features, and target audiences. Auth0 is geared toward developers and smaller organizations, while Okta is aimed at larger enterprises with more complex needs.
What is the advantage of using Auth0?
Auth0 offers a range of benefits, such as its ease of use, flexibility, and scalability. It also provides a secure way to authenticate users and supports various identity providers, including social media accounts and enterprise identity providers.
Is Auth0 free and open source?
Auth0 is not open source, but it offers a free plan that allows up to 7,000 active users per month.
Does Okta own Auth0?
No, Auth0 is not owned by Okta.
Does Microsoft use Auth0?
While Microsoft does not use Auth0 for its identity and access management needs, it offers integration with Auth0 for developers and organizations that use Microsoft Azure.
Why is Okta so popular?
Okta’s popularity can be attributed to its wide range of features, ease of use, and ability to integrate with various identity providers and applications. It also offers strong security and compliance features, making it a popular choice for enterprise-level organizations.
Why is Okta so good?
Okta offers a range of benefits, such as its ease of use, flexibility, scalability, and strong security and compliance features. It also integrates well with various identity providers and applications.
Why is Okta the best?
While Okta may not necessarily be the best solution for every organization, it is often considered a top choice due to its comprehensive feature set, scalability, and strong security and compliance capabilities.
What database does Auth0 use?
Auth0 uses various databases, including MongoDB, Cassandra, and Redis, depending on the specific service or feature.
What is the difference between Google OAuth2 and Auth0?
While Google OAuth2 and Auth0 are used for authentication and authorization, they differ in their features and target audiences. Google OAuth2 is primarily aimed at developers who want to integrate with Google’s services.
At the same time, Auth0 is more geared toward developers and organizations that require a more comprehensive identity and access management solution.
How to secure an API with Auth0?
To secure an API with Auth0, you can use its API authorization features, such as setting up scopes and permissions for specific users or groups. You can also use Auth0’s rule engine to apply custom logic and enforce additional security measures.
How much does Auth0 support cost?
The cost of Auth0 support varies depending on the specific plan and level of support needed. Auth0 offers a range of plans, including a free plan and various paid plans with additional features and support.
What is the difference between Auth0 and Authy?
While both Auth0 and Authy offer authentication solutions, Auth0 primarily focuses on identity and access management, while Authy focuses on two-factor authentication.
Is Okta a Russian company?
No, Okta is an American company based in California.
Is Okta blocked in China?
Yes, Okta is currently blocked in China.
What is the Microsoft equivalent of Okta?
Microsoft offers its own identity and access management solution called Azure Active Directory, similar to Okta.
Is Auth0 hosted on Azure?
While Auth0 can be integrated with Azure for certain features, it is not hosted on Azure.
What is the difference between Auth0 and Keycloak?
While both Auth0 and Keycloak offer identity and access management solutions, there are differences in their pricing, features, and target audiences.
Keycloak is an open-source solution geared towards developers, while Auth0 offers a more comprehensive solution for developers and organizations of all sizes.
What cloud does Auth0 use?
Auth0 can be used on various cloud platforms, including AWS, Azure, and Google Cloud.
What are the negatives of Okta?
Some potential negatives of Okta include its higher cost than other solutions, complexity for smaller organizations, and occasional issues with its user interface.
What are the flaws of Okta?
Some flaws of Okta include occasional service disruptions, challenges with setting up and integrating with certain applications, and limitations with its customization options.
Does Google use Okta?
While Google may use Okta for internal authentication, this information is not publicly available.
Why is Okta dropping?
Without more specific information, it is difficult to determine why Okta may be dropping in popularity or usage.
Should I use Okta or Azure AD?
The decision to use Okta or Azure AD depends on your organization’s specific needs and requirements. Okta may be better for smaller organizations or those with more complex authentication needs.
In comparison, Azure AD may be a better choice for larger enterprises already using other Microsoft products.
Is Okta still growing?
Okta has continued to grow since its founding in 2009 and remains a popular choice for identity and access management.
Why do Microsoft customers use Okta?
Microsoft customers may use Okta for its ability to integrate with various identity providers and applications and its strong security and compliance features.
What are the strengths of Okta?
Some strengths of Okta include its comprehensive feature set, strong security and compliance capabilities, and ability to integrate with various identity providers and applications.
What are the limitations of Okta authentication?
Some limitations of Okta authentication include occasional service disruptions, challenges with customization, and limitations with certain applications or environments.
What database does the military use?
It is unclear which specific database or identity management solution the military uses, as this information is not publicly available for security reasons.
What is the difference between Auth0 and Firebase?
While Auth0 and Firebase offer authentication solutions, their features and target audiences differ. Auth0 is more geared towards developers and organizations that require a more comprehensive identity and access management solution.
At the same time, Firebase focuses more on app development and includes additional features such as a real-time database and cloud messaging.
What is the difference between Azure AD and Auth0?
While Azure AD and Auth0 offer identity and access management solutions, they differ in pricing, features, and target audiences.
Azure AD primarily aims at larger enterprises already using other Microsoft products, while Auth0 is geared toward developers and organizations of all sizes.
What protocols does Auth0 use?
Auth0 supports various protocols, including OAuth 2.0, OpenID Connect, and SAML.
Should I use OpenID or OAuth2?
The decision to use OpenID or OAuth2 depends on your application’s specific needs and requirements. OpenID is primarily used for authentication, while OAuth2 is primarily for authorization.
Does Google use OAuth or OpenID?
Google uses both OAuth and OpenID for its authentication and authorization needs.
What is the best authentication method for API?
The best authentication method for an API depends on your application’s specific needs and requirements. Some common authentication methods include OAuth2, API keys, and JSON web tokens (JWTs).
Which authentication is most secure for REST API?
JSON web tokens (JWTs) are a secure authentication method for REST APIs, as they allow for the transmission of encrypted and signed data, providing an extra layer of security.
What is the difference between Auth0 application and API?
Auth0 application refers to the client-side application that users interact with, while Auth0 API refers to the backend API that handles authentication and authorization requests.
What is the well known rate limit of Auth0?
The well-known rate limit of Auth0 is 100 requests per second for most APIs.
What is the maximum number of tenants in Auth0?
The maximum number of tenants in Auth0 varies depending on the specific plan and level of support needed.
What is the maximum number of users in Auth0?
The maximum number of users in Auth0 varies depending on the specific plan and level of support needed.
What is the disadvantage of Authy?
One disadvantage of Authy is that it primarily focuses on two-factor authentication and does not offer the same comprehensive identity and access management solutions as Auth0 or Okta.
What Authenticator is the safest?
The safest authenticator depends on the specific needs and requirements of your application. Some popular options include Google Authenticator, Microsoft Authenticator, and Authy.
What is a self-hosted alternative to Auth0?
Some self-hosted alternatives to Auth0 include Keycloak, FusionAuth, and Gluu.
How to use Auth0 for authentication?
To use Auth0 for authentication, you can sign up for an account and set up your applications and APIs. You can integrate Auth0 with your application or website to handle user authentication.
How to secure an API without authentication?
Securing an API without authentication is generally not recommended, as this can leave your application vulnerable to attacks and unauthorized access.
Does Amazon use Okta?
While Amazon may use Okta for internal authentication, this information is not publicly available.
Does FedEx use Okta?
While it is unclear whether FedEx specifically uses Okta for its authentication needs, Okta is a popular choice for identity and access management for many large enterprises.
Is Microsoft using Okta?
While Microsoft may use Okta for internal authentication, this information is not publicly available.
Do banks use Okta?
Yes, many banks and financial institutions use Okta for their identity and access management needs.
Does LinkedIn use Okta?
While it is unclear whether LinkedIn specifically uses Okta for its authentication needs, Okta is a popular choice for identity and access management for many large enterprises.
Who is Okta’s biggest competitor?
Okta’s biggest competitor is arguably Microsoft, which offers its own identity and access management solution called Azure Active Directory.
Should I use Okta or Auth0?
Using Okta or Auth0 depends on your organization’s needs and requirements. Okta may be better for larger enterprises with complex needs, while Auth0 may be better for smaller organizations or those focused on application development.
Where is user data stored with Auth0?
User data is stored in Auth0’s databases, which are located in various regions around the world.
Why do people use Auth0?
People use Auth0 for its ease of use, flexibility, scalability, strong security and compliance features, and ability to integrate with various identity providers and applications.
Is Keycloak outdated?
Keycloak is not outdated and is a popular open-source solution for identity and access management..
Why is Okta better than Azure?
Whether Okta is better than Azure AD depends on your organization’s needs and requirements. Okta may be better for smaller organizations or those with more complex authentication needs. In comparison, Azure AD may be a better choice for larger enterprises already using other Microsoft products.
What makes Okta unique?
Okta’s comprehensive feature set, strong security and compliance capabilities, and ability to integrate with various identity providers and applications make it unique among identity and access management solutions.
What is the limitation of Okta?
Some limitations of Okta include occasional service disruptions, challenges with customization, and limitations with certain applications or environments.
Why is Okta better than Duo?
Whether Okta is better than Duo depends on your organization’s specific needs and requirements. Okta offers more comprehensive identity and access management solutions, while Duo primarily focuses on two-factor authentication.
Is Okta a good authenticator?
Okta is a strong authenticator with comprehensive identity and access management solutions.
How is Okta more secure?
Okta is more secure through its strong security and compliance capabilities, such as multi-factor authentication, adaptive authentication, and encryption.
Is Okta SAML compliant?
Yes, Okta is SAML compliant and can integrate with various SAML-based identity providers.
What is the Microsoft equivalent of Auth0?
The Microsoft equivalent of Auth0 is Azure Active Directory, which provides similar identity and access management solutions.
Can I use Azure AD for authentication?
Azure AD can be used for authentication and identity management in cloud and on-premises environments.
Which authentication protocol is best for REST API?
The best authentication protocol for REST API depends on your application’s specific needs and requirements, but popular options include OAuth2 and JWT.
What is the most common authentication protocol?
The most common authentication protocol is likely to be either OAuth2 or SAML.
Is OpenID 2.0 deprecated?
OpenID 2.0 is deprecated and no longer recommended for new applications.
Should I use SAML or OpenID?
The decision to use SAML or OpenID depends on your application’s specific needs and requirements. SAML is generally better suited for enterprise environments, while OpenID is more commonly used in web and mobile applications.
Does Amazon use OpenID?
Amazon may use OpenID for its authentication needs, but this information is not publicly available.
Does Okta use SAML or OpenID?
Okta supports both SAML and OpenID authentication protocols.
Does Apple use OpenID Connect?
Apple uses its own authentication protocol, Sign in with Apple, based on OpenID Connect.
Which is the most powerful authentication method?
The most powerful authentication method depends on your application’s specific needs and requirements, but some popular options include multi-factor authentication and adaptive authentication.
Which authentication method is most popular and why?
Multi-factor authentication is becoming increasingly popular because it provides an extra layer of security beyond traditional username and password authentication.
What is the difference between API basic authentication and OAuth?
API basic authentication involves sending a username and password with each API request, while OAuth involves obtaining and using access tokens for authentication and authorization.
Which is the safest authentication method?
Multi-factor authentication is generally considered the safest authentication method, as it requires users to provide multiple forms of authentication before being granted access.
What is the safest authentication protocol?
The safest authentication protocol depends on your application’s specific needs and requirements, but some popular options include OAuth2 and SAML.
What is the safest form of authentication?
The safest form of authentication involves using multiple factors, such as something the user knows (like a password), something the user has (like a physical token), and something the user is (like biometric data).
What is the maximum token size in Auth0?
The maximum token size in Auth0 depends on your application’s specific needs and requirements, but is generally limited to a few kilobytes.
What is the total number of users in Auth0?
The total number of users in Auth0 varies depending on the specific plan and level of support needed.
What is the rating of Auth0?
The rating of Auth0 varies depending on the source and methodology used, but it generally receives positive reviews for its ease of use, scalability, and strong security features.
Can a user belong to multiple tenants?
Yes, a user can belong to multiple tenants in Auth0.
How many tenants can an Azure account have?
The number of tenants an Azure account can have is not limited.
Can you have multiple tenants in Azure?
Yes, you can have multiple tenants in Azure.
What is the minimum password length for Auth0?
The minimum password length for Auth0 can be configured to meet the specific security requirements of your application.
What are the 3 common authentication types?
The three common authentication types are something the user knows (like a password), something the user has (like a physical token), and something the user is (like biometric data).
What is the weakest authentication?
The weakest authentication involves relying solely on something the user knows, such as a password, which can be easily guessed or stolen.
What is the best 2 factor authentication option?
The best 2 factor authentication option depends on your application’s specific needs and requirements, but popular options include time-based one-time passwords and push notifications.
Can Authy get hacked?
While no system is completely immune to hacking, Authy has strong security measures to protect user data and prevent unauthorized access.
Which is safer Authy or Google Authenticator?
Both Authy and Google Authenticator are considered safe and secure two-factor authentication options.
Which is better Keycloak and Okta?
Whether Keycloak or Okta is better depends on your organization’s specific needs and requirements. Okta is generally better suited for smaller organizations or those with more complex authentication needs, while Keycloak may be a better choice for larger enterprises with more extensive customization needs.
How to integrate Keycloak with Auth0?
Integrating Keycloak with Auth0 may involve using various tools and APIs to facilitate communication between the two systems.
Why not to use Cognito?
Some reasons why someone may choose not to use AWS Cognito include its limitations in terms of customization and scalability, as well as concerns about vendor lock-in and data ownership.
What is the difference between Cognito and SSO?
Cognito primarily focuses on user authentication and management, while SSO (Single Sign-On) provides seamless access to multiple applications with a single set of credentials.
What are alternatives to AWS Cognito?
AWS Cognito’s alternatives include identity and access management solutions, such as Okta and Auth0.
What are the disadvantages of Amazon Cognito?
Disadvantages of Amazon Cognito include its limitations in terms of customization and scalability, as well as concerns about vendor lock-in and data ownership.
Is Cognito a SAML provider?
Yes, Amazon Cognito can act as a SAML provider to enable single sign-on across multiple applications.
What is the equivalent of Cognito in Azure?
The equivalent of Cognito in Azure is Azure Active Directory, which provides similar identity and access management solutions.
Why to use Cognito with Azure AD?
Using Cognito with Azure AD can help provide a comprehensive identity and access management solution that meets your organization’s needs.
Does Cognito use CloudFront?
Amazon Cognito can integrate with Amazon CloudFront to provide secure content delivery for your applications.
Why is Amazon Cognito used?
Amazon Cognito provides user authentication and management for web and mobile applications.
While Amazon Cognito primarily focuses on user authentication and management, it can also be used as an authorization server to grant access to specific resources or actions.
What are the two main components of Amazon Cognito?
The two main components of Amazon Cognito are user pools, which provide user authentication and management, and identity pools, which provide federated authentication and access to AWS resources.
What is the benefit of Cognito in AWS?
The benefit of using Amazon Cognito in AWS is that it provides a fully managed and scalable user authentication and management solution, allowing you to focus on building your application instead of managing your own identity infrastructure.
Is Amazon Cognito serverless?
Yes, Amazon Cognito is a serverless solution that does not require you to provision or manage any servers.
Is Amazon Cognito any good?
Amazon Cognito is generally considered to be a good solution for user authentication and management in web and mobile applications, but its limitations in terms of customization and scalability may make it less suitable for larger or more complex deployments.
How many people use Cognito?
The number of people using Amazon Cognito is not publicly available.
Who acquired Cognito?
Amazon developed and maintains Amazon Cognito as part of its suite of cloud computing services.
Does Cognito use Openid?
Yes, Amazon Cognito supports OpenID Connect for federated authentication and access to third-party resources.
Authentication is verifying a user’s identity, while authorization is granting or denying access to specific resources or actions based on a user’s authenticated identity.
What is the strongest authentication?
The strongest authentication involves using multiple factors, such as something the user knows (like a password), something the user has (like a physical token), and something the user is (like biometric data).
Which authentication method is better?
The best authentication method depends on your application’s specific needs and requirements, but using multiple factors, such as multi-factor authentication, is generally considered the most secure option.
What is the most used authentication API?
OAuth2 is one of the most commonly used authentication APIs, providing a flexible and standardized framework for authentication and authorization.
Who is using Cognito?
Various organizations use Amazon Cognito, including small businesses, startups, and large enterprises.
What is JWT Cognito?
JWT (JSON Web Token) is used for authentication and authorization in Amazon Cognito. It is a compact and standardized format that allows for secure transmission and validation of user data.
What are the 4 types of Azure?
The four types of Azure are infrastructure as a service (IaaS), platform as a service (PaaS), software as a service (SaaS), and serverless computing.
Does Cognito support LDAP?
Amazon Cognito does not currently support LDAP authentication but provides support for other federated identity providers.
Is Cognito an identity provider?
Yes, Amazon Cognito can act as an identity provider to enable federated authentication and access to third-party resources.
What is the difference between Azure IAM and Azure AD?
Azure IAM (Identity and Access Management) is a set of tools and services for managing user access to Azure resources, while Azure AD (Active Directory) is a cloud-based identity management service for managing user access to applications and other resources.
Is Cognito inside VPC?
Amazon Cognito can be integrated with Amazon VPC (Virtual Private Cloud) to provide secure access to your applications and resources.
Yes, Amazon Cognito uses cookies to maintain user sessions and facilitate authentication and authorization.
How secure is Cognito?
Amazon Cognito provides strong security measures to protect user data and prevent unauthorized access, including multi-factor authentication, encryption, and auditing support.
How do you implement Cognito?
Implementing Amazon Cognito involves setting up user pools and identity pools, integrating with your application code, and configuring security and access controls to meet your needs.
Is Cognito Hipaa compliant?
Amazon Cognito is HIPAA (Health Insurance Portability and Accountability Act) compliant, providing the security and privacy controls necessary to handle sensitive healthcare data.
What is the difference between SAML and OIDC in Cognito?
SAML (Security Assertion Markup Language) and OIDC (OpenID Connect) are protocols used for federated authentication and access to third-party resources. The main difference is that SAML is an older and more established protocol, while OIDC is newer and provides more modern features and capabilities.
What is a user pool in AWS Cognito?
A user pool in Amazon Cognito is a secure and scalable directory of user accounts that can be used for user authentication and management in web and mobile applications.
What are the three parts of AWS?
The three parts of AWS (Amazon Web Services) are Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS).
What is the difference between user pool and identity pool in AWS?
A user pool in Amazon Cognito is used for user authentication and management, while an identity pool is used for federated authentication and access to third-party resources.
What is the difference between Okta and SSO?
Okta is an identity and access management solution that provides a range of features and capabilities for user authentication and management. At the same time, SSO (Single Sign-On) is a specific feature that enables users to access multiple applications with a single set of credentials.
Auth0 and Okta are identities and access management solutions but separate companies with their products and services.
Does Okta use AWS?
Okta provides its services through various cloud providers, including AWS (Amazon Web Services).
What are the benefits of Auth0?
Auth0 provides various benefits for organizations, including a flexible and customizable authentication and authorization solution, support for various identity providers and protocols, and strong security measures to protect user data.
Which authentication is better?
The best authentication method depends on your application’s specific needs and requirements, but using multiple factors, such as multi-factor authentication, is generally considered the most secure option.
Does the government use Okta?
Okta provides its services to various organizations, including government agencies and departments.
What companies compete with Okta?
Companies that compete with Okta in the identity and access management market include Microsoft, Ping Identity, and OneLogin.
What are the limitations of Okta?
Limitations of Okta include its cost, which can be high for smaller organizations, and concerns about vendor lock-in and data ownership.
Why do people use Okta?
People use Okta to provide a comprehensive and secure identity and access management solution for their web and mobile applications, supporting various identity providers and protocols.
Is Okta a 2fa or MFA?
Okta provides two-factor authentication (2FA) and multi-factor authentication (MFA) options to enhance the security of user authentication and access security.
Does Salesforce use Okta?
Salesforce provides its own identity and access management solution, but it can be integrated with Okta for federated authentication and access to third-party resources.
What cloud is Okta hosted on?
Okta provides its services through various cloud providers, including AWS (Amazon Web Services), Microsoft Azure, and Google Cloud Platform.
Which database is best for authentication?
The best authentication database depends on your application’s specific needs and requirements, but popular options include MongoDB, PostgreSQL, and MySQL.
What is the difference between authentication and AuthO?
Authentication is verifying a user’s identity, while Auth0 is a cloud-based identity and access management solution that provides a range of features and capabilities for user authentication and management.
Is Auth0 an API?
Auth0 provides a RESTful API that can be used to manage user authentication and access and integrate with other applications and services.
What are the 4 types of authentication?
The four types of authentication are something the user knows (like a password), something the user has (like a physical token), something the user is (like biometric data). Somewhere the user is (like a specific location or IP address).
Is Auth0 expensive?
Auth0 offers all the functionality you require, is simple to set up, and is easy to work with; however, when your user base increases and you need more capabilities, the pricing doesn’t scale well and can get quite expensive.
Is Auth0 necessary?
Auth0 is still a well-liked solution for authentication and authorization support. It can relieve a lot of pressure from your developers, who might not have a deep understanding of cybersecurity.
In addition, it will offer you confidence that your consumers’ data is secure. Auth0 is no longer the only choice, though.
For a comparable and even better experience, consider other technologies like OneLogin, Amazon Cognito, Passport, LoginRadius, etc.
Why is Auth0 the best?
Adding authentication and authorization services to your applications is easy with Auth0, a modular drop-in solution.
As a result, you can save your team and company the money, effort, and risk of developing your user authentication and authorization system.
How is Auth0 different from Okta?
Any firm can enable IAM with the help of Auth0 and Okta. However, Auth0’s extensibility and developer-focused platform would be better for smaller organizations or app development firms with more extensive IAM infrastructure demands.
Larger companies that need to implement their IAM strategy might consider Okta because of its extensive library of pre-built components and integrations.
What is better than Auth0?
Keylock, Passport, OneLogin, FusionAuth, Amazon Cognito, etc., are some of the best Auth0 alternatives you can try out and enjoy advanced authentication and authorization services.
Is JWT the same as Auth0?
The JSON object’s information may be checked and trusted because it is digitally signed. Auth0-issued JWTs are JSON Web Signatures (JWS), meaning they are signed rather than encrypted, even though JWTs can also be encrypted to provide anonymity between parties.
What is Auth0 vs. OAuth?
Users can offer restricted access to resources from one website to another using the OAuth 2.0 protocol without disclosing their login information.
B2C, B2B, B2E, or a combination of them can all be handled by Auth0, an organization that maintains the Universal Identity Platform for online, mobile, and IoT.
Is Auth0 a SAML?
The SAML protocol is supported by Auth0, which can act as the SP, the IdP, or both, supporting SAML2 web applications. SSO integrations with SAML.
Final Words
An identity access management program in your organization is essential to ensure the security and safety of your operations and functions. Moreover, when your systems are secure, your clients and customers trust you more.
Auth0 is a great platform, serving all your needs and requirements, but there are equally good alternatives.
We hope this article about some of the best Auth0 alternatives was helpful to you and you’re well managing the security of your applications and systems.