Welcome to the digital era, where data security is paramount for individuals and organizations. Regarding protecting sensitive information, BitLocker has been a popular choice among Windows users for encrypting their drives.
However, exploring alternatives in today’s dynamic landscape is essential to ensure comprehensive data protection.
In this article, we delve into the world of BitLocker alternatives, presenting you with innovative solutions that offer robust security measures and seamless functionality.
We’ve covered whether you seek enhanced encryption features, cross-platform compatibility, or intuitive user interfaces.
Join us as we explore BitLocker alternatives, empowering you to make informed decisions and confidently safeguard your data.
Discover a range of solutions that cater to your unique needs, ensuring your information remains safe from prying eyes.
Let’s dive in and explore the diverse landscape of BitLocker alternatives, unraveling a new world of data protection possibilities.
Understanding BitLocker
BitLocker, an advanced encryption feature developed by Microsoft, provides robust data protection for Windows operating systems.
BitLocker is an integral part of the Windows ecosystem, offering a seamless solution to safeguard sensitive information from unauthorized access.
Utilizing full-disk encryption, BitLocker encrypts entire volumes, including the operating system, system files, and user data.
This ensures that the data remains secure and inaccessible even if a device falls into the wrong hands. The encryption process employs symmetric encryption algorithms such as AES (Advanced Encryption Standard) and XTS (XOR-Encrypt-XOR) to strengthen data confidentiality.
Users must provide a recovery key or enter the correct BitLocker password to unlock the encrypted volume. These authentication measures ensure that only authorized individuals can access the protected data.
Additionally, BitLocker supports using smart cards and TPM (Trusted Platform Module) for enhanced security.
BitLocker offers a range of features to accommodate various use cases and scenarios. It supports multiple encryption modes, including a transparent mode for system drives and a user authentication mode for data drives.
Furthermore, BitLocker allows for creating encrypted virtual drives called BitLocker To Go, enabling secure data transfer and storage on removable devices.
Understanding BitLocker empowers users to take control of their data security. By implementing this powerful encryption solution, individuals and organizations can protect their sensitive information from potential threats, ensuring peace of mind and compliance with data privacy regulations.
BitLocker Limitations
While BitLocker offers robust data encryption capabilities, it is important to understand its limitations to make informed decisions regarding data security.
By examining these limitations, users can assess whether BitLocker meets their specific requirements or if alternative solutions may be more suitable.
One notable limitation of BitLocker is its platform dependency. It is primarily designed for Windows operating systems, restricting its usage on other platforms such as macOS or Linux.
This can pose challenges for individuals or organizations with diverse operating system environments. Another limitation is cross-platform compatibility. BitLocker-encrypted drives cannot be easily accessed on non-Windows systems, creating potential accessibility issues when sharing or transferring data across different platforms.
Furthermore, BitLocker’s encryption strength and security rely heavily on the integrity of the underlying operating system.
BitLocker’s effectiveness can also be compromised if the operating system is compromised, leaving the encrypted data vulnerable.
Additionally, while BitLocker provides a reliable encryption solution for fixed drives, it may not offer the same level of protection for removable devices such as USB drives or external hard drives.
This can limit its usefulness in scenarios where data needs to be securely transported or stored on such devices. Users need to be aware of these BitLocker limitations and consider them to their specific security needs.
Depending on the use case, alternative encryption solutions may provide more comprehensive protection and overcome the limitations presented by BitLocker.
Best Bitlocker Alternatives – Our Top Pick👌👌
This list is in no particular order and contains alternatives that I have tested and trust to give some value to you. The final choice you make would depend on your personal preferences.
Here is my list of Bitlocker Alternatives:-
1. VeraCrypt
This is a free Bitlocker alternative if you are in the market for a free tool similar to the Bitlocker tool.
The VeraCrypt tool offers many features to users, and full disk/partial encryption is a part of these features. This tool helps with the creation of a virtual encrypted disk. It has advanced features that let you use the user’s hidden OS encryption.
The VeraCrypt software lets you encrypt whole disks, files, removable media, logical volumes, and partitions.
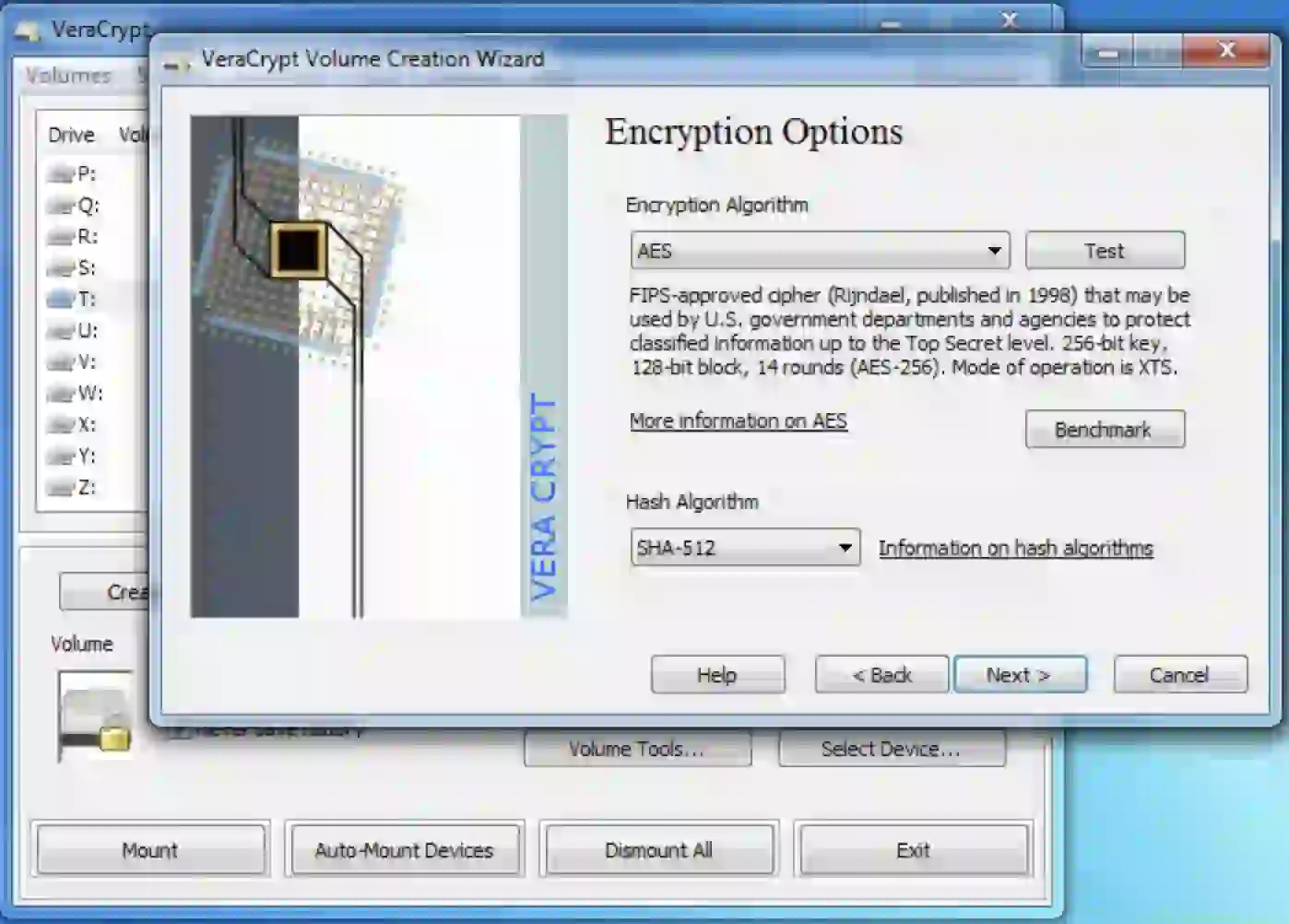
The software is available on Mac OS, Windows, FreeBSD operating systems, and Linux. It is a completely open-source tool that is readily available and user-friendly.
The VeraCrypt is a supporter of the famous AES one, which is an encryption algorithm. It also uses several well-known algorithms, such as Camellia and Twofish, SHA-256, and RIPEMD-160. These algorithms are options for hash algorithms.
Veracrypt vs Bitlocker:-
Veracrypt is a good choice for individuals who value open-source software and want more flexibility regarding encryption options.
Bitlocker is a good choice for those who want a more integrated encryption solution tightly integrated with the Windows operating system and supports hardware encryption.
Here’s a table comparing Veracrypt and Bitlocker:-
| Feature | Veracrypt | Bitlocker |
|---|---|---|
| Encryption | AES, Serpent, Twofish | AES |
| Operating Systems | Windows, macOS, Linux | Windows |
| Open Source | Yes | No |
| License | GNU General Public License (GPL) | Proprietary |
| Cross-platform | Yes | No |
| Volume Encryption | Yes | Yes |
| Full Disk Encryption | Yes | Yes |
| Hidden Volumes | Yes | No |
| Two-Factor Authentication | Yes | Yes |
| Support | Community-driven | Vendor support available |
| Security Audits | Regularly performed | Not publicly disclosed |
| Ease of Use | Requires technical knowledge | User-friendly interface |
| Integration | It can be used with third-party tools | Native integration with Windows |
| Cost | Free | Included with Windows |
2. M3 BitLocker Loader for Windows
M3 BitLocker Loader for Windows provides an excellent alternative to Microsoft’s BitLocker encryption, particularly for users of Windows Home editions.
Its compatibility, user-friendly interface, and support for various encryption methods make it attractive for individuals and organizations seeking reliable data protection.
It enables users to fully utilize the BitLocker encryption function on Windows Home editions, which lack the built-in capability for BitLocker encryption.
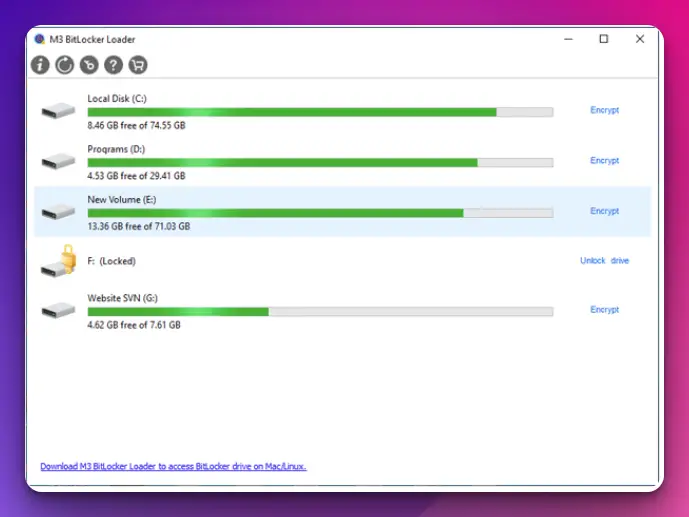
With M3 BitLocker Loader, users can encrypt both system drives and external storage devices, providing robust protection for their data.
Features:-
Here’s a table highlighting some of the features of M3 BitLocker Loader for Windows:-
| Feature | Description |
|---|---|
| BitLocker Encryption | Allows you to encrypt drives and partitions using the BitLocker encryption technology. |
| Windows Preboot Support | Provides support for Windows preboot environments, ensuring compatibility and system integrity. |
| Full Disk Encryption | Enables full disk encryption, ensuring that all data on the drive is protected from unauthorized access. |
| Partition Encryption | Allows you to encrypt specific partitions on your hard drive, providing granular security options. |
| Automatic Encryption | Supports automatic encryption for newly added drives and partitions, ensuring continuous protection. |
| Unlock/Decryption | Optimizes encryption performance while ensuring data security, minimizing the impact on system resources. |
| Password Recovery | It provides the ability to unlock and decrypt BitLocker-encrypted drives and partitions when needed. |
| Management of BitLocker | Enables management of BitLocker settings and configurations, including encryption methods and policies. |
| Integration with Windows | Seamlessly integrates with the Windows operating system, providing a familiar and user-friendly interface. |
| File System Compatibility | Supports various file systems, such as NTFS, exFAT, and FAT32, allowing encryption on different drive types. |
| Bootable Media Creation | Allows the creation of bootable media (USB, CD/DVD) to unlock and decrypt BitLocker-encrypted drives outside of Windows. |
| Encryption Performance | Optimizes encryption performance while ensuring data security, minimizing impact on system resources. |
3. Hasleo BitLocker Anywhere For Windows
To safeguard sensitive information, many users rely on BitLocker, a popular encryption tool developed by Microsoft.
However, what if you need to encrypt your data on a non-Windows operating system? Enter Hasleo BitLocker Anywhere, a reliable BitLocker alternative that allows you to protect your files across multiple platforms.
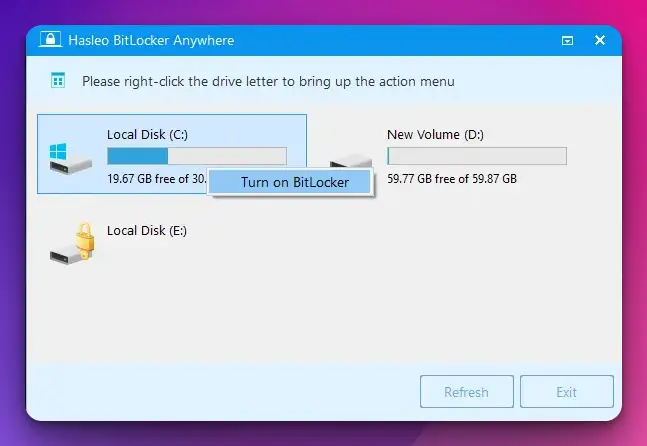
Its cross-platform compatibility, ease of use, advanced encryption algorithms, and comprehensive data protection features offer a compelling solution for safeguarding sensitive files.
Whether a Windows, macOS, or Linux user, Hasleo BitLocker Anywhere empowers you to encrypt your data confidently, providing peace of mind in an increasingly interconnected world.
Features:-
Here’s a table outlining some of the key features of Hasleo BitLocker Anywhere:-
| Feature | Description |
|---|---|
| Full Drive Encryption | Encrypts an entire drive or partition, including system drive (requires a restart). |
| Encryption for External Drives | Encrypts external hard drives, USB flash drives, SD cards, etc. |
| Encrypt Windows and Non-Windows | Encrypts drives on Windows 10/8.1/8/7 Home, Windows 8 Core and Windows 7 Professional with a password or a smart card. |
| Decryption | Decrypts BitLocker-encrypted drives, allowing users to access the data on them without the password. |
| Mount/Unmount | Mounts or unmounts BitLocker encrypted drive for read-write or read-only access. |
| Changing Password | Changes password of BitLocker encrypted drive without decrypting the entire drive. |
| Adding or Removing Key | Adds or removes password/smart card as a key to unlock BitLocker encrypted drive. |
| Automatic Unlock at Boot | Decrypts BitLocker-encrypted drives, allowing users to access the data on them without a password. |
| TPM Support | Supports TPM (Trusted Platform Module) version 1.2/2.0. |
| Command-Line Support | Supports command-line operation for advanced users. |
| Compatibility | Encrypts an entire drive or partition, including a system drive (requires a restart). |
| Windows To Go Encryption | Compatible with different file systems such as NTFS, FAT16, FAT32, and exFAT works on various types of hard drives, USB drives, and other storage devices. |
| 30-day free trial | Offers a 30-day free trial version. |
4. GNU Privacy Guard
Are you concerned about the security of your confidential data? In today’s interconnected world, safeguarding sensitive information has become more crucial.
One powerful solution that offers robust protection for your files is GNU Privacy Guard (GPG). As an exceptional alternative to Bitlocker, GPG empowers you with advanced encryption capabilities to keep your data secure from prying eyes.
Whether you’re a privacy-conscious individual, a business owner, or an organization looking for enhanced data protection, GPG offers a comprehensive set of features that will exceed your expectations.
Features:-
Here’s a table summarizing some key features of GNU Privacy Guard:-
| Feature | Description |
|---|---|
| Encryption | Provides strong encryption algorithms for secure messaging, file, and email encryption. Supports symmetric and asymmetric encryption, including OpenPGP standard. |
| Digital signatures | Allows users to sign messages and files with digital signatures to verify the authenticity and integrity of the content. |
| Key management | Enables users to manage their encryption keys, including generating new, revoking, and importing/exporting keys. |
| Cross-platform | Available on Windows, macOS, Linux, and Unix-based systems, allowing for secure communication across different operating systems. |
| Open-source | Source code is publicly available and can be reviewed and audited by anyone, ensuring transparency and security. |
| Command-line interface | Provides a command-line interface for automation and integration with other software and systems. |
| Multiple languages support | It supports many different languages, making it accessible to users worldwide. |
| Integrations | Integrates with various email clients and applications, including Mozilla Thunderbird, Microsoft Outlook, and Apple Mail. |
| Trust model | Uses a web of trust model for decentralized and community-based trust systems. Users can vouch for the authenticity of each other’s encryption keys. |
5. AxCrypt
In a world where data breaches and cyber threats are rising, it is crucial to employ robust encryption tools to protect sensitive information.
AxCrypt, with its cross-platform compatibility, user-friendly interface, strong encryption algorithms, and advanced file-sharing capabilities, stands out as a reliable alternative to BitLocker.
Whether you are an individual looking to secure personal files or an organization seeking to protect valuable data, AxCrypt offers a seamless and efficient solution.
With AxCrypt, encrypting files or folders is as simple as right-clicking and selecting the encryption option. The streamlined process ensures that even non-technical users can secure their data effortlessly.
Furthermore, AxCrypt’s seamless integration with Windows Explorer makes encryption and decryption operations conveniently accessible within the file explorer.
Features:-
| Feature | Description |
|---|---|
| File Encryption | AxCrypt allows you to encrypt individual files or folders using strong encryption algorithms, providing secure data protection. |
| AES Encryption | Users can set a strong password to encrypt their files, ensuring only authorized individuals can access the encrypted data. |
| Folder Encryption | AxCrypt integrates with popular cloud storage services like Dropbox, Google Drive, and OneDrive, allowing seamless encryption. |
| Password Protection | AxCrypt can encrypt entire folders, including subfolders and their contents, making it easy to secure multiple files simultaneously. |
| File Shredder | AxCrypt allows you to work with encrypted files, even offline, ensuring that your data remains protected. |
| Cloud Storage Integration | A file shredder feature securely deletes files, making them unrecoverable, which is useful when you need to remove data permanently. |
| Key Sharing | You can securely share encrypted files with others by sharing the key or password with authorized recipients. |
| Multiple Platform Support | AxCrypt is available for Windows, macOS, Android, and iOS, ensuring cross-platform compatibility for encrypted files. |
| Two-Factor Authentication | AxCrypt supports two-factor authentication for enhanced security, adding an extra layer of protection to your encrypted files. |
| File Access Tracking and History | It provides an activity log that tracks file access attempts, allowing you to monitor who has attempted to open your encrypted files. |
| Offline Mode | AxCrypt offers a free version with limited features and a premium version with additional functionalities for more advanced users. |
| Command Line Interface (CLI) | It provides a command line interface for advanced users, allowing them to perform encryption and decryption operations programmatically. |
| Free and Premium Versions | AxCrypt allows you to work with encrypted files, even offline, ensuring your data remains protected. |
Bitlocker vs AxCrypt:-
If you require full-disk encryption on Windows systems, BitLocker is a suitable choice. On the other hand, if you need file-level encryption with cross-platform support, AxCrypt is a viable option.
Here’s a comparison table between BitLocker and AxCrypt:-
| Feature | BitLocker | AxCrypt |
|---|---|---|
| Encryption Method | AES encryption (128-bit or 256-bit keys) | AES encryption (128-bit or 256-bit keys) |
| Supported OS | Windows 10 Pro, Enterprise, and Education | Windows, macOS, Android, iOS, Linux |
| Encryption Modes | Full disk encryption and individual files | Individual files and folders |
| User-Friendly | Integrated into Windows, easy to use | User-friendly interface |
| Authentication | Password or TPM (Trusted Platform Module) | Password-based authentication |
| Key Management | Can store keys in Active Directory | Manually manage keys |
| File Sharing | Can share encrypted files with other users | Can share encrypted files securely |
| Portability | Limited to Windows systems | Cross-platform compatibility |
| Additional Features | BitLocker To Go for USB drives | Secure file deletion, cloud storage integration, key sharing |
| Open Source | Closed source | Closed source |
6. Cryptomator: Put a lock on your cloud
The Cryptormator is an open-source encryption tool used on Windows 10, 8,7, and Mac OS operating systems.
It provides you with client-side encryption alongside transparent encryption that has no backdoors. With the Cryptomator, file-based encryption can be done with the help of the AES algorithm.
It guarantees the protection of any file filled with data stored on a server or cloud.
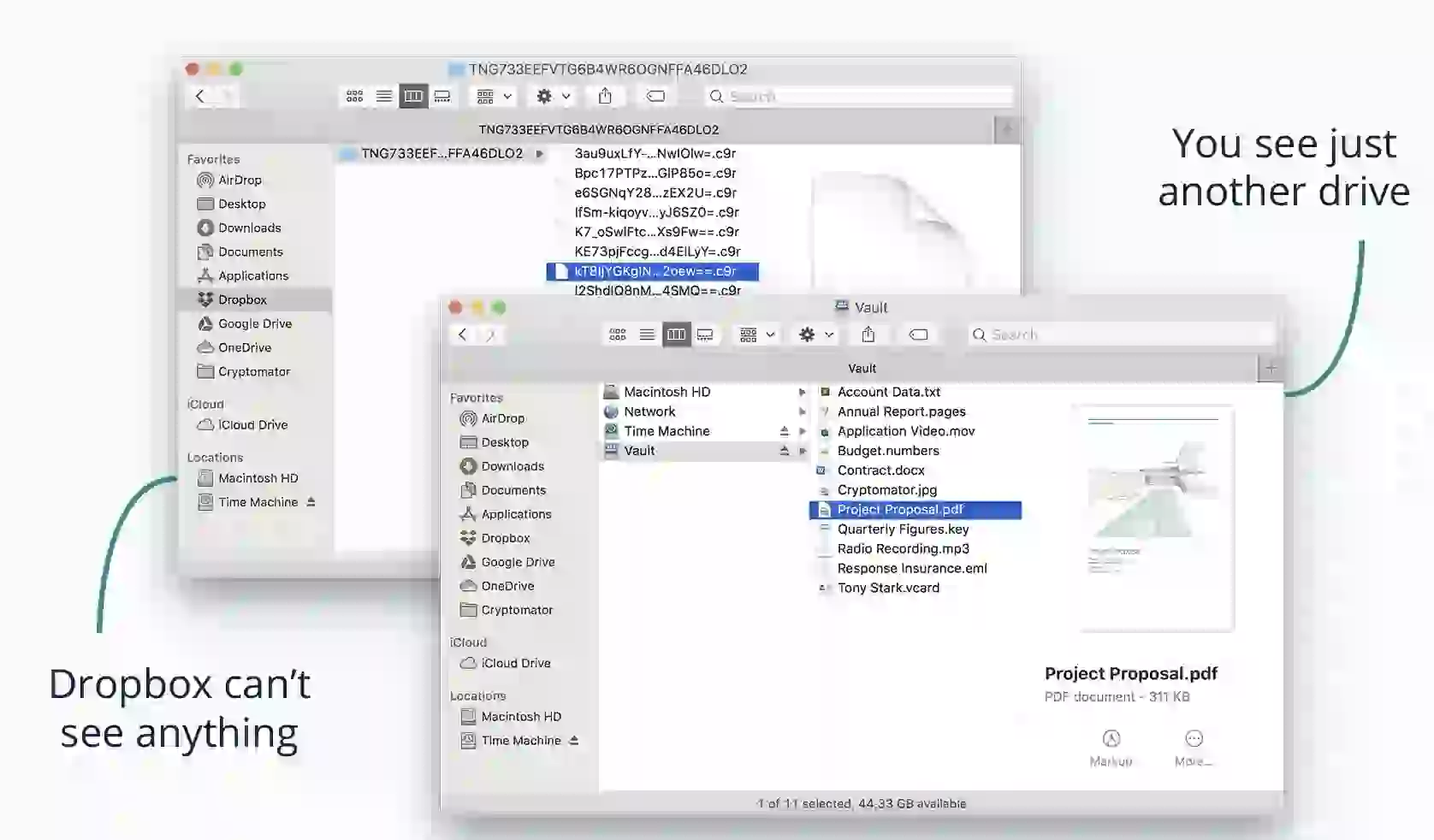
Cryptomator helps you with the name of file encryption and directories. These directories are personified and become useless for other people to use.
Even though the Crptomator is one of the best options you can opt for to protect your data, it has a limitation.
It may not be very easy at times to delete a Cryptomator file. A solution has not been proffered for this limitation, but developers are doing ongoing research and work to fix this problem.
Features:-
Here’s a table outlining the features of Cryptomator, an open-source file encryption software:-
| Feature | Description |
|---|---|
| Client-side Encryption | Cryptomator encrypts your files locally on your device before uploading them to any cloud storage provider. This ensures your data remains encrypted and secure even when stored on third-party servers. |
| Zero-Knowledge Principle | Cryptomator follows the zero-knowledge principle, meaning only you can access the encryption keys and passwords. The software does not have access to your data, providing additional privacy and security. |
| Transparent File Access | You can access your encrypted files seamlessly through virtual drives or folders, as Cryptomator integrates with your operating system. This allows you to work with your files as you would normally, without any additional steps. |
| Cross-Platform Compatibility | Cryptomator is available for various operating systems, including Windows, macOS, Linux, Android, and iOS, making it convenient to use across different devices and platforms. |
| File Versioning | Cryptomator follows the zero-knowledge principle, meaning only you can access the encryption keys and passwords. The software cannot access your data, providing additional privacy and security. |
| Two-Factor Authentication | To enhance security, Cryptomator offers two-factor authentication (2FA). You can enable 2FA to provide an additional layer of verification when accessing your encrypted files. |
| Open-Source | Cryptomator supports file versioning, allowing you to restore previous versions of your encrypted files. This feature can be useful in case of accidental modifications or if you need to retrieve an older file version. |
7. CipherShed – Free BitLocker alternatives
CipherShed is free software specifically for encryption. It provides files and drive protection on your system. It has similar features to another software called TrueCrypt.
It gives you a transparent kind of encryption with an easy-to-use interface. Any file you encrypt with this software can be stored anywhere and accessed when needed.
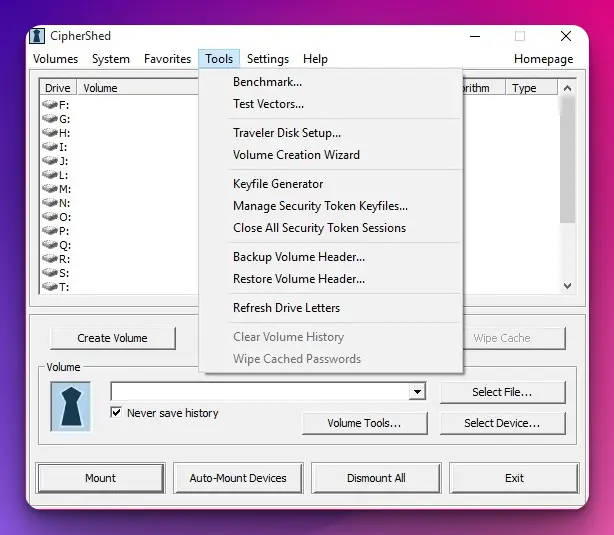
Aside from the easy storage method, the files can be easily transferred without fear of losing part of the stored data.
The CipherShed is supported on Windows and Mac OS operating systems, and files can be transferred from one of the operating systems to the other without difficulties. This is a budget-friendly tool, so you should try this BitLocker alternative.
8. AES Crypt
This software is supported on Windows 32 and 42 bits. It can also be used on Mac OS, Linux, and Android.
The AES Crypt is great for protecting your files as it uses 256 bits encryption and the AES encryption algorithm.
It is user-friendly and would be a recommendation regardless of the user’s experience to encryption tools. To protect a file on your system, right-click on the file, select the encrypt option, and provide a password.
By doing this, your file is protected. Follow the same process to get the original information.
One great feature of the AES Crypt software is that no extension is added to the file name. Every single thing remains the same as it was before encrypting the file.
Compared to other encryption software, the AES Crypt may be slower. Encryption passwords should be kept safe as you need them for files you want to encrypt.
9. Sophos Safeguard
The Sophos Safeguard has a 30 days free usage policy; afterward, you begin paying as you use the software. Sophos Safeguard uses its encryption methods on its interface and adopts BitLocker and MAC encryption methods.
It is possible to connect to a server via HTTPS. HTTPS software gives external users access to servers, and you can see the real stored files and open them.
Sophos Safeguard has key group features that let a group of users have permission to use some important files.
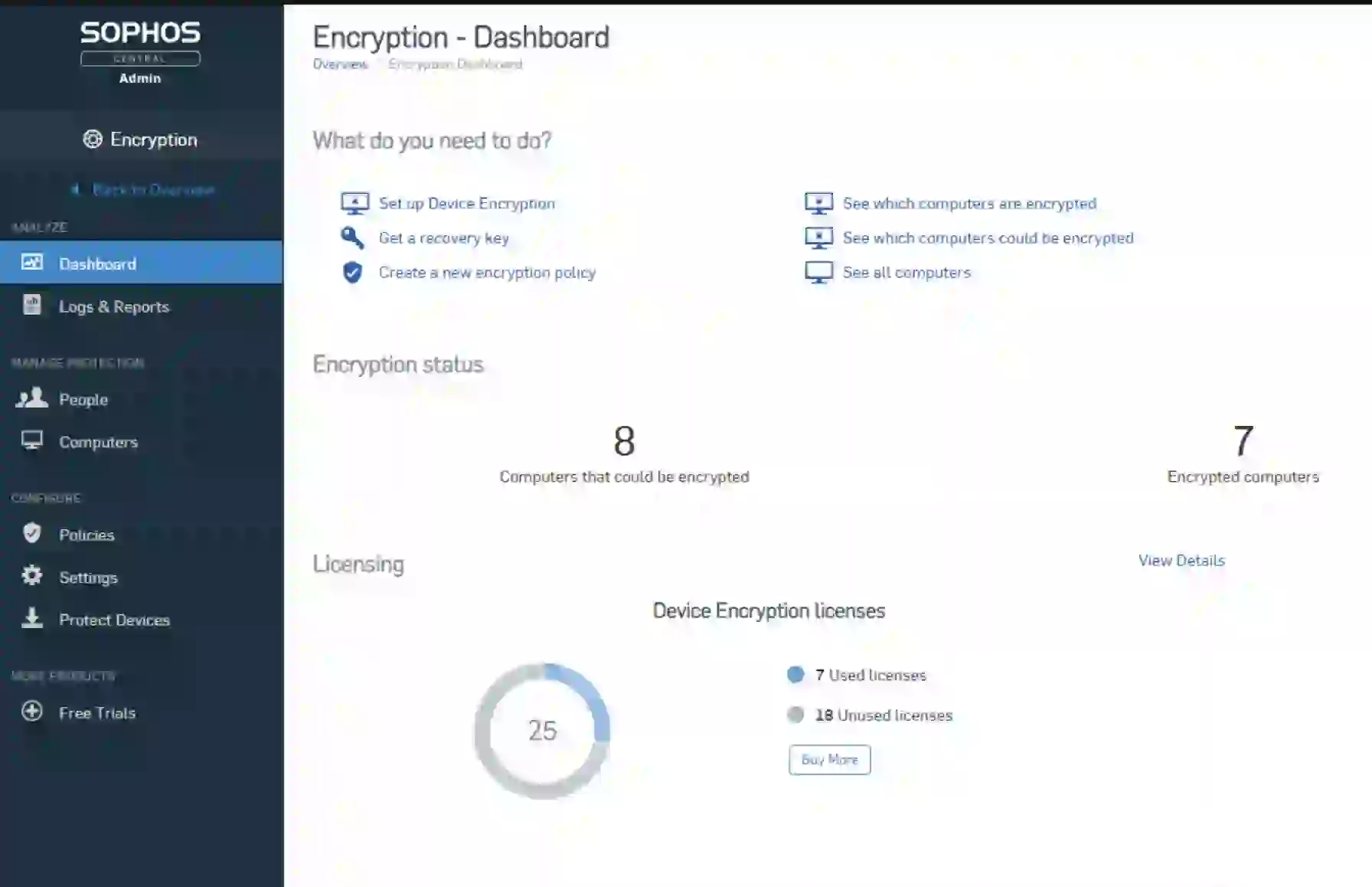
It helps you detect threats that are harmful to your system. Once the threat is found, each one of the encryption keys gets automatically deleted from the ‘Keyring’ until the threat is fixed.
This software is a reliable source of protection for your files and system. It gives offers you encryption options for both whole disks and partitions.
BitLocker vs Sophos Safeguard:-
BitLocker is a good option for basic encryption needs, while SafeGuard is a more advanced solution for organizations that require more granular control over their encryption policies and key management.
Here’s a comparison table highlighting some key features and differences between BitLocker and Sophos Safeguard:-
| Feature | BitLocker | Sophos Safeguard |
|---|---|---|
| Encryption Algorithm | AES (128-bit or 256-bit) | AES (256-bit) |
| Operating Systems | Windows | Windows, macOS, Linux (limited functionality) |
| Central Management | Microsoft Endpoint Manager (formerly SCCM) | Sophos Central Console |
| Pre-Boot Authentication | Available | Available |
| Self-Encrypting Drives | Supported | Supported |
| Removable Media | Supported | Supported |
| Key Management | Active Directory or Azure AD | Sophos Central or Sophos Enterprise Console |
| Recovery Options | Recovery key, TPM, Active Directory recovery | User-based, Local recovery key, Helpdesk recovery |
| Device Compliance | Limited control over non-Windows devices | Comprehensive control over multiple OS platforms |
| Reporting and Auditing | Limited | Detailed reporting and auditing capabilities |
| Integration | Seamless integration with Windows ecosystem | Integration with Sophos security solutions |
| Price | Included with Windows Pro and Enterprise editions | Subscription-based pricing model |
10. Jetico BestCrypt Volume Encryption
This is one of the best-paid BitLocker alternatives if you normally use a paid encryption tool to protect your computer.
It cares for a Windows data encryption part of your system by offering maximum security while supporting all other algorithms like the AES, Serpent, and Twofish.
The Jetico BestCrypt permits users to access the encrypted states of full disks and partitions from a single screen.
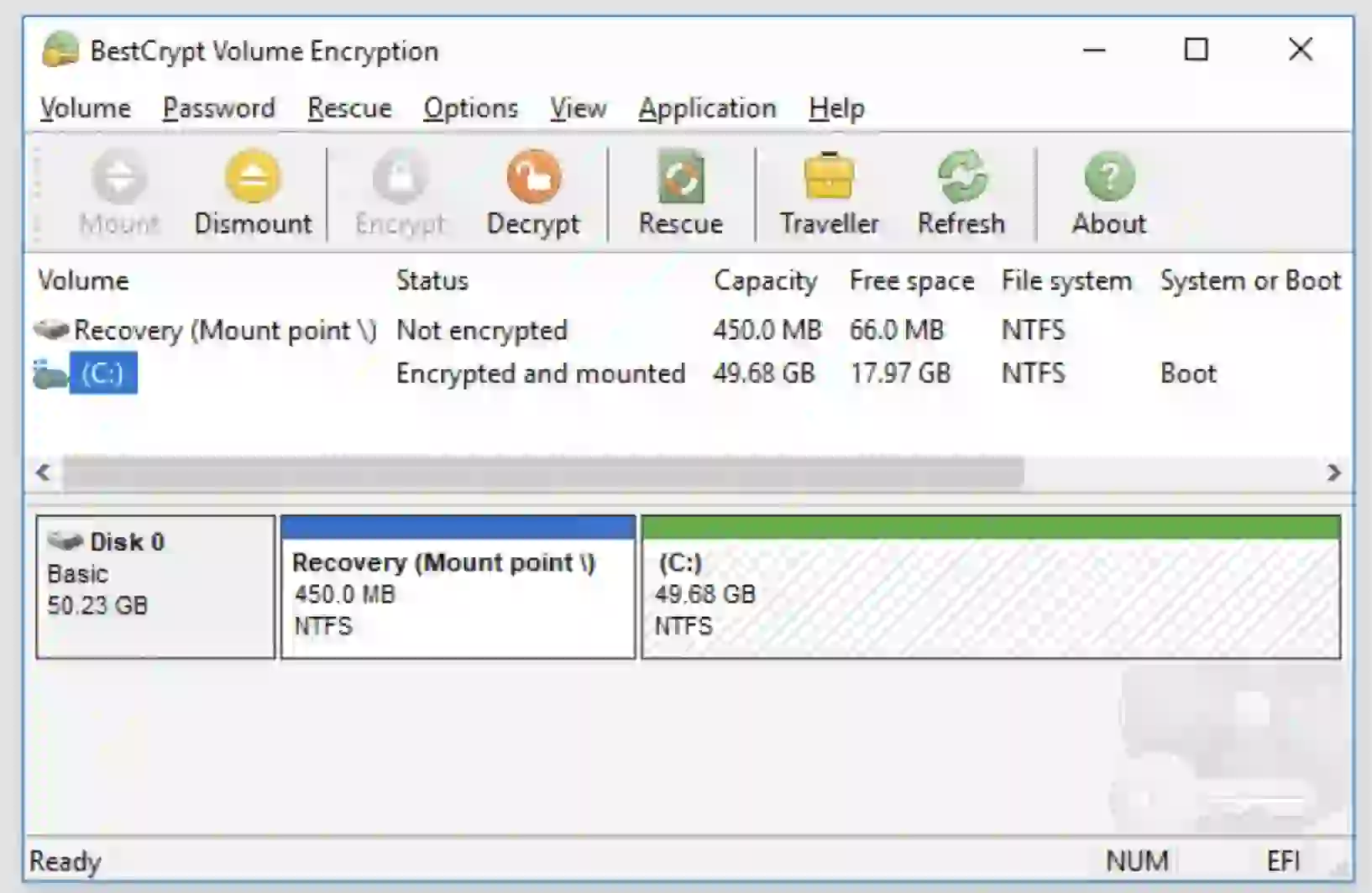
The software can control all the Jetico BestCrypt volume from one login process but with the assistance of two-factor authentication. It also has preboot authentication if you are interested in using it.
It gives you the optimum protection you may desire with a price tag. Well, nothing good comes easily. It can be used on Mac. Linux and a Windows operating system with ease.
11. FileVault
FileVault software’s encryption is very secure for all types of files. It runs on all Apple devices and is user-friendly.
You do not necessarily need to know how to use it because its user interface is easy to navigate.
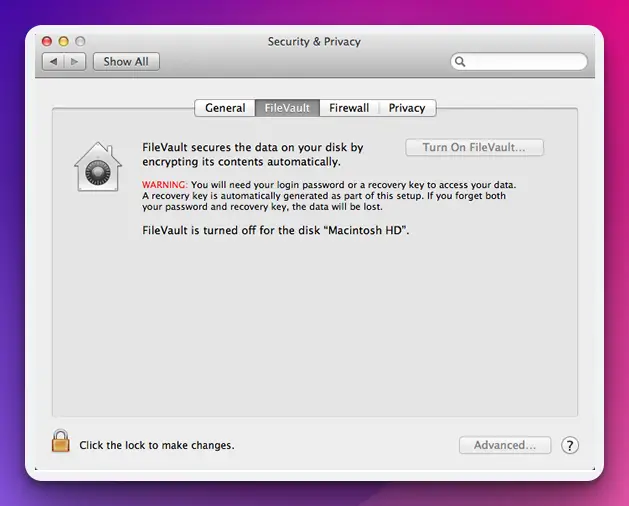
You can encrypt your file, folder, image, document, or whatever you want. Its high-level security protection will protect your documents using this software in the simplest ways without complications.
Sometimes, FileVault may affect the function of other applications on the system where it is installed. This is a well-documented limitation of this BitLocker alternative.
12. Symantec Endpoint Encryption
Symantec Encryption combines a strong full-disk and removable media encryption with centralized management that guards sensitive information, ensuring regular compliance.
This software provides users with the best security encryption. It does this by encrypting each file by compartments. It also supports endpoint encryption to laptops and desktops, which uses several types of removable media such as external hard drives, USBs, CDs, etc.
With Symantec, you can access your encrypted files on any Windows and Mac operating system, even if the software has not been installed.
BitLocker vs Symantec Endpoint Encryption:-
BitLocker may be a good choice for organizations that use Windows operating systems exclusively, while Symantec Endpoint Encryption may be a better fit for those that need more advanced encryption features and multi-platform support.
Here’s a table comparing BitLocker and Symantec Endpoint Encryption:-
| Feature | BitLocker | Symantec Endpoint Encryption |
|---|---|---|
| Encryption Method | AES (Advanced Encryption Standard) | AES, RSA, Blowfish, Twofish, etc. |
| Operating System Support | Windows | Windows, macOS, Linux |
| Management Console | Microsoft Endpoint Manager (formerly SCCM) | Symantec Endpoint Protection Manager |
| Authentication Methods | TPM, PIN, USB Key, Network Unlock, Active Directory integration | User password, smart cards, tokens, biometrics |
| Pre-Boot Authentication | Yes | Yes |
| Full Disk Encryption | Yes | Yes |
| Removable Media Encryption | Yes | Yes |
| Centralized Management | Yes | Yes |
| Reporting and Auditing | Limited | Comprehensive |
| Compliance Support | FIPS 140-2, HIPAA, GDPR, etc. | FIPS 140-2, HIPAA, GDPR, etc. |
| Third-Party Integration | Limited | Extensive |
| Cost | Included with Windows | Subscription-based |
13. ESET Endpoint Encryption
ESET Endpoint Encryption is a well-structured security app that gives optimum protection for your files at rest or in transit.
All of its editions offer file encryption, folder encryption, and email encryption and can compress archives, encrypt virtual disks, and add a shredder for desktops to secure file deletion.
It has an exceptional intuition for user experience, making it easy to navigate through its interface.
The ESET Endpoint Encryption is a simple-to-use, powerful data encryption tool that provides full disk encryption and encryption for every other file you want to be protected.
Its unique key system encryption shows that protection is highly secure and practical. You don’t need a password whenever you want to share encrypted media.
This is one of the most amazing BitLocker alternatives you should try if you are searching for a great and powerful encryption tool for your system.
BitLocker vs ESET Endpoint Encryption:-
BitLocker is primarily focused on full-disk encryption for Windows operating systems. At the same time, ESET Endpoint Encryption offers more comprehensive encryption capabilities across multiple platforms and supports various encryption options beyond just full-disk encryption.
Here’s a comparison table between BitLocker and ESET Endpoint Encryption:-
| Features | BitLocker | ESET Endpoint Encryption |
|---|---|---|
| Encryption Method | AES (Advanced Encryption Standard) | AES (Advanced Encryption Standard) or Triple DES |
| Full Disk Encryption | Yes | Yes |
| File-Level Encryption | No | Yes |
| Pre-Boot Authentication | Yes | Yes |
| Centralized Management | Yes | Yes |
| Password Complexity | Limited (password only) | Flexible (password, smart card, token, etc.) |
| Multifactor Authentication | No | Yes |
| Platform Compatibility | Windows only | Windows, macOS, and Linux |
| Data Recovery | Recovery Key or Recovery Password | Recovery Key or Recovery Password |
| Key Management | Active Directory Integration | Centralized Key Management |
| Integration with Antivirus | No | Yes |
| Compliance Support | Limited (Windows enterprise editions) | Yes |
| Performance Impact | Minimal | Minimal |
| Cost | Included with Windows Pro and Enterprise editions | Commercial licensing based on the number of seats |
14. Kaspersky Endpoint Security
This Bitlocker alternative is especially for businesses. It provides a flexible security option for a mixed kind of environment. It incorporates joint building blocks to automate threat defense and systems hardening automatically.
This security tool is recognized and awarded as one of the security apps powered by next-generation technology to protect every Windows endpoint, including the data they carry.
Kaspersky Endpoint Security allows businesses to protect their data stored on a network or in the cloud from cyber attacks.
This tool has a free business trial that a user can use as a stepping stone to getting familiar with the interface. However, it has a user-friendly interface where you can easily navigate and access data and files.
You should give the Kaspersky Endpoint Security a trial and let it perform the magic it does by providing you with one of the most advanced security encryption you can find.
15. Dell Data Protection
Dell Data Protection is a series of applications that lets you find data security risks on your desktops, laptops, and external media storage. It encrypts sensitive information and enforces control policies and authentication.
This security tool has easy compliance management with a quick recovery system. With it, system disk and port encryption can be in a single solution without worrying about lost data.
It offers you the protection and security you need by supporting Microsoft’s built-in full encryption policies that you know as BitLocker. It gives you complete encryption volume and several ways to secure your operating system from cyber attacks.
16. Dm-crypt
Dm-crypt is an encrypting subsystem visible in versions 2.6 and later of the Linux kernel, as well as in DragonFly BSD. It utilizes cryptographic methods from the kernel’s Crypto API and is a DM (device-mapper) architecture component.
It differs from Cryptoloop, in that it was built to prevent watermarking attacks by supporting sophisticated modes of operation like LRW, XTS, and ESSIV. Dm-crypt solves some of Cryptoloop’s dependability issues.
Dm-crypt is a device-mapper target that may be used with other device mappers. As a result, it may encrypt whole drives (including portable media), software RAID volumes, partitions, data, and logical volumes. It displays as a block device that can act as an LVM physical volume or backup file system.
Regarding the root file system, several Linux versions enable dm-crypt usage. Before the usual boot process, these distributions utilize initrd to ask the user to provide a password at the console or insert a smart card.
Choosing the Right BitLocker Alternative
When securing your data, exploring BitLocker alternatives can provide additional options tailored to your needs.
To ensure you choose the right alternative, it’s essential to consider various factors before deciding.
First and foremost, encryption strength is a crucial aspect to evaluate.
Look for alternatives that offer robust encryption algorithms, such as AES-256 or Twofish, to ensure your data remains highly secure. Encryption strength directly impacts the level of protection your chosen alternative can provide.
Platform compatibility is another vital consideration. Evaluate whether the alternative solution supports your operating system, especially if you have a mixed environment.
Look for options that offer cross-platform compatibility across Windows, macOS, and Linux, enabling you to secure your data consistently across different systems.
User-friendliness is key, so opt for an alternative that offers an intuitive and easy-to-use interface. This ensures a smooth transition and minimizes the learning curve.
The alternative should provide a seamless experience for creating encrypted volumes or drives and managing access to your protected data.
Additionally, consider the level of community support and the development status of the alternative.
Active communities and ongoing development indicate a vibrant user base and a commitment to addressing potential issues and enhancing the solution’s features.
By carefully considering these factors, you can choose the right BitLocker alternative that aligns with your specific requirements, offering enhanced data security and peace of mind.
Implementing and Using BitLocker Alternatives
When securing your data, implementing and using BitLocker alternatives provides flexible options to protect sensitive information.
To effectively utilize these alternatives, follow these essential steps.
First, choose a suitable BitLocker alternative based on your specific requirements.
Conduct thorough research and select an alternative that aligns with your desired encryption strength, platform compatibility, and user-friendliness.
Once you’ve chosen an alternative, begin the implementation process.
Install the alternative software on your system and follow the instructions for setup and configuration. Ensure you understand the encryption options and customize the settings according to your needs.
Launch the alternative software and select the desired storage location to create encrypted volumes or drives. Follow the instructions to initialize the encryption process and set up a strong password or utilize other authentication methods supported by the chosen alternative.
Managing and accessing encrypted data is crucial for a seamless experience. Make sure to familiarize yourself with the alternative software’s user interface and its functionalities.
Explore features such as mounting encrypted volumes, changing passwords, or managing access permissions.
If you encounter any issues or difficulties during implementation or usage, refer to the alternative’s documentation, user forums, or customer support for assistance. These resources can provide valuable insights and solutions to common challenges.
By following these steps, you can successfully implement and use BitLocker alternatives to confidently safeguard your data, enhancing your overall data security and maintaining control over your sensitive information.
BitLocker alternatives For Android
BitLocker is a Windows-specific encryption tool that is not available for Android.
However, there are several encryption tools that you can use as alternatives to BitLocker on Android, like VeraCrypt, Crypt4All Lite (AES), AxCrypt, SSE Universal Encryption, and Encrypto.
Here’s a table comparing some popular BitLocker alternatives for Android:-
| Tool Name | Description | Encryption Algorithm | Price |
|---|---|---|---|
| VeraCrypt | Open-source encryption tool for files, partitions, and devices | Various, including AES and Twofish | Free |
| Crypt4All Lite (AES) | Simple app for encrypting and decrypting files and folders | AES-256 | Free |
| AxCrypt | Popular encryption tool for individual files and folders | AES | Free, with a paid upgrade option |
| SSE Universal Encryption | Open-source encryption tool supporting various algorithms | Various, including AES, Blowfish, and Twofish | Free |
| Encrypto | Simple encryption tool for files and folders | AES-256 | Free |
Open Source BitLocker alternatives
If you’re looking for an open-source alternative to BitLocker, VeraCrypt, LUKS,dm-crypt, OpenPGP, and Cryptsetup is one.
Here’s a table comparing some of the key features of open-source BitLocker alternatives:-
| Software | Platforms | Encryption Type | Key Management | User Interface |
|---|---|---|---|---|
| VeraCrypt | Windows, Mac, Linux | AES, Serpent, Twofish | Password, Keyfile, Smart card | GUI, command line |
| LUKS | Linux | AES, Twofish, Serpent | Password, Keyfile | Command line |
| dm-crypt | Linux | AES, Twofish, Serpent | Password, Keyfile | Command line |
| OpenPGP | Windows, Mac, Linux | AES, Twofish, CAST5, Triple DES | Public-key cryptography | GUI, command line |
| Cryptsetup | Linux | AES, Twofish, Serpent | Password, Keyfile | Command line |
Linux Bitlocker Alternatives
There is no direct equivalent to BitLocker in Linux; alternative solutions offer similar functionality.
LUKS (Linux Unified Key Setup),dm-crypt, VeraCrypt, and EncFS are a few options.
Here is a table that compares some popular Linux Bitlocker alternatives:-
| Software Name | License | Encryption Algorithm | Key Management | Cross-Platform Support |
|---|---|---|---|---|
| VeraCrypt | Open Source | AES, Serpent, Twofish | Password, Keyfile, Token | Windows, macOS, Linux |
| dm-crypt/LUKS | Open Source | AES, Serpent, Twofish | Password, Keyfile | Linux |
| Cryptsetup | Open Source | AES, Serpent, Twofish | Password, Keyfile | Linux |
| EncFS | Open Source | Blowfish, AES | Password | Windows, macOS, Linux |
| TrueCrypt | Discontinued | AES, Serpent, Twofish | Password, Keyfile, Token | Windows, macOS, Linux |
📗 FAQs on BitLocker alternatives
What can I use instead of BitLocker?
Some popular options include VeraCrypt, DiskCryptor, and 7-Zip. These tools offer similar functionality to BitLocker and provide robust encryption for your data.
Here’s a table comparing BitLocker with some alternative encryption solutions:-
| Encryption Solution | Description | Compatibility | Platform | Open Source | Key Features |
|---|---|---|---|---|---|
| VeraCrypt | A free, open-source disk encryption software based on TrueCrypt. | Windows, macOS, Linux | Cross-platform | Yes | Hidden volumes, encryption of entire system drive, various encryption algorithms. |
| FileVault | Native disk encryption tool for macOS. | macOS | macOS | No | Full-disk encryption, automatic encryption of user data, integration with Apple devices. |
| LUKS | Linux Unified Key Setup, a disk encryption specification for Linux. | Linux | Linux | Yes | Full-disk encryption, key management, multiple encryption algorithms. |
| Symantec Endpoint Encryption | A comprehensive encryption solution for enterprise environments. | Windows | Windows | No | Centralized management, full-disk encryption, removable media encryption, compliance reporting. |
| DiskCryptor | Free open-source encryption software for Windows. | Windows | Windows | Yes | Full-disk encryption, boot loader, multiple encryption algorithms, portable mode. |
| AES Crypt | Cross-platform file encryption software. | Windows, macOS, Linux | Cross-platform | Yes | Simple file encryption/decryption, integration with file managers, command-line support. |
How to encrypt Windows without BitLocker?
If you prefer not to use BitLocker, consider using third-party encryption software like VeraCrypt or DiskCryptor. These tools offer similar encryption capabilities and can help you secure your Windows system and data.
Is BitLocker obsolete?
No, BitLocker is not considered obsolete. It is still a widely used and trusted encryption solution for Windows operating systems. Microsoft continues to support and enhance BitLocker, ensuring its compatibility with newer Windows versions and providing updates to address any security vulnerabilities that may arise.
Why not to use BitLocker?
While BitLocker is a reliable encryption tool, some users may have specific reasons for not using it. One reason could be the edition of Windows they are using, as BitLocker is only available in certain versions of Windows.
Additionally, some users might prefer open-source alternatives like VeraCrypt or DiskCryptor due to their transparency and the ability to audit the source code.
Is VeraCrypt still secure?
Yes, VeraCrypt is still considered a secure encryption solution. It is a fork of the original TrueCrypt project and has undergone independent security audits, which have not revealed any major vulnerabilities.
Is BitLocker the best encryption?
BitLocker is a reputable and widely used encryption tool, but whether it is the best encryption solution depends on your specific needs and preferences.
Alternatives like VeraCrypt and DiskCryptor offer similar functionality and may be considered better by some users due to their open-source nature or additional features.
How to encrypt Windows 11 without BitLocker?
In Windows 11, if you prefer not to use BitLocker, you can still encrypt your system using third-party encryption software like VeraCrypt or DiskCryptor.
These tools provide encryption capabilities similar to BitLocker. You can download and install the chosen software, follow their instructions to create an encrypted container or encrypt specific drives/partitions, and set up a strong password or passphrase for the encryption.
How do I start my laptop without BitLocker?
If your laptop has BitLocker enabled, you must enter the correct BitLocker recovery key or password during the boot process to start your laptop.
If you want to bypass BitLocker, temporarily suspend the protection by accessing the BitLocker settings in the Control Panel or using the “manage-bde” command in Command Prompt with administrative privileges.
How to lock external hard disk with password without BitLocker?
To lock an external hard disk with a password without using BitLocker, you can utilize third-party software like VeraCrypt or other file encryption tools.
These tools allow you to create an encrypted container or encrypt the external hard disk with a password. Once encrypted, the external hard disk will require the correct password to access its contents.
What is the downside of BitLocker encryption?
One drawback is that BitLocker is only available on certain editions of Windows, so users with unsupported editions may need to explore alternative encryption options.
Additionally, BitLocker requires a Trusted Platform Module (TPM) chip on the computer or the use of a USB drive for authentication, which may not be available on all systems. Finally, if you forget your BitLocker password or lose the recovery key, it can be challenging to recover your encrypted data.
here’s a table outlining some potential downsides of BitLocker encryption:-
| Downside of BitLocker Encryption | Description |
|---|---|
| Compatibility Issues | BitLocker encryption is only available on certain versions of Windows, and it may not be compatible with some older computers or devices running other operating systems. This can limit its usefulness in certain situations. |
| Performance Impact | If a BitLocker-encrypted drive becomes corrupted or fails, it can be difficult or impossible to recover the stored data. Additionally, if a user forgets their password or loses their encryption key, they may not be able to access their data. |
| Recovery Issues | If a BitLocker-encrypted drive becomes corrupted or fails, it can be difficult or impossible to recover the stored data. Additionally, if a user forgets their password or loses their encryption key, they may be unable to access their data. |
| Potential Security Vulnerabilities | BitLocker encryption can slow down a computer’s performance, particularly if running on older or slower hardware. This may be particularly noticeable when reading or writing large files or performing other disk-intensive tasks. |
| Limited Protection | BitLocker encryption only protects data when the computer or device is powered off or in an otherwise secure state. If an attacker gains access to a running system, they may still be able to access unencrypted data. Additionally, if an attacker gains physical access to the drive and can remove it from the system, they may be able to bypass the encryption altogether. |
Does Windows 11 enforce BitLocker?
Windows 11 includes BitLocker encryption as part of its security features. However, whether BitLocker is enforced or enabled on a Windows 11 system depends on various factors, including the edition and configuration of Windows 11 that you are using.
Does Windows 11 automatically encrypt the hard drive?
Windows 11 does not automatically encrypt the hard drive by default. While BitLocker encryption is available in Windows 11, it requires manual configuration and activation to encrypt the hard drive.
Why is BitLocker not available in Windows 11?
BitLocker is available in certain Windows 11, but its availability may vary depending on your specific edition. Microsoft reserves BitLocker for specific editions, such as Windows 11 Pro and Windows 11 Enterprise.
Suppose you are using Windows 11 Home Edition or other editions that do not include BitLocker. In that case, you may need to explore alternative encryption options like third-party software or upgrading to a compatible edition that supports BitLocker.
Will a factory reset remove BitLocker?
Performing a factory reset on a device that has BitLocker encryption enabled will not remove BitLocker or decrypt the encrypted data.
BitLocker encryption is tied to the hardware and operating system, unaffected by a factory reset. After the reset, if you want to access the device, you must provide the correct BitLocker recovery key or password to unlock the encrypted data.
What happens if you skip BitLocker?
If you skip the BitLocker encryption setup on your Windows computer, the hard drive or data will remain unencrypted, and it will not benefit from the added security that BitLocker provides.
Without BitLocker encryption, your data will be more vulnerable to unauthorized access if the device is lost, stolen, or accessed by an unauthorized individual.
Is there a downside to using BitLocker?
Bitlocker is one of the best tools for Windows users to encrypt the drive. However, it lacks in performance at times, such as your system getting slower than usual, slow process of encryption and decryption, and other issues.
Furthermore, you need to keep the recovery key in the right place, or you might lose all your data.
Can I buy BitLocker for Windows 10 home?
Bitlocker is only available for Windows Professional and not for any other version of Windows OS. If you already have a Professional version of Windows, you can use all the services for free and keep your data secure.
However, if you are using Windows 10 Home, you need to upgrade to Windows Professional, which will cost you a hefty amount.
How good is VeraCrypt?
VeraCrypt is known to be the best alternative to Bitlocker. The best part is that it is an open-source tool, and you can get it free for every user.
Moreover, it encrypts your drive where Windows is installed and allows no backdoor access. Furthermore, you can download it on your Windows, macOS, and even Linux operating system.
Can I use EFS with BitLocker?
There is a huge advantage of using both tools together. While Bitlocker will keep your entire operating system drive encrypted and safe from attacks, EFS will ensure that the file encryption is activated for different users on the same computer. EFS is perfect for keeping all the other files encrypted, which Bitlocker does not secure.
Is EFS Windows 10 compatible?
EFS is only available on Windows 10 Pro, Enterprise, and Education versions. If you already have these installed, you can use this encryption tool’s features.
However, for Windows 10 Home users, you must upgrade to the above version to use EFS or even Bitlocker for free.
Final Thoughts on BitLocker Alternatives
In conclusion, it’s crucial to consider your specific needs and requirements when it comes to finding suitable alternatives to BitLocker.
While BitLocker offers robust encryption capabilities for Windows users, alternative solutions may better align with your preferences or business objectives.
You can discover alternatives that offer features like cross-platform compatibility, enhanced security measures, user-friendly interfaces, or additional functionality by exploring various options.
When deciding, remember to assess factors such as ease of implementation, scalability, cost-effectiveness, and ongoing support.
Whether you opt for open-source solutions like VeraCrypt or AxCrypt, or choose commercial alternatives such as Symantec Endpoint Encryption or DiskCryptor, a wide range of options are available to safeguard your sensitive data.
It’s essential to thoroughly evaluate each alternative and consider how well it fits your organization’s unique needs.
Ultimately, the most important aspect is prioritizing protecting your data and ensuring that any alternative offers reliable encryption, ease of use, and ongoing support.
By doing so, you can confidently secure your files and maintain the privacy and confidentiality of your information, mitigating the risks associated with unauthorized access or data breaches.
Make an informed decision, explore the alternatives, and find the one best suits your requirements.
By taking proactive steps to secure your data with a reliable BitLocker alternative, you can fortify your digital defenses and establish a robust foundation for protecting your valuable information.