Are you prepared to advance your Linux knowledge? We’ll cover advanced hints and techniques in this article so you can control file permissions like a pro by using the chmod command.
We’ll go over everything you need to know about using the chmod command proficiently, from setting custom permissions to operating recursively.
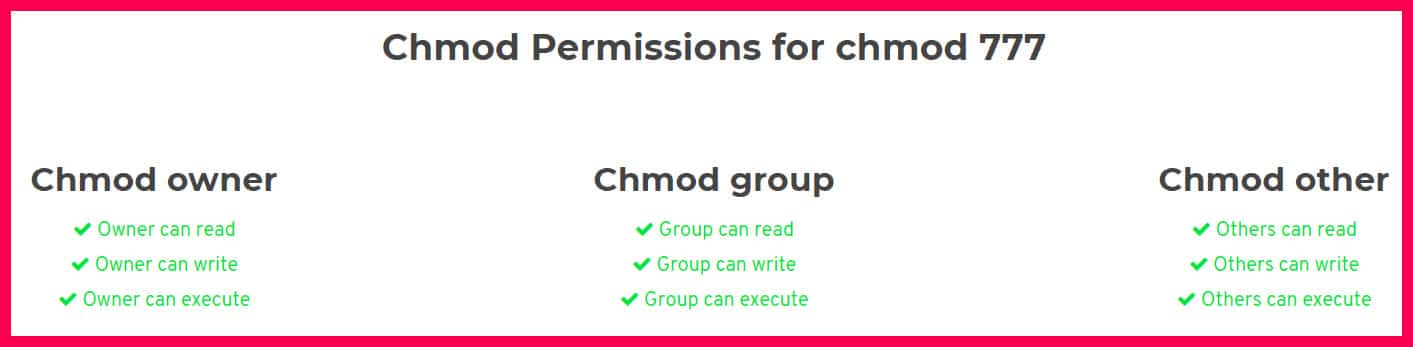
This review presupposes that you’ve come across the term “Chmod 777” before, it will be explained in simple and concise ways.
This review will explain what it is, what it does, how to use it, where to use it, and generally other information relating to the term.
You may have encountered the term while trying to fix a permission issue on your web server. The solution offered might have been for you to “chmod 777” the web directory recursively.
This might solve the problem but then it opens you up to other issues that you might not be aware of unless you’re well informed about what Chmod 777 does exactly.
Maybe you’re a web owner whose website is hosted on a Linux server. You tried accessing or modifying a document and you were repulsed by the statement “you do not have permission to upload a file to the folder”.
After searching for help, you learn that the solution is to change the file permission to ” 777″. This seems easy enough but there are underlying issues why we should know more before making modifications.
What is Chmod?
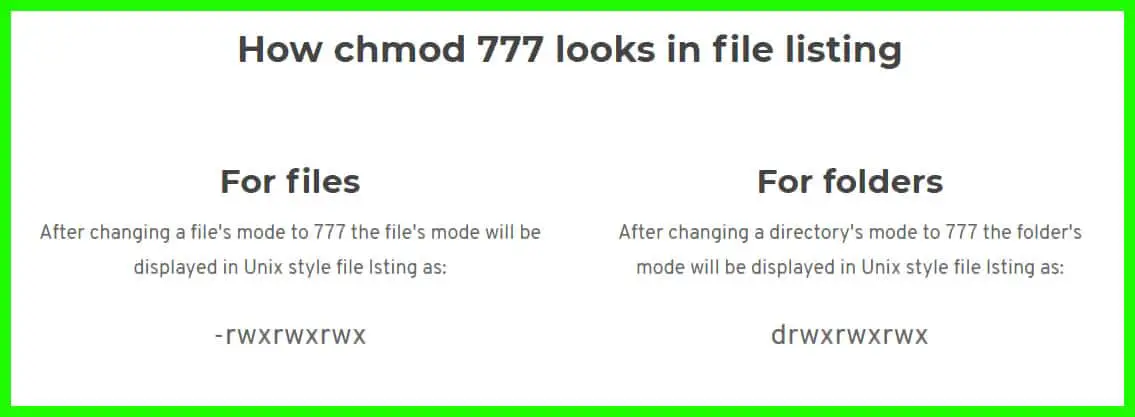
In Unix systems, there is a mechanism that deals with file controls. Chmod is a command used to change those file permissions and controls in terminals. It allows or disallows modifications of the file.
Understanding Linux systems help secure your system by restricting access to your files. Chmod 777 is one of those file control mechanisms. More of a permission mechanism, though. There are two parts (of file control mechanisms).
- Classes
- Permissions
Classes:-
Underneath this group, there are 3 subgroups. There’s usually the “Owner”, the “Group” and “Others”.
The Owner is usually the one with all the permissions to modify at will any file. The Group is a bunch of people given access by the Owner to modify or just view files depending on the level of access granted by the Owner.
Others are guests basically, their level of access is also restricted or loosened by the Owner.
Permissions:-
There are 3 actions you can initiate on files. They are
Read – Access is only limited to reading files. Modifying the file is restricted. When applied to folders, viewing files inside the folder is allowed but any other action like adding or deleting files to the folder is restricted.
Write – Reading the files, editing the files and modifying the files are allowed. Folders with this permission can have files removed from them and other files added.
Execute – Major usage is in running files. Examples are Scripts. Another explanation is that the file directory can be entered using the CD command.
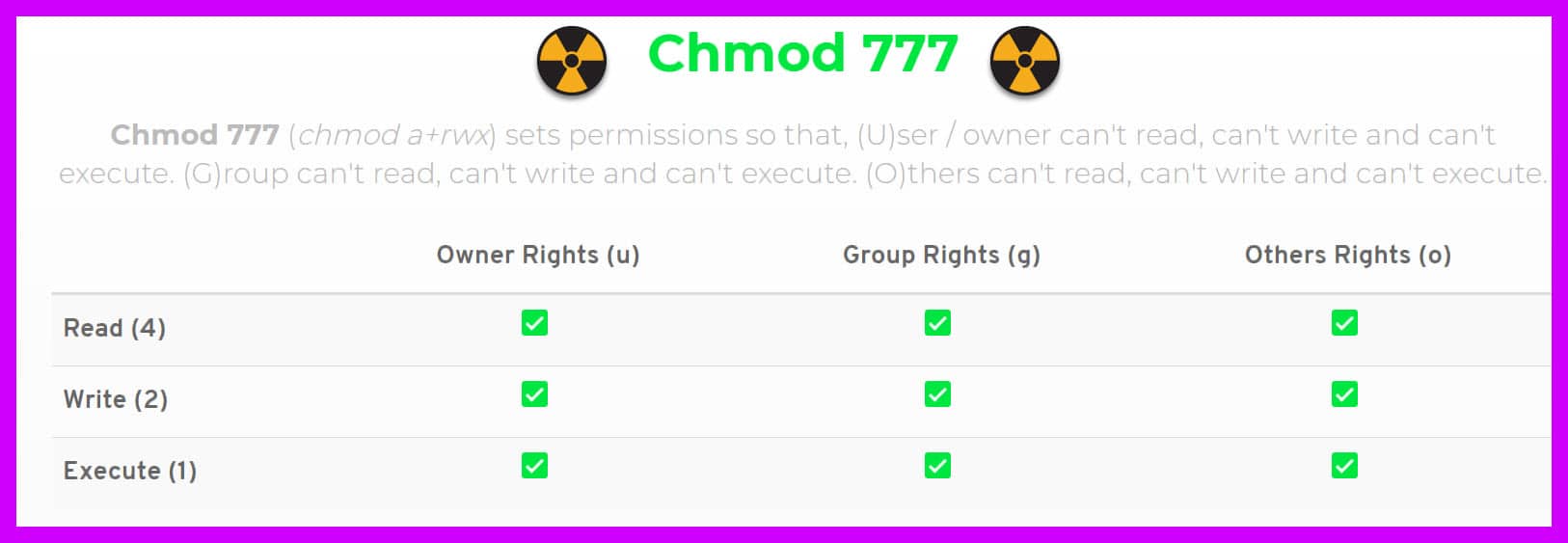
What is the meaning of “777” in Chmod 777? 🤔
Did you make it thus far, understanding every step? Then let’s continue.
These numbers represent restrictions or access depending on the numbers. An 8-bit binary controls files or folders access.
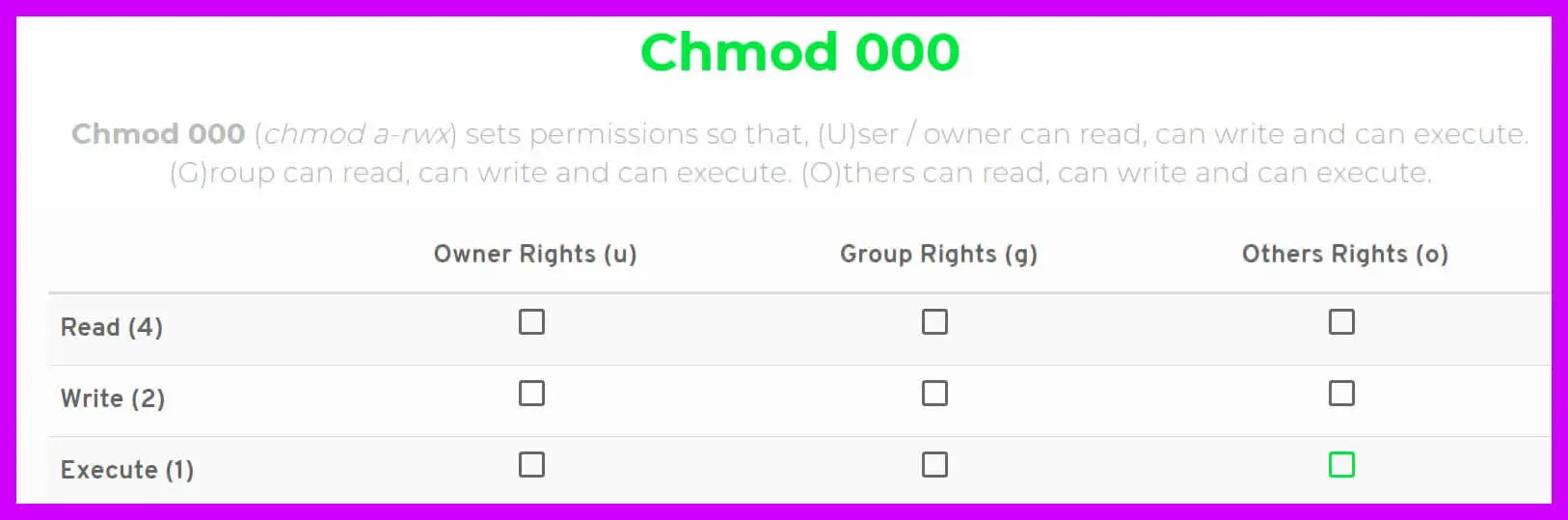
In its original or basic form, (000), it signifies no access. No modification or reading or execution is allowed at all.
Here’s something vital you need to know, while in basic binary form, there are only numbers 0 and 1. So if “000” means no permission is given to all classes in its basic form, then “111” will mean all permissions are given to all classes. But in a decimal format, these are the designated numbers of the permissions.
“Read“ is represented by the number 4
“Write“ is represented by the number 2
“Execute“ is also represented by a number, the number 1
These permissions are the same for files and directories but with slightly different meanings.
The Read Permission – For files with the read permission set, the file can be read in a normal text editor. In the case of a directory or folder, the contents of that folder can be viewed.
Write Permission – Files can be changed or modified when this permission is set. For directories, the contents can be altered in a lot of ways. Examples of alteration include deleting of new files, creating new files, moving files and renaming files.
The Execute Permission – Files with the execute permission set can be executed while directories can be entered using the CD command.
The rationale behind the numbers being three (777 for instance) is that they represent the Owner, Group, and Others.
The first “7” signifies some sort of permission or access for the Owner, the second “7” represents permission or access for the Group and the third “7” represents permission or access for Others.
How To Understand The Numbers (777,775,655 and so on)
We already learned that in the decimal format, the permissions have numbers assigned to them. To get the permission assigned to the classes, we will add the numbers based on the access granted.
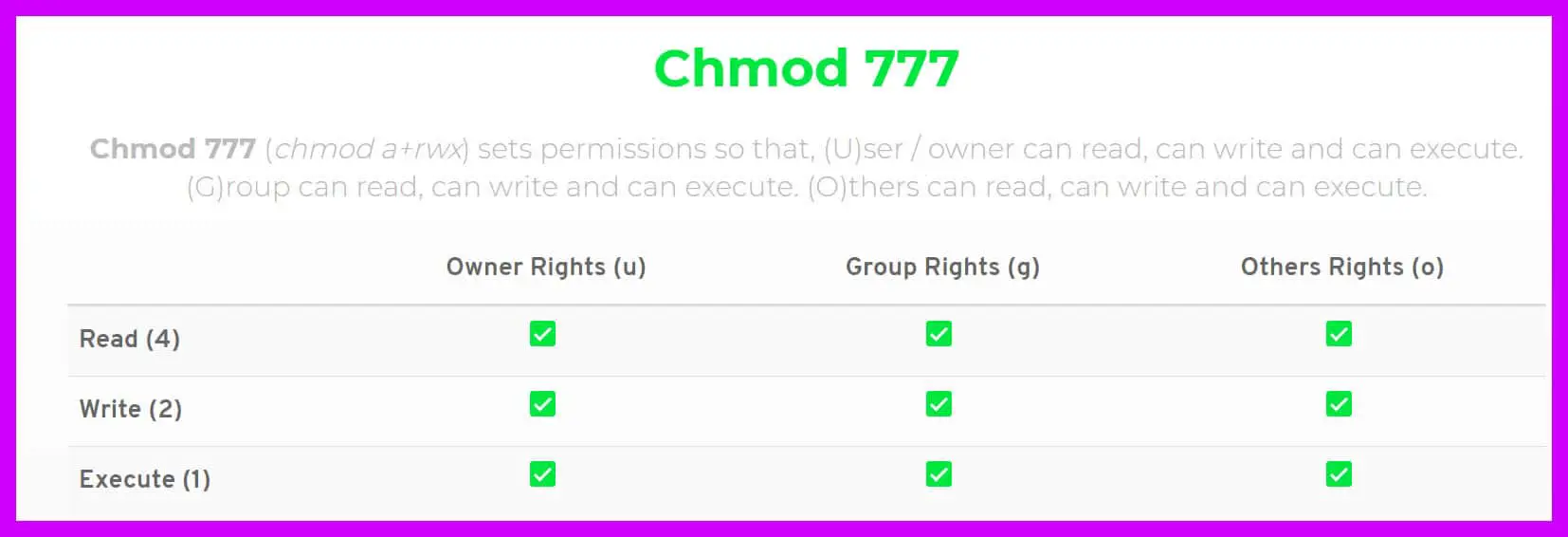
For example, a (4+2+1 with)=7 means Read, Write and Execute functions are available and accessible to one class, if it is 777, it means all classes can read, execute and write. 😎
Here’s a table that explains the different permutations that could occur.
0 – No permission or access
1 – Only “Execute” allowed
2 – Only “Write” allowed
3 – “Write” and “Execute” allowed
4 – “Read” only allowed
5 – “Read” and “Execute” allowed
6 – “Read” and “Write” allowed
7 – All permissions and access are granted
Based on the information above, to set permissions to files and folders, set the number accordingly to the permission that you want them to have.
Some permissions promise easy access to all classes; some restrict all classes while others differentiate between classes. Whichever one we use, it must be determined by the sensitivity of the files or folders we protect.
Still, this concept is not clear. 🤔 No Worries! Watch out for this “Linux File Permissions and Attributes” video to understand this.
Some Permissions Explained 📗
000 – No permission is set. All-access is denied, and no class can read, write or edit
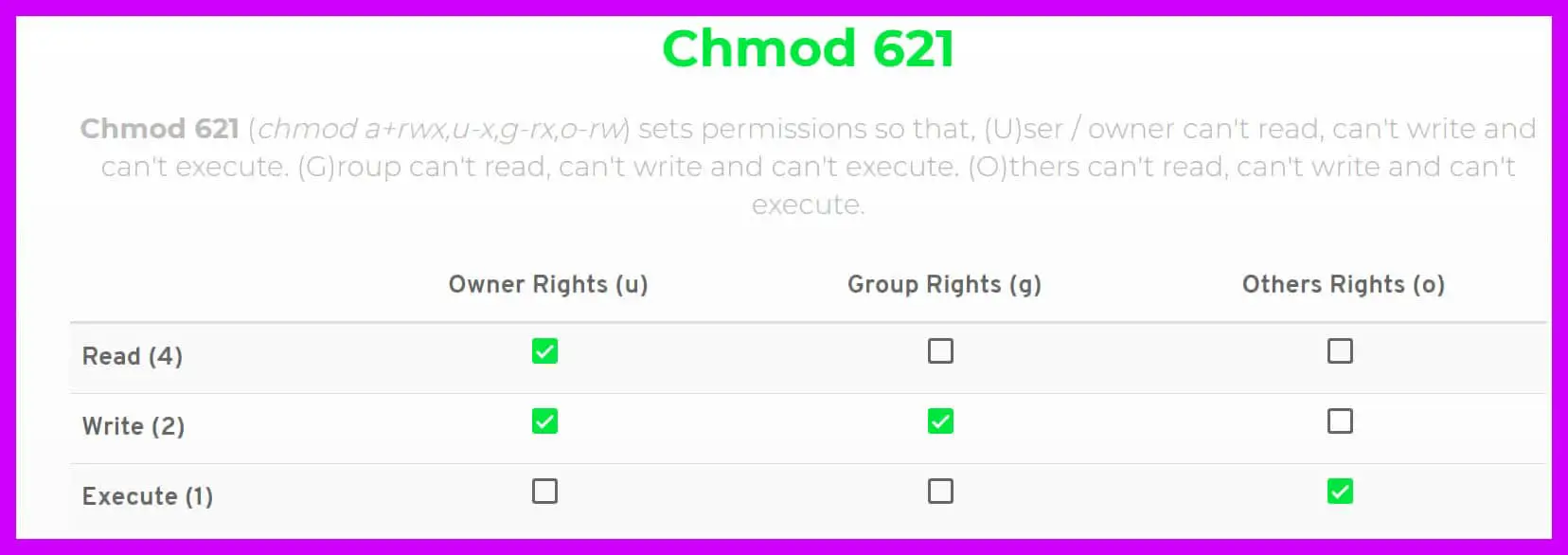
621 – The Owner can read and write, basically he/she can modify the files and folders. Groups can only modify the file but not read. Others can only execute the file.
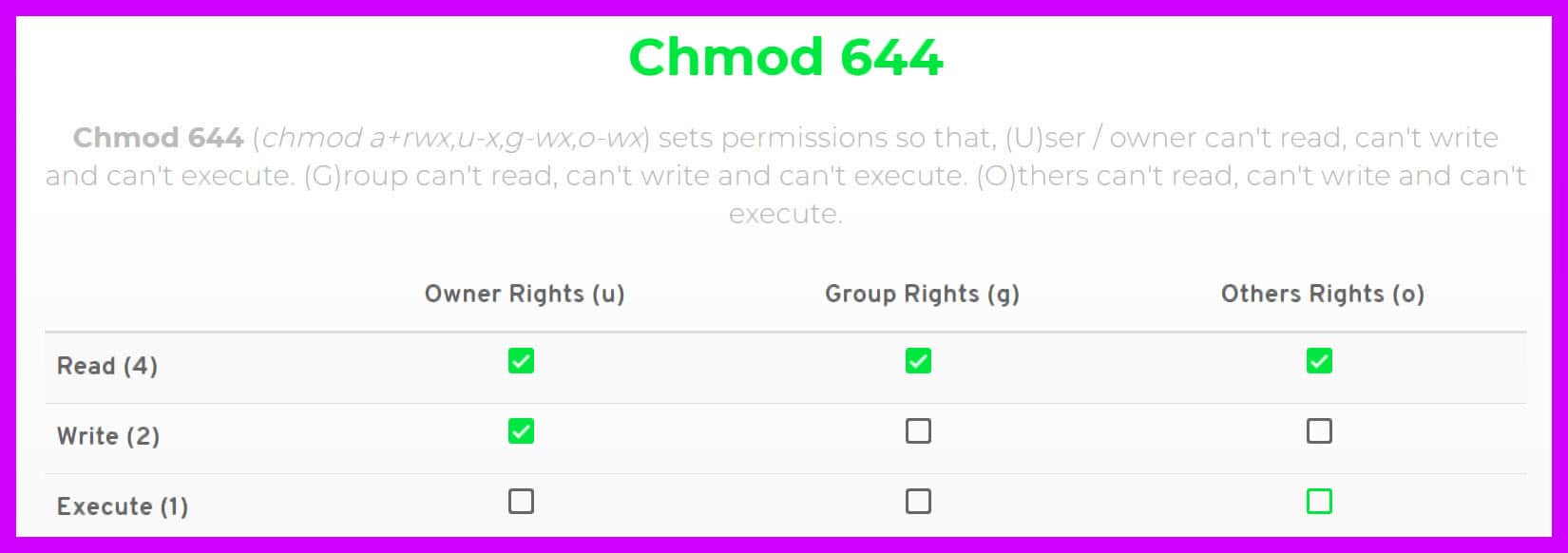
644 – This suggests that the Owner can only read and write, the Group can only read and Others too will be allowed to only read the files or folders.
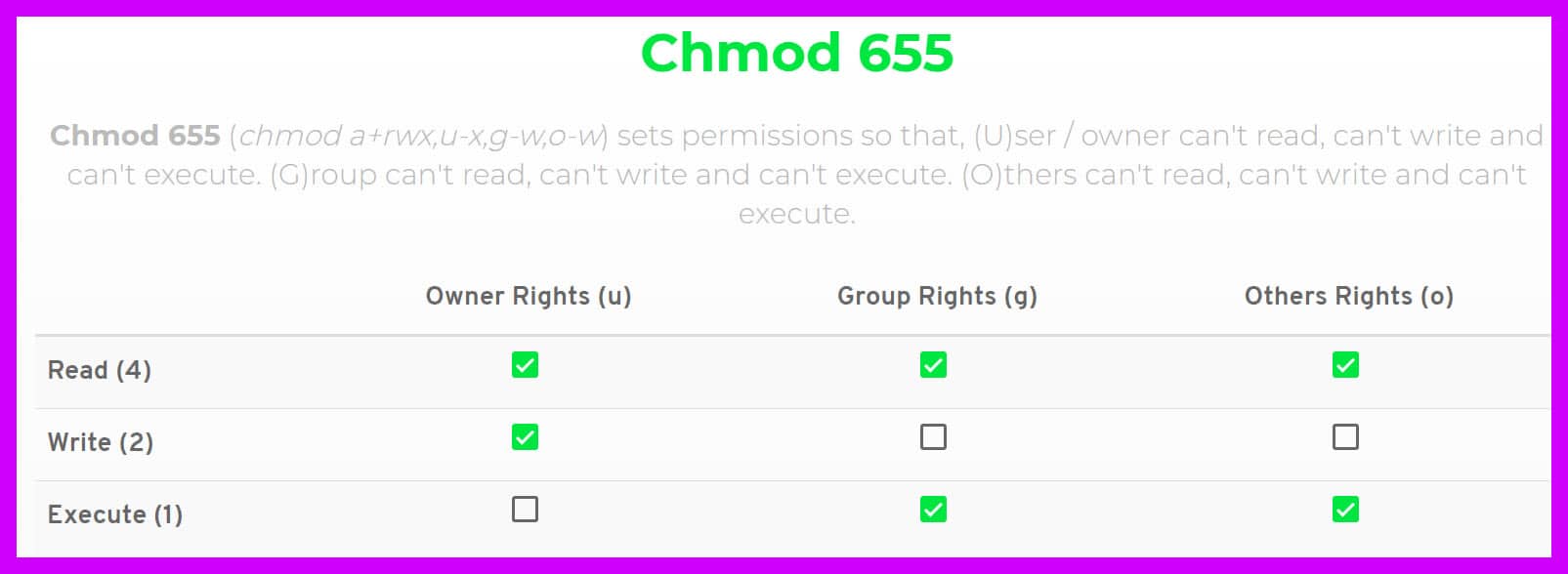
655 – Another type of permission that indicates that the Owner will only be able to read and write, the Group will be able to read and execute and Others will have the same permissions as the Group.
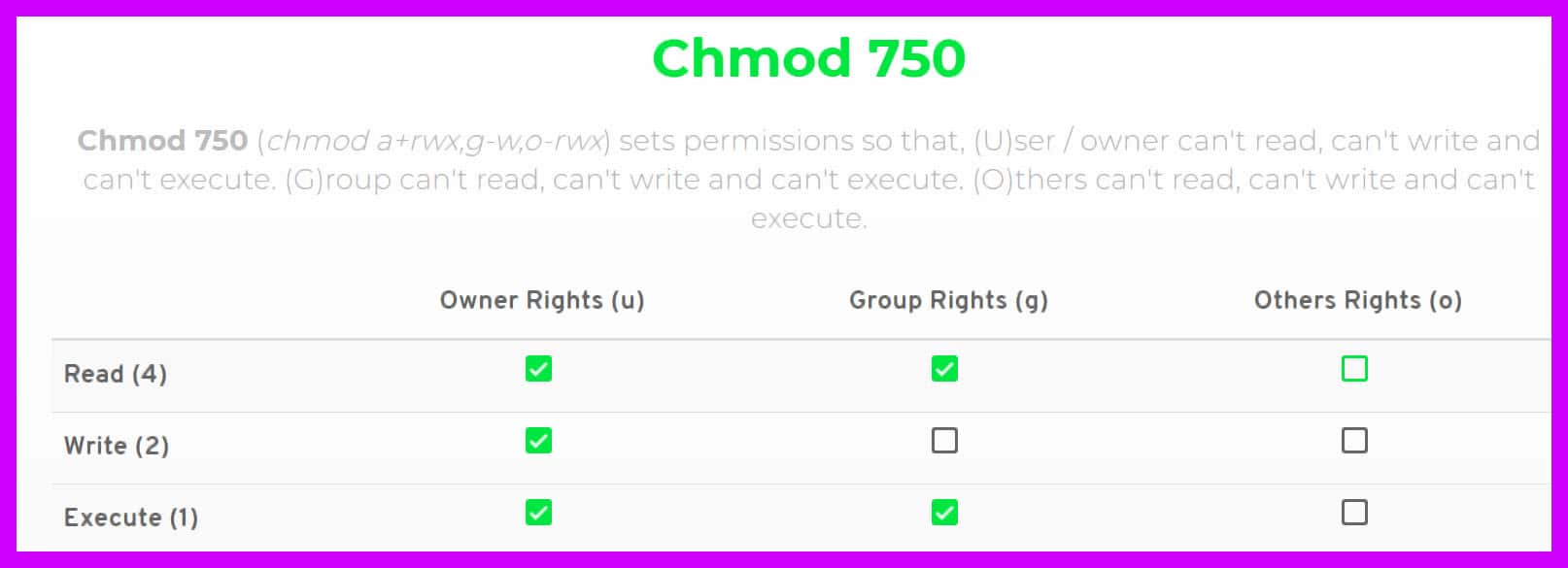
750 – Owners have all permissions set, Groups can read and execute but Others have no permission set so they cannot read, write or execute any file or folder.
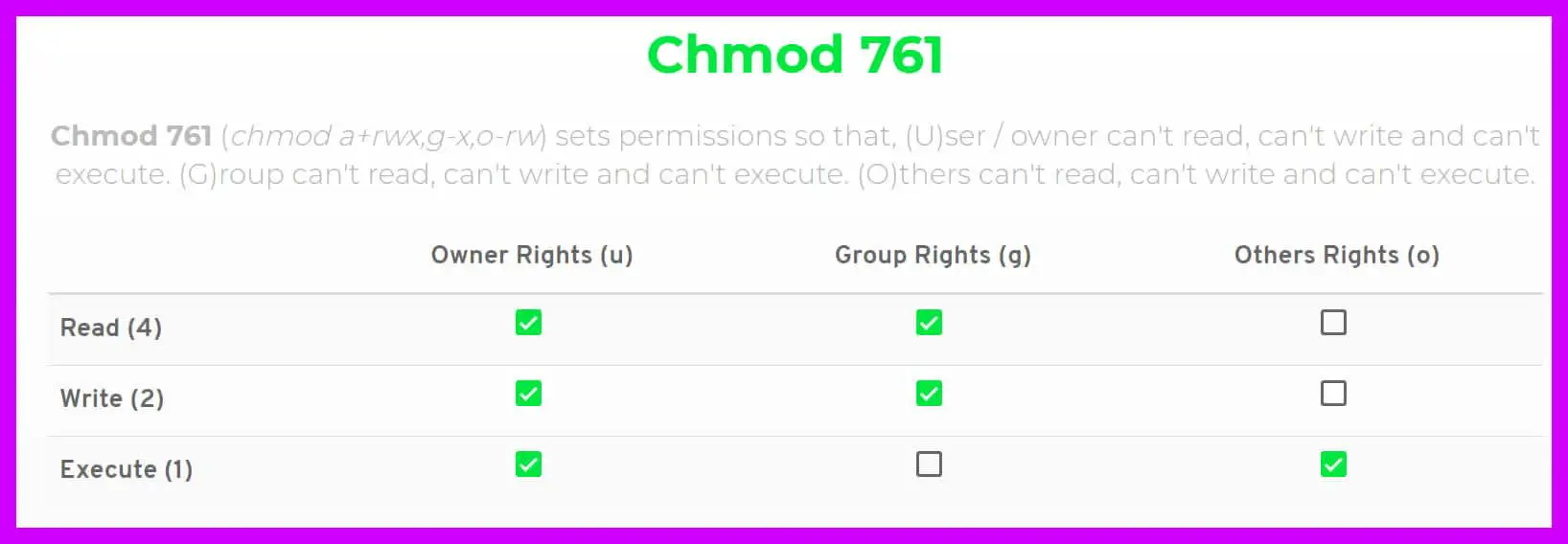
761 – Owners will have access to read, write and execute. Groups will only read and write and Others can only execute.
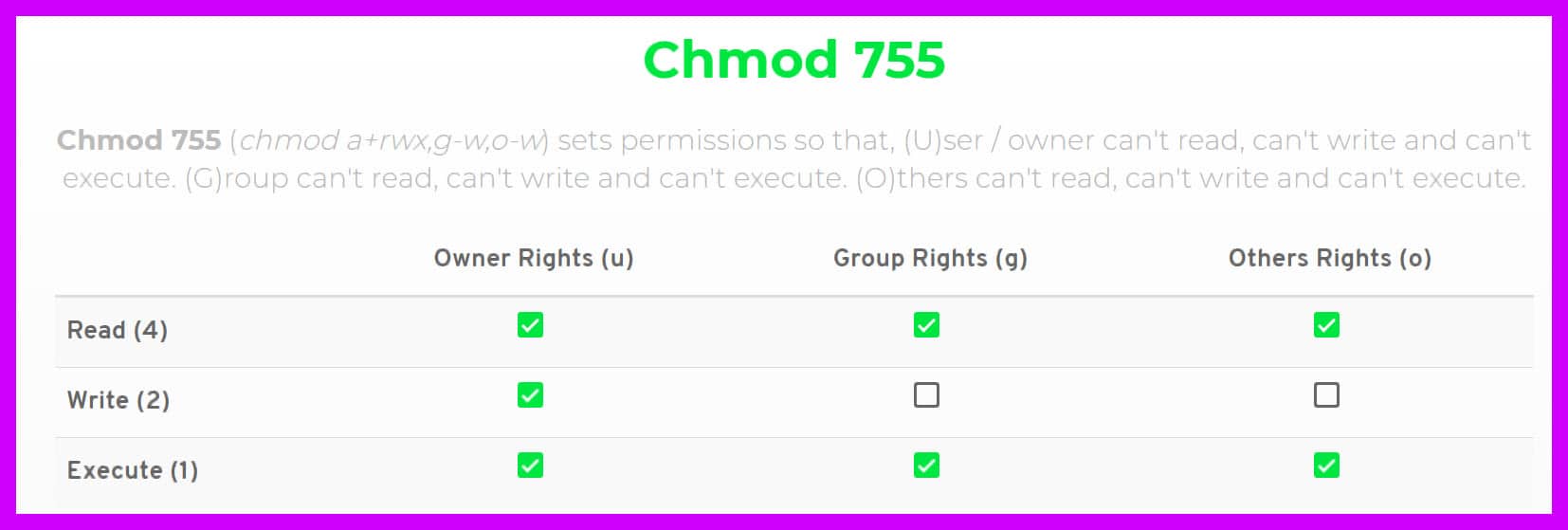
755 – Owner has all permission and access, Groups can only read and execute, Others can only read and execute too.
777 – All classes, Owners – Groups – Others, share the same permission to read, execute and write files or folders.
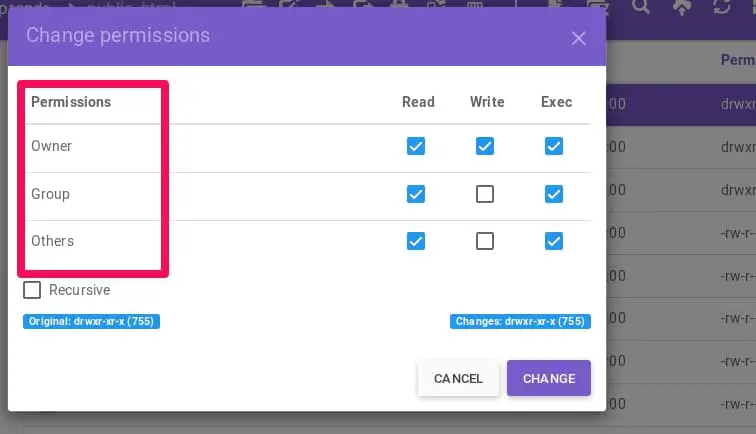
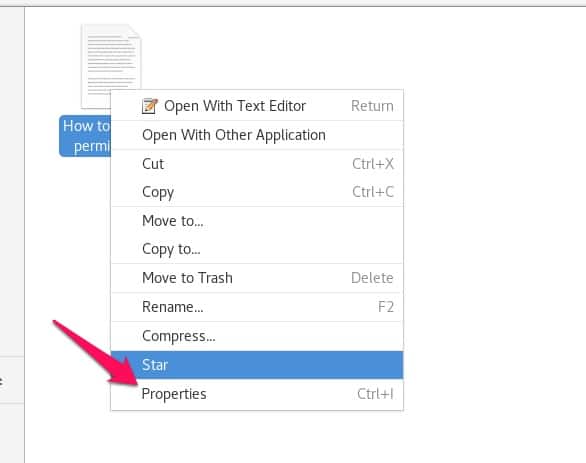
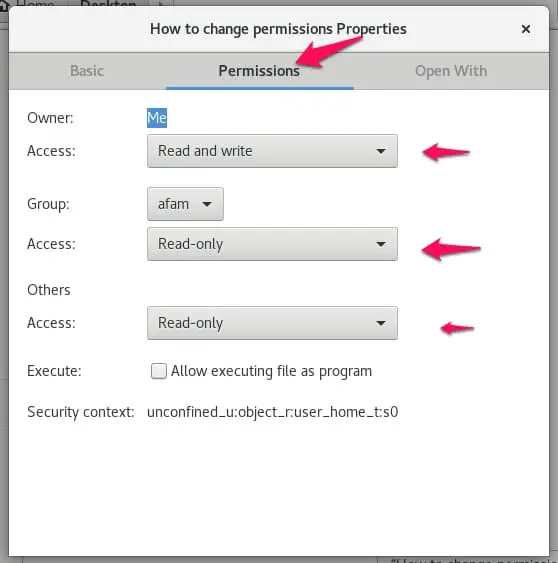
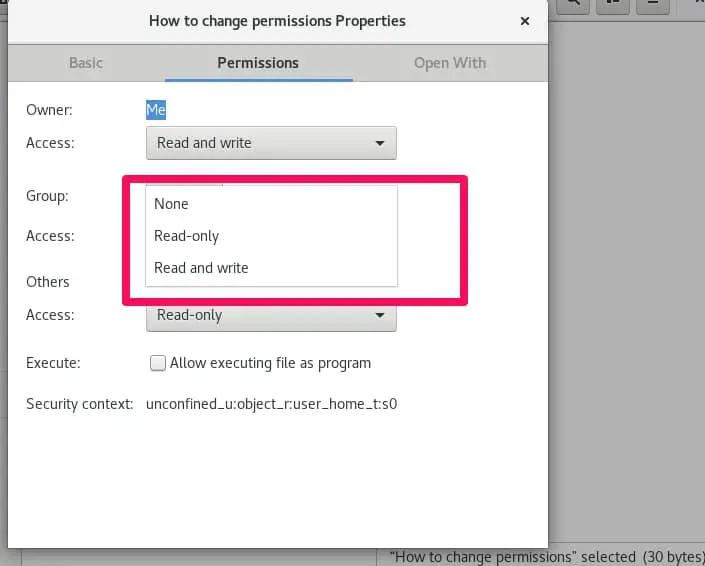
How To Change Permissions Of Files Using GUI
This is a simple process:
First, you have to do is right-click the file or folder and click on “properties”.
By default, you will be on the”basic” tab. Click on the “permissions” tab at the top center, here you will be able to modify permissions for the file.
The owner, group and other categories all have an “access” value. By clicking on the drop-down list, in front of the access value, you can change the permission rights.
If you are a webmaster and looking for detailed information about WordPress file management then mentioned video is for you only.
How to use chmod 777 command in linux
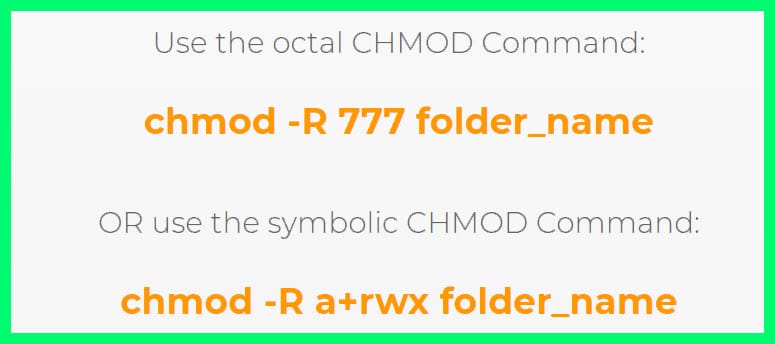
You can modify a file or directory’s permissions in Linux using the chmod command. All users have read, write, and execute access using the 777 permission setting.
Setting permissions to 777 with the chmod command, type
chmod 777 <filename>
You should substitute the file name or directory whose permissions you want to modify for <filename>.
For instance, you would type the following to grant read, write, and execute permissions to everyone for the text file myfile.txt:
chmod 777 myfile.txt
It’s important to remember that the 777 permission setting is quite permissive and might not be appropriate for all files and directories.
Generally, giving a file or directory the fewest permissive permissions possible is good practice.
Use the 644 permission setting rather than 777, for instance, if a file merely needs to be read by other users. This would give the file’s owner read-write access while limiting other users’ access to read-only.
chmod 644 myfile.txt
How do I give 777 permission to a user in Linux?
Use the chmod command with the u+rwx flag, which stands for “user + read, write, execute,” to provide a user 777 permission for a file or directory in Linux.
The chmod command’s syntax is as follows:
chmod u+rwx <filename>
If you want to update the permissions of a file or directory, replace <filename> with its name.
For instance, you would type the following to grant the owner of the text file myfile.txt the ability to read, write, and execute:
chmod u+rwx myfile.txt
You can use the -R flag to do recursive operations, as in the following example, to grant 777 permission to a user for a directory and all of its subdirectories and files:
chmod -R u+rwx <directory>
Replace directory> with the name of the directory, together with any subdirectories and files within it whose permissions you wish to modify.
For instance, you would type the following to grant the owner of the directory mydir, as well as all of its subdirectories and files, read, write, and execute permissions:
chmod -R u+rwx mydir
What the sudo chmod r 777 command will do?
Using the sudo command, you can execute a command as the superuser. A file or directory’s permissions can be changed with the chmod command.
The 777 permission level permits read, write, and execute permissions for all users, while the r flag instructs chmod to act recursively.
You would type the following to use the sudo chmod command to change a file or directory’s permissions, along with all of its subdirectories and files, to 777:
sudo chmod -R 777 <directory>
Replace <directory> with the name of the directory and any subdirectories and files within it whose permissions you wish to modify.
For instance, you would type the following to grant everyone permission to read, write, and execute on the directory mydir and all of its files and subdirectories:
sudo chmod -R 777 mydir
The Danger Of Using Chmod 777 🧨
We know many files and folders are important to our jobs or family. These files and folders should be kept private and set the permission to “777” do not help in keeping the information on the file secret. It ensures that just about anybody can read and modify your file.
Perhaps instead of quickly changing the file permissions when we have issues with our web servers, we might want to consider changing the file ownership status to the user running the application, set files permission to “644” and file directories to “755””.
The command used to change permission as explained above is ” chmod” while that of directories is “chown”. Hopefully, this will solve our issues while maintaining the integrity of our files.
What is the Windows equivalent of chmod 777?
The icacls command in Windows is the chmod 777 command’s equivalent.
You can modify the permissions on a file or directory in Windows using the icacls command. The following command can be used to grant everyone read, write, and execute permissions for a file or directory:
icacls <filename> /grant Everyone:(OI)(CI)(F)
You should substitute the file name or directory whose permissions you want to modify for <filename>.
For instance, to grant everyone permission to view, write, and execute the file C:myfile.txt, you would type:
icacls C:\myfile.txt /grant Everyone:(OI)(CI)(F)
The specified user or group receives the given permissions thanks to the /grant flag. The (OI)(CI)(F) permissions give the ability to read, write, and execute.
The acronyms for the three flags are OI (for “object inherit”), CI (for “container inherit”), and F (for “full control”).
How to change the chmod 777
Using the chmod command on Linux, you would use the following syntax to alter a file or directory’s permissions from 777 to a new setting:
chmod <new-permissions> <filename>
Change the desired permission setting to <new-permissions> and <filename> to the name of the file or directory whose permissions you want to modify.
As an illustration, to alter a file’s permissions from 777 to 644, you might type:
chmod 644 <filename>
Using the -R flag to operate recursively, you can modify a directory’s permissions, as well as those of all its subdirectories and files, from 777 to 755.
chmod -R 755 <directory>
How To Undo chmod 777?
Using the chmod command in Linux with the -R flag to work recursively and the —reference option to modify the target file’s permissions to match the reference file will undo the chmod 777 command and restore the original permissions on the target file or directory.
The following command, for instance, can be used to reverse the chmod 777 command on a file and return its original permissions:
chmod –reference=<original-file> <modified-file>
<original-file> should be changed to the name of the file whose permissions you wish to reference, and <modified-file> should be changed to the name of the file whose permissions you want to restore.
As an illustration, you might type: to restore the original permissions of the file modified.txt based on the permissions of the file original.txt.
chmod –reference=original.txt modified.txt
Using the -R flag to work recursively, you can undo the chmod 777 command on a directory and every one of its subdirectories and files, as in the following example:
chmod -R –reference=<original-directory> <modified-directory>
Change <original-directory> to the name of the directory whose permissions you wish to use as a reference and <modified-directory> to the name of the directory, together with all of its subdirectories and files, whose permissions you want to restore.
For instance, you would type: To restore the original permissions of the directory modified and all of its files and subdirectories depending on the permissions of the directory original.
chmod -R –reference=original modified
📗FAQ
What does chmod 770 do?
The 770 permission level grants the owner of the file read, write, and execute permissions and read and execute permissions for others.
What does chmod 774 do?
The file’s owner is given read, write, and execute access with the 774 permission setting, and others are given read and execute permissions.
What is chmod 775 permission?
The 775 permission setting grants the owner of the file read, write, and execute permissions and read and execute permissions to members of the same group as the owner.
What does 777 permission mean?
The 777 permission setting in Linux grants all users the ability to read, write, and execute.
What is chmod 755?
The 755 permission level in Linux grants read, write, and execute access to the directory or file’s owner and read and execute capabilities to others.
What does chmod 444 do?
All users may have read-only rights under Linux’s 444 permission setting.
What is chmod 666?
The 666 permission setting in Linux grants all users read and write access.
What does chmod 766 mean?
The 766 permission setting in Linux grants read, write, and execute access to the file or directory owner and read and write permissions to others.
What is chmod 744?
The 744 permission level in Linux grants read, write, and execute permissions to the file or directory owner and read-only permissions to everyone else.
What does chmod 760 do?
The 760 permission setting in Linux grants read, write, and execute access to the file or directory’s owner and read and write permissions to users who are part of the same group as the owner.
What is 555 permission in Linux?
The 555 permission level in Linux grants read and execute permissions to each user.
Conclusion
Granting access to all classes (chmod 777) can sometimes be a security hazard. Everybody accessing that file or folder can make changes and modify it according to their will.
You could lose vital information in the least or the wrong person could access sensitive information and modify it.
A sensible option is to consider using the “755” permission. It gives groups and others access to read and execute but the privilege of modifying the file still rests with the owner. Many permissions are available for use. Find the perfect fit by considering how important the file or folder secrecy is.
In using a Linux system, this information is vital. Permissions are very important and the knowledge of how to use them will only enhance user satisfaction.
Changing these permissions are pretty easy so there’s some sort of flexibility when it comes to set permissions for different files and folders which could sometimes be called directories.
Please comment below on your experiences about permissions.