If you’re a digital investigator or a cybersecurity analyst, you probably know Maltego, the popular open-source intelligence (OSINT) tool for mapping relationships and patterns in data.
However, you may also be aware of some limitations or drawbacks of Maltego, such as its steep learning curve, pricing model, or compatibility issues with certain data sources or platforms.
These issues can slow your investigations, limit your capabilities, or even make you depend on a tool that may not always deliver the desired results.
Moreover, as the digital landscape evolves and new challenges emerge, you may need to expand your toolkit and explore alternatives to Maltego that offer better features, flexibility, or cost-effectiveness.
Fortunately, several Maltego alternatives available on the market can help you overcome these challenges and enhance your OSINT workflows.
In this article, we will introduce you to some of the most promising Maltego alternatives, compare their key features and benefits, and provide tips on choosing the best fit for your needs.
Whether you’re a seasoned Maltego user looking to explore new options or a newcomer to the OSINT field, this article will help you discover the power of the alternatives to Maltego and take your investigations to the next level.
Let’s get started!
What is Maltego?🔭
Maltego, a powerful digital investigation tool, is designed to uncover crucial intelligence and establish connections within complex datasets.
Leveraging its advanced data mining and visualization capabilities, Maltego allows investigators to extract meaningful insights from diverse sources.
With a unique graph-based approach, it visualizes relationships and patterns between entities, enhancing understanding.
Through its extensive library of modular algorithms, known as transforms, Maltego enables data aggregation, correlation, and analysis across multiple domains.
With seamless access to social media platforms, public databases, and online infrastructure, Maltego empowers investigators with a user-friendly interface and collaborative features.
Its exceptional capabilities make Maltego an indispensable asset for law enforcement, cybersecurity, intelligence, and fraud detection professionals.
Criteria for Evaluating Maltego Alternatives
When considering Maltego alternatives for your digital investigation needs, it is crucial to evaluate various criteria to ensure you choose the right tool.
Here are some key factors to consider:-
Features and Functionality:- Assess the alternative’s capabilities, such as data visualization, entity correlation, and data mining. Look for features that align with your investigative requirements.
Scalability and Customization:- Determine if the alternative can handle large datasets and adapt to your specific investigative workflows. Flexibility and scalability are vital for efficient investigations.
Data Sources and Integrations:- Investigate the alternative’s access to diverse data sources, including social media, public records, and specialized databases. Consider integration capabilities with external tools and APIs.
User Interface and Ease of Use:- Evaluate the alternative’s interface intuitiveness and ease of navigation. A user-friendly tool with well-designed controls and customizable layouts can enhance productivity.
Pricing Models and Licensing:- Consider the alternative’s pricing structure, including subscription plans, licensing options, and additional costs for accessing premium features or data sources.
By carefully analyzing these criteria, you can make an informed decision when selecting a suitable Maltego alternative.
It is essential to choose a tool that meets your specific investigative requirements and provides a seamless user experience, scalability, and integration capabilities.
Remember that each alternative may offer unique strengths and weaknesses, so prioritize the criteria that align with your investigation objectives and workflow preferences.
Here, we have prepared a list of some of the best ones –
Best Maltego Alternatives For Improved Data Analysis👌
1. Gephi
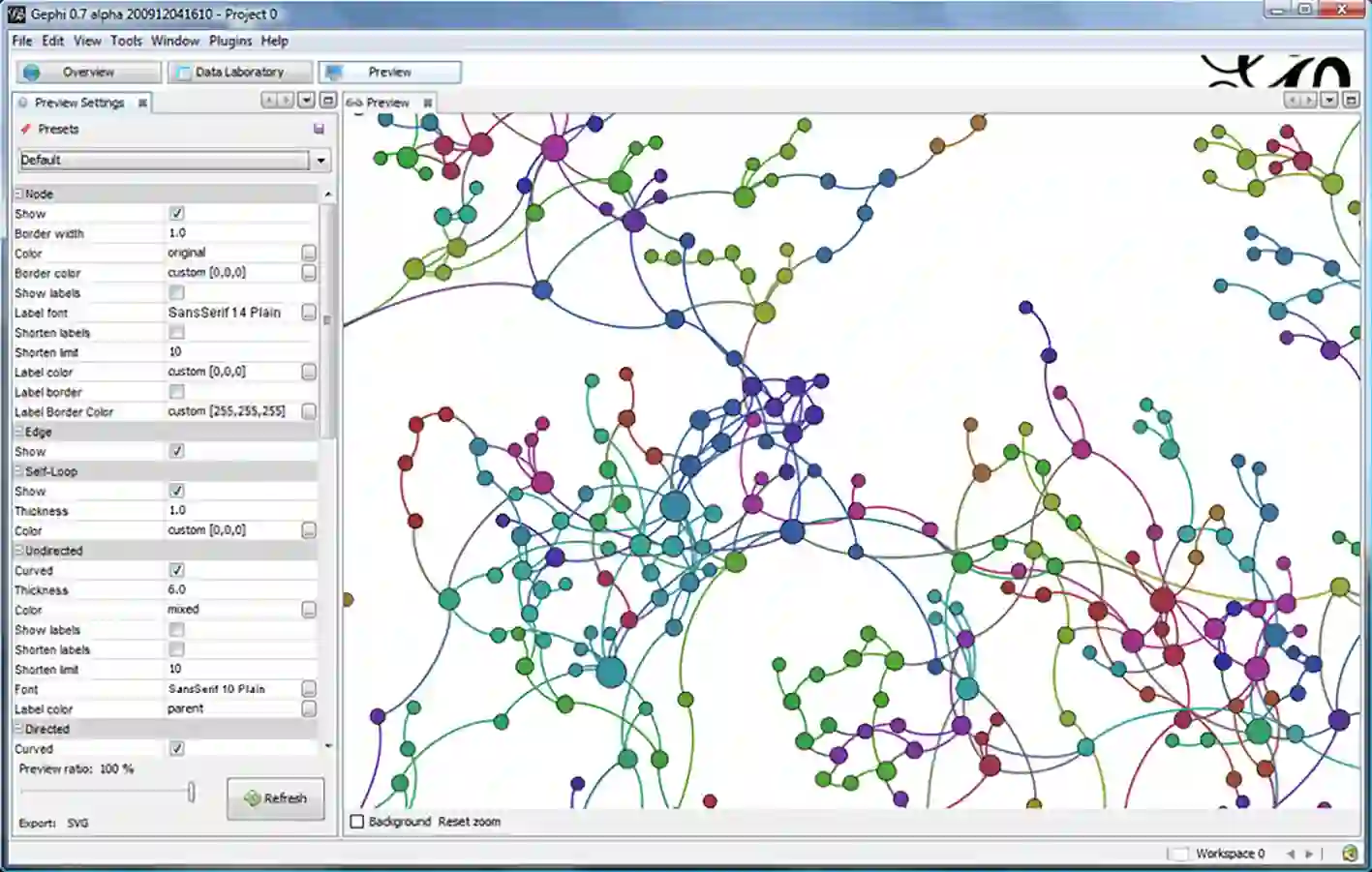
Gephi is one of the most incredible and unique Maltego alternatives that offer the fastest data gathering and analyzing services.
Gephi is the latest and the most advanced open-source platform to visualize and analyze information graphically.
With Gephi, one can quickly explore information with a simultaneous graphic display.
Gephi offers information from trusted sources, making it more reliable for users. The platform also provides active sound insulation, which most software fails to provide.
The built-in 3D graphic engine feature of Gephi allows you to visualize the real-time graphical representation of the data. The platform even offers supported file formats coupled with dynamic information filtering.
The application supports all the advanced features, including statistical representation of data, exporting and importing information, and algorithm layout, making it the most recommended software for data interpretation.
To know more about Gephi, visit the official website without any delay.
Maltego vs Gephi:-
Maltego is an advanced tool for data analysis and visualization, whereas Gephi is a general-purpose tool for graph analysis and visualization.
While Gephi is more suited to researchers and analysts who wish to examine and visualize large-scale networks and graphs, Maltego is more appropriate for investigators and analysts who must collect and visualize data from diverse sources.
Here is a detailed table comparing Maltego and Gephi:-
| Criteria | Maltego | Gephi |
|---|---|---|
| Type of Tool | OSINT and data visualization tool | Graph visualization and analysis tool |
| Purpose | Investigate and visualize data relationships in various data sources | Analyze and visualize large-scale networks and graphs |
| User Interface | User-friendly GUI with drag-and-drop interface and customizable workspaces | Simple GUI with basic functionalities |
| Data Sources | Can connect to various data sources such as public records, social media, and dark web | Import data from various file formats such as GEXF, GraphML, CSV, and Excel |
| Data Visualization | Offers a range of visualization options including entity lists, graphs, charts, and maps | Provides various layout algorithms, filtering options, and visualization styles for graphs |
| Analysis Capabilities | Offers a range of analysis capabilities including entity correlation, social network analysis, and geospatial analysis | Provides basic analysis capabilities such as centrality measures, clustering algorithms, and community detection |
| Collaboration | Offers real-time collaboration for multiple users | Does not offer collaborative features |
| Cost | Subscription-based pricing model with a free trial version and different tiers for personal and commercial use | Open-source software available for free |
| Learning Curve | Requires some level of technical expertise and experience to use effectively | Easy to use, with no prior experience required |
2. SpiderFoot
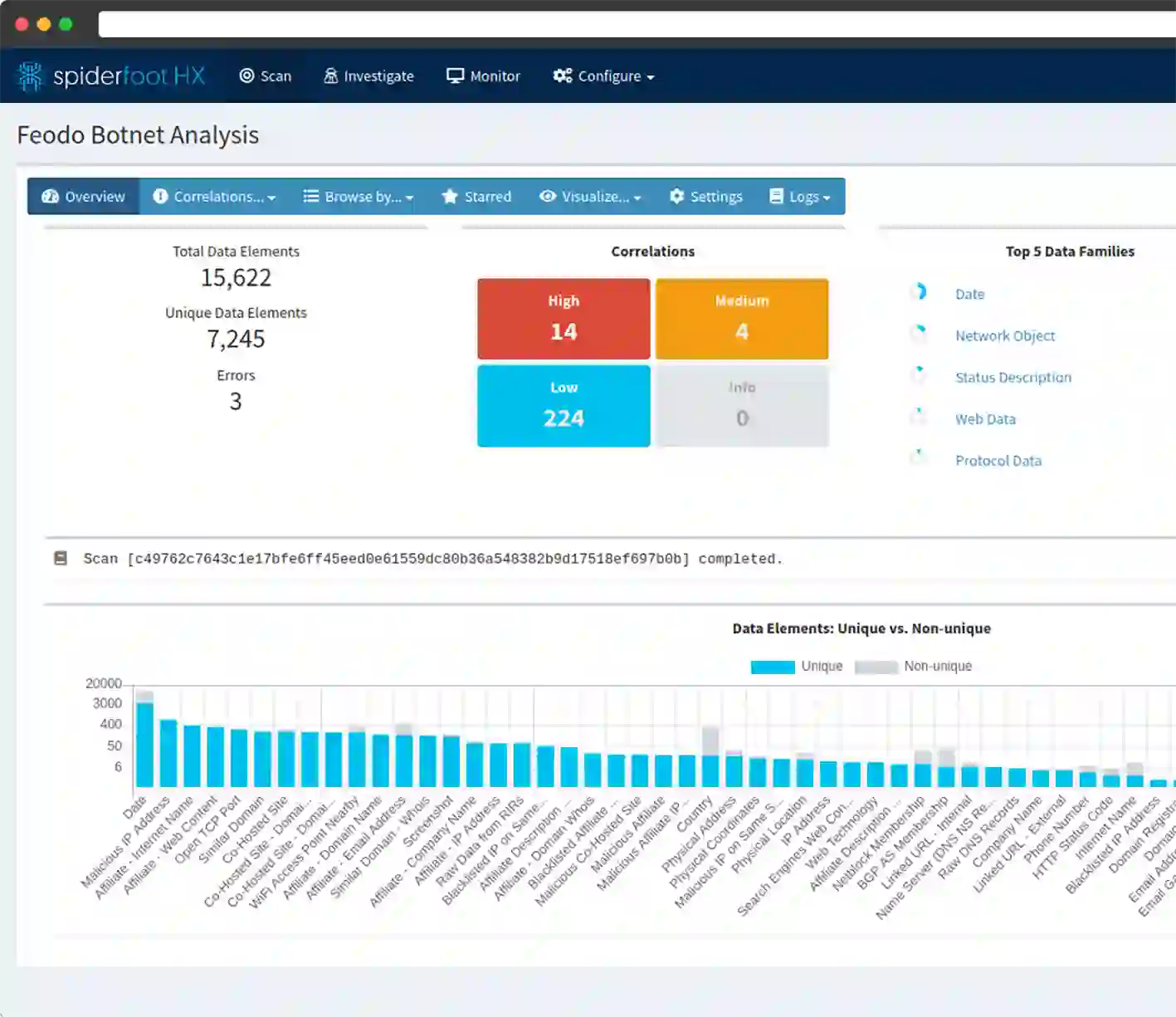
Do you want software that automatically analyzes the data and serves you the report? Here is the best you can opt for – The SpiderFoot.
SpiderFoot is technically advanced software built to automate the open-source intelligence program.
The platform offers a wide range of features that automatically analyzes and represents the data best.
The software is the best platform for gathering information from different sources, including IP addresses, social media websites, domains, and other sources.
The platform establishes or identifies the relationship between the information and the target to be investigated.
Features of SpiderFoot:-
- The software scans data accurately and quickly, thereby saving an adequate amount of time.
- Once the software scans the complete data, it sends an e-mail notification to inform you that the scanning is completed.
- It easily integrates with various sources to gather information and even helps import scanned targets.
- The application is best known for its timeous investigation, which is impressive.
Some specific uses for SpiderFoot include:-
Gathering intelligence about a person or organization:- SpiderFoot is a tool that may be used to gather data about a person or business from various places, including social media profiles, domain registrations, and blacklists.
Identifying potential security risks:- SpiderFoot is a tool that may gather data about a target’s internet activity and spot potential security hazards like exposed passwords or weak systems.
Tracking down suspects:- A suspect’s online presence, relationships, and other information can be discovered using SpiderFoot to learn more about them.
Gathering evidence:– Information can be gathered via SpiderFoot and utilized as proof in an investigation.
Spiderfoot vs Maltego:-
SpiderFoot is an open-source tool that can work on both Windows & Linux. The tool was designed using Python language. It has a top-notch configuration and can operate on any platform you want.
The tool can integrate with an easy and interactive GUI. Besides, the tool provides you with a powerful command-line interface. You can automatically use it on more than 100+ OSINT sources.
This feature helps you understand the intelligence of names, emails, domain names, IP addresses, etc. You are provided with a piece of extensive information about e-mails, web servers, and netblocks.
Using the tool, you can target according to your requirement. Maltego is another exciting tool that Paterva designed.
It is an inbuilt tool of Kali Linux. This is also an open-source intelligence tool that can work using in-built transforms.
As it is an open-source tool, you can write customized code. The programming language you write in Java can be displayed as a built-in language for Kali Linux.
Unlike Spiderfoot, you must register on Maltego, which is free to use on the Paterva website. After registration, you can use the tool to design effective digital footprints for your target on the internet.
They both are equally effective, and we can highly recommend them both. However, Maltego has a slight edge over Spiderfoot regarding efficiency and customer support. We found that Spiderfoot was lagging in these areas.
Here’s a table comparing SpiderFoot and Maltego:-
| Feature | SpiderFoot | Maltego |
|---|---|---|
| Purpose | Open-source intelligence-gathering tool | Proprietary intelligence gathering tool |
| License | GPL v2 | Proprietary, with free and paid versions available |
| User Interface | Command-line interface and web-based dashboard | Graphical user interface |
| OS Compatibility | Windows, Linux, and macOS | Windows, Linux, and macOS |
| Data Sources | Over 200 modules for data collection and analysis | Over 100 data connectors and transforms |
| Integration with OSINT | Integration with various OSINT tools like Shodan, Censys, and WHOIS | Integration with various OSINT tools like VirusTotal, HaveIBeenPwned, and Google Maps |
| Link Analysis Features | Basic link analysis and graphing capabilities | Advanced link analysis and graphing capabilities |
| Collaboration Features | None | Collaboration with other users through a shared server |
| Price | Free and open-source | Free and paid versions are available |
3. Linkurious
Are you searching for the best data security and forensics software? Here is the best you can choose – The Linkurious.
Linkurious is another great forensics and open-source data application that helps you with an on-spot graphical representation of information, which is very helpful. The platform is best recommended for fraud and threat recognition and detection.
If you are investigating threat and fraud cases, then Linkurious is a great application you can use. The Linkurious software has built-in alarming systems that help you detect all possible frauds in the data source.
The platform even establishes real-time relations between the information and the subject, making it easier to analyze and reach a conclusion.
All you need for the application to work is to identify the detection rules and add them to the commands.
Once you have entered the rules, the app identifies all the suspicious activities of the target, which is a fantastic feature.
With all the advanced and unique fraud detection and data interpretation features, Linkurious can be regarded as one of the excellent Maltego alternatives.
Primary features associated with Linkurious:-
- Linkurious is one of the best platforms to analyze and visualize information in a structured manner.
- The platform has impressive built-in features that help you with fraud detection and money laundering cases.
- The software integrates with different platforms, making it easier to implement on the target.
- The software is highly flexible in its operations and functionalities.
Maltego vs Linkurious:-
Maltego is a robust data mining and analysis program that can gather data from many sources, evaluate it, and do link analysis. In contrast, Linkurious is a graph visualization tool that focuses on displaying intricate and sizable graphs.
While Linkurious offers a user-friendly interface and doesn’t need any technical knowledge, Maltego needs some technical knowledge to utilize.
Maltego does well with small to medium-sized data sets but can be slow with bigger data sets, whereas Linkurious does well with huge data sets and can handle real-time graph data.
Both tools have unique pricing structures and provide security features and connectors with various third-party tools.
Here’s a detailed table comparing Maltego and Linkurious:-
| Criteria | Maltego | Linkurious |
|---|---|---|
| Type | Data mining and analysis tool | Graph visualization tool |
| Main features | Collects and analyzes data from various sources, performs link analysis and data visualization | Visualizes complex and large-scale graphs, performs interactive graph exploration, allows graph query and filtering |
| Data sources | Supports various data sources including social media, online databases, and APIs | Supports various data sources including graph databases, SQL databases, and APIs |
| Ease of use | It requires some technical expertise to use, but has an intuitive interface and extensive documentation. | It has a user-friendly interface, requires no technical expertise, and has limited documentation |
| Performance | Performs well with small to medium-sized data sets but can be slow with larger data sets | Performs well with large-scale data sets and can handle real-time graph data |
| Integrations | Integrates with various third-party tools such as Shodan and VirusTotal | Integrates with various third-party tools such as Neo4j and ElasticSearch |
| Security | It has security features such as access control, encryption, and data masking. | It has security features such as role-based access control and data encryption. |
| Pricing | Offers a free community edition and paid professional and enterprise editions with varying features | Offers a free trial and paid professional and enterprise editions with varying features |
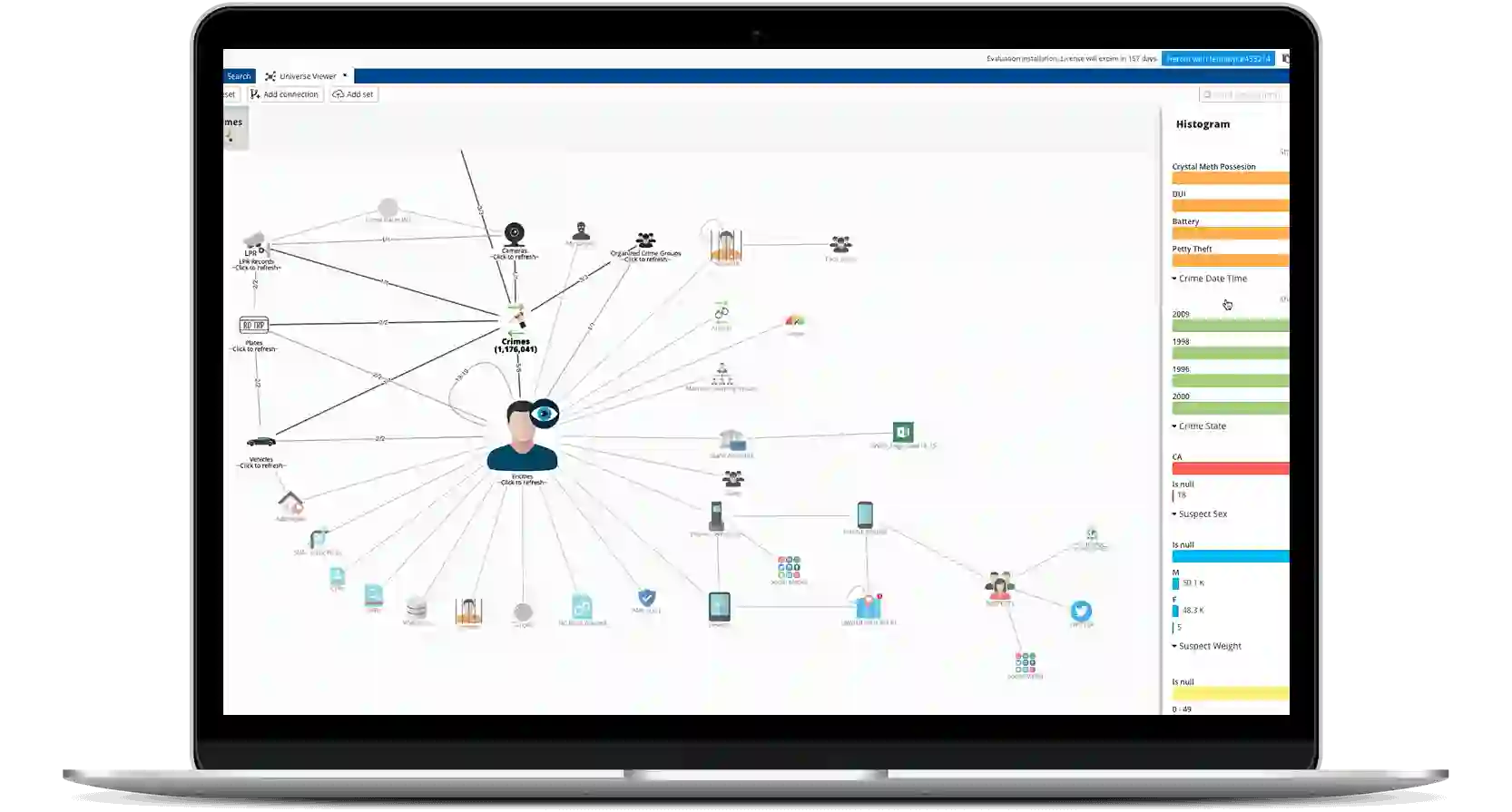
4. DataWalk
DataWalk is considered one of the most well-known Maltego alternatives; It is the latest and most advanced platform for analyzing information and recognizing the link between them.
The software is built to identify data patterns and their relations easily. It even helps identify all possible irregularities caused by extensive source intelligence investigations.
The application displays the result in a structured and single data sheet with the help of various charts, including histograms, link charts, and maps.
The software even establishes a strong bond between external and internal information sources.
Features Associated with DataWalk:-
- The platform is designed to help accelerate the investigation process and reach a conclusion quickly.
- It helps identify suspicious and false claims, making correct assumptions about the statements and information.
- The platform even calculates and delivers risk scores to help identify the risks associated with data scanning.
Maltego vs DataWalk:-
Both programs are capable of link analysis and can combine different data sources; however, DataWalk incorporates machine learning and has extensive search capabilities, whereas Maltego does not.
Finally, DataWalk offers a wide range of customization choices, while Maltego offers fewer.
Overall, Maltego and DataWalk are strong data and link analysis tools. Still, their differences in pricing, user interfaces, and feature sets make them more appropriate for certain use cases and user preferences.
Here’s a detailed comparison table between Maltego and DataWalk:-
| Feature | Maltego | DataWalk |
|---|---|---|
| Price | Freemium, Pro and Enterprise versions available | Contact for pricing |
| User Interface | User-friendly with drag-and-drop functionality | User-friendly with customizable dashboards and workflows |
| Data Sources | Various open-source and commercial sources | Multiple internal and external sources |
| Data Visualization | Graph-based visualizations | Graph-based visualizations, tables, and charts |
| Link Analysis | Yes | Yes |
| Data Mapping | Yes | Yes |
| Data Integration | Yes | Yes |
| Collaboration | Yes | Yes |
| Advanced Search | Limited | Advanced search capabilities |
| API Integration | Yes | Yes |
| Machine Learning | No | Yes |
| Customization | Limited | Highly customizable |
5. Visallo
If you are an intelligence investigator looking for software to assist you in information analysis and interpretation, then Visallo is the best option.
Visallo is an intelligence data assistance software built to detect fraudulent organizational activities.
Law enforcement officers and individual detectives prefer the Visallo software to identify anomalies in data analysis.
The platform analyzes tons of data within minutes and helps investigators identify the critical and hidden relationship between the information and the target, which is an excellent feature.
You can achieve high accuracy and efficiency with the help of Visallo; Hence, Visallo can be considered one of the finest Maltego alternatives.
Features of Visallo:-
- The software makes accessing various tools and permissions required during the investigation easier.
- The platform offers a customizable workspace coupled with data duplication and transfer.
- The platform can interpret a lot of data within seconds and assist the investigator in situation management and mapping.
6. Poortego
Do you want a secure platform to link and store matters related to OSINT? Here is an excellent software that can help you – The Poortego.
Poortego is an Open-source investigating software that helps manage information in an OSINT investigation.
The software offers the best and most secure environment to manage and store information, which is pretty unique.
Poortego has fixed all the bugs and glitches in its latest updates to provide a more secure ecosystem to store information.
The software is supported on multiple platforms, including Windows, BSD, Linux, etc. The software helps gather and review user data from various sources, which is very beneficial.
The software is user-friendly and requires basic technical knowledge to operate, making it popular among users. Hence, Poortego can be regarded as one of the superb Maltego alternatives with all the outstanding features.
7. IBM i2 Analyst’s NoteBook
As a software developer, IBM does not need any introduction; it is well known for its marvelously designed security software.
The i2 Notebook from IBM is a popular data analysis software built solely to interpret, analyze, and visualize data.
The software can transform and compile the information into intelligence reports, which is impressive.
The software provides a state-of-the-art user interface coupled with innovative features. The software even helps you analyze social media accounts related to the targets.
The app offers superb data views, including geospatial and temporal view options.
To sum it up, the application is a well-designed and organized platform to analyze and summarize intelligence information. So, it can be regarded as one of the excellent Maltego alternatives.
Maltego vs i2:-
Maltego is a popular cyber intelligence and forensics tool that is easy to use and suited for novices. It connects with other applications to automate workflows and is accessible in an open-source form.
On the other hand, IBM i2 is a more sophisticated tool that needs considerable training to master its sophisticated capabilities. It connects with other IBM technologies and third-party apps and has more sophisticated data analysis capabilities.
Both programs can execute various data analysis activities and visualize data, but IBM i2 is better suited for enterprise-level investigations and intelligence analysis.
Here is a detailed table comparing Maltego and IBM i2:-
| Feature | Maltego | IBM i2 |
|---|---|---|
| Purpose | Cyber Intelligence and Forensics tool | Investigative Analysis and Intelligence tool |
| Developer | Paterva | IBM |
| Type of tool | Graphical User Interface (GUI) based tool | Graphical User Interface (GUI) based tool |
| Platform | Windows, Linux and Mac | Windows and Web |
| Licensing | Commercial and Open-Source versions available | Commercial only |
| Data sources | Large number of data sources such as social media, WHOIS, and other open-source databases | Similar data sources as Maltego, but also integrates with internal enterprise databases |
| Entities and Relations | Entities and relationships are represented using nodes and edges respectively | Entities and relationships are represented using nodes and links respectively |
| Ease of Use | Easy to use with a user-friendly interface and drag-and-drop functionality | Requires some training to master its advanced features |
| Data visualization | Offers clear visualizations of connections and data relationships | Offers more advanced visualizations of data relationships and patterns |
| Data analysis | Can perform a wide range of data analysis tasks such as link analysis, data mining, and social network analysis | Offers more advanced data analysis capabilities, including predictive analytics and threat modeling |
| Integration | Integrates with other cyber tools to automate workflows | Integrates with other IBM tools and third-party applications |
| Community Support | Has a large and active user community with plenty of online tutorials and documentation | Has a smaller but active user community with official training and support |
8. Siren.io
Siren.io is one of the best and most well-known Maltego alternatives that can analyze a massive amount of information in one go.
The platform offers massive data searches, understandable graphical representation, and a quick connection between the data and the suspect.
The software is packed with advanced alarming and monitoring systems that help detect threats and fraudulent activities, which is impressive.
The software is built exceptionally with fantastic features to tackle all the investigation problems.
9. Sentinel Visualizer
Adding to the list is another fantastic Maltego alternatives – Sentinel Visualizer; it is the best data analysis assistant that you can opt for.
The software is built to assist data analysts in identifying irregularities in data trends.
The software provides the latest visual and analysis aids to the analysts to detect threats and fraudulent activities.
The software is packed with the latest features and provides a detailed overview of data trends, which is superb. The database visualization feature helps with quick and multi-dimensional viewing of data.
The software is best suited for establishing relationship types; it even highlights data trends, making it easier for you to analyze the data.
10. Social Links
Social Links is a software company that develops automated, AI-driven search methods for extracting and assembling huge volumes of open data.
Their flagship product SL Professional empowers investigators and data security professionals to reach their work objectives quicker and more effectively.
SL Professional offers an immense suite of custom-designed search methods spanning more than 500 open sources.
The product’s advanced search queries, which rely on machine learning, allow users to filter the data as it is being gathered in various sophisticated ways.
However, Social Links OSINT solutions do more than gather information; they also offer advanced analysis tools for refining data as you progress through investigations and penetration tests, returning accurate results for an ever more understandable picture of the data.
Product Features:-
1. A professional bundle of 1000+ original search methods for over 500 open data sources, including all major platforms across social media, messengers, blockchains and the Dark Web
2. Advanced automation features which leverage machine learning to deliver an expansive range for information retrieval, delivering accurate results at remarkable speeds
3. Bespoke analysis tools enable data to be significantly enriched and molded to the user’s particular purposes
4. Seamless integration within any IT infrastructure
5. Social Links offer training and support as part of their product packages
For organizations who need the ultimate OSINT solution, Social Links also have an enterprise-grade platform SL BOX – an on-premise solution offering their widest range of search methods, full customization according to the users’ needs, and total data privacy and security.
Spiderfoot alternatives:-
An open-source intelligence-collecting application called SpiderFoot enables users to gather data about a target from various sources, including social media, domain registrars, and blacklists.
A few SpiderFoot substitutes are listed below:-
Maltego:- Users of this program can collect and analyze data from various sources. It is intended for data mining and open-source intelligence collection.
The Harvester:- With the help of this program, you may collect email addresses, names, and subdomains from various places, including search engines, PGP keyservers, and the Shodan search engine.
Recon-ng:- This tool is intended to automate the recon process and obtain open-source intelligence. It has several modules for acquiring information from numerous sources, including social media, domain registrars, and blacklists.
Shodan:- Users of this search engine can look for and examine comprehensive information on online servers and devices. It can be used to assess vulnerabilities and obtain open-source intelligence.
Here’s a table comparing some popular alternatives to Spiderfoot:-
| Tool Name | Type | License | Language | Features |
|---|---|---|---|---|
| Maltego | OSINT | Commercial | Java | Link analysis, data visualization, entity extraction, social network analysis, email address verification |
| Recon-ng | OSINT | Open-source | Python | Reconnaissance, data collection, API integration, report generation, multi-threading |
| theHarvester | OSINT | Open-source | Python | Email harvesting, subdomain discovery, virtual host discovery, document disclosure, IP reconnaissance |
| Shodan | IoT/OSINT | Commercial | Python | Search engine for internet-connected devices, vulnerability and exploit scanning, network mapping, data visualization |
| Foca | OSINT | Commercial | .NET | Metadata extraction from documents, email harvesting, geolocation, link analysis, reporting |
| Datasploit | OSINT | Open-source | Python | Automated data collection, OSINT reconnaissance, social engineering, domain reconnaissance, data enrichment |
Maltego vs shodan:-
The goals and strengths of Maltego and Shodan are distinct. For open-source intelligence gathering, law enforcement, security experts, and researchers typically employ the link analysis program Maltego.
Conversely, researchers, hobbyists, and cybersecurity experts utilize Shodan, a search engine for internet-connected devices and systems, to identify vulnerabilities and examine networks.
Even though both programs have subscription-based price structures, Maltego is more expensive and offers a user-friendly, visually-based interface with graph-based visualizations.
On the other side, Shodan uses a search-based interface and offers sophisticated search filters for location, device type, and vulnerability.
Both solutions include integrations with many data sources and third-party applications but differ in their restrictions on data sources and access to particular hardware and software.
Here is a detailed table comparing Maltego and Shodan:-
| Feature | Maltego | Shodan |
|---|---|---|
| Purpose | OSINT and Link Analysis Tool | Search Engine for Internet Devices |
| Pricing | Subscription-based, starts at $1,200/year | Subscription-based, starts at $49/month |
| Data Sources | Open-source intelligence, social media, and public records | Internet-connected devices and systems |
| User Interface | User-friendly, visual-based interface | Search-based interface |
| Search Filters | Basic filters for domain, IP address, and entity types | Advanced filters for device types, location, and vulnerabilities |
| Data Visualization | Interactive graph-based visualizations | Maps, charts, and tables |
| Collaboration Features | Team collaboration features, integrations with other tools | Collaboration through API access and integrations |
| Target Audience | Law enforcement, security professionals, and researchers | Cybersecurity professionals, researchers, and hobbyists |
| Limitations | Limited access to some data sources, primarily focused on link analysis | Limited access to certain devices and systems, not comprehensive for all internet-connected devices |
| Integrations | Integrates with numerous data sources and third-party tools | Integrations with various tools, including Metasploit and Nmap |
| Support | Email support and extensive documentation | Email support and community forums |
Pros and Cons of Maltego
| Pros of Maltego | Cons of Maltego |
|---|---|
| User-friendly: Maltego has a clean and intuitive user interface that is easy to use for beginners. | Limited functionality: The community edition of Maltego only allows for limited data sources and output options. |
| Comprehensive data sources: Maltego has access to many public and private data sources, including social media, domain names, and IP addresses. | Expensive licensing: The commercial editions of Maltego can be quite costly, which may be prohibitive for smaller organizations. |
| Customizable: Maltego allows users to create custom entities and transforms to tailor the tool to their needs. | Steep learning curve: While Maltego is generally easy to use, creating custom entities and transforms can be challenging. |
| Collaborative: Maltego allows multiple users to work on the same investigation simultaneously, making it a useful tool for teams. | Dependence on external data sources: Maltego relies heavily on external data sources, so its usefulness can be limited by the quality and availability of those sources. |
| Visual representation: Maltego’s graph-based visualization allows users to easily see connections between data points, making it easier to identify patterns and anomalies. | Limited scripting capabilities: While Maltego supports scripting, the capabilities are somewhat limited compared to other tools. |
Here are a table listing some of the best OSINT (Open Source Intelligence) tools for social media:-
| Tool Name | Description | Platform | Cost | URL |
|---|---|---|---|---|
| Maltego | A powerful data visualization tool that can be used for OSINT investigations. It lets you map relationships and connections between social media accounts and other online data. | Windows, Linux, Mac | Free, with a paid version available | https://www.maltego.com/ |
| Spiderfoot | A web-based OSINT automation tool that can be used to gather information about social media accounts, including their associated email addresses, phone numbers, and geolocation data. | Web-based | Free, with a paid version available | https://www.spiderfoot.net/ |
| Sherlock | A tool that searches for social media accounts by username across various platforms, including Facebook, Twitter, LinkedIn, and Instagram. | Windows, Linux, Mac | Free | https://github.com/sherlock-project/sherlock |
| OSINT Framework | A collection of OSINT tools and resources, including tools for searching social media sites and platforms. | Web-based | Free | https://osintframework.com/ |
| Creepy | A tool for geolocation-based social media OSINT investigations allows you to see the location of social media users on a map. | Windows, Linux | Free | https://github.com/ilektrojohn/creepy |
| FOCA | A tool for metadata analysis, which can be used to gather information about social media accounts, including their email addresses and IP addresses. | Windows | Free | https://github.com/ElevenPaths/FOCA |
| DataSploit | A tool that automates OSINT investigations, including those involving social media platforms. It can gather information about social media accounts, including their associated email addresses, phone numbers, and geolocation data. | Linux | Free | https://github.com/DataSploit/ds |
Best osint websites
here’s a table outlining some of the best OSINT (Open Source Intelligence) websites:-
| Website Name | Description | URL |
|---|---|---|
| OSINT Framework | A comprehensive collection of various tools and resources for OSINT investigations. | https://osintframework.com/ |
| Intel Techniques | Provides a wide range of free OSINT tools and resources, as well as training courses. | https://inteltechniques.com/ |
| Social Catfish | A reverse image search tool that helps you find social media profiles associated with an image. | https://socialcatfish.com/ |
| Spyse | A cybersecurity search engine that provides OSINT data on IP addresses, domains, and SSL certificates. | https://spyse.com/ |
| Shodan | A search engine for internet-connected devices that provides OSINT data on open ports, services, and vulnerabilities. | https://www.shodan.io/ |
| Maltego | A powerful OSINT tool that allows you to visualize and analyze complex relationships between people, organizations, and other entities. | https://www.maltego.com/ |
| WHOIS Lookup | A tool that provides information about domain registration, including the owner’s name, contact information, and registration date. | https://whois.domaintools.com/ |
| Google Advanced Search | A powerful search tool that allows you to refine your Google search using specific parameters, such as site, filetype, and date range. | https://www.google.com/advanced_search |
| Wayback Machine | A tool that allows you to view archived versions of websites, including past versions of social media profiles. | https://archive.org/web/ |
| TinEye | A reverse image search tool that helps you find where an image has been used online. |
📗FAQ
Who is the competitor of Maltego?
Some competitors of Maltego in the field of open-source intelligence gathering and analysis include Analyst’s Notebook and Palantir.
What can Maltego do?
Maltego is a powerful tool for open-source intelligence gathering and analysis, allowing users to gather information from various sources, visualize that information meaningfully, and identify connections and patterns that might not be immediately apparent.
Is Maltego still used?
Yes, Maltego is still widely used by security professionals, law enforcement agencies, and researchers for intelligence gathering and analysis.
Do employers use Maltego?
Yes, employers in various fields, such as cybersecurity, law enforcement, and intelligence, may use Maltego to conduct investigations, threat intelligence, and other related activities.
What are the limitations of Maltego?
Some of the limitations of Maltego include the need for internet connectivity, reliance on external data sources, and occasional inaccuracies in the data it provides.
Does police use Maltego?
Yes, many law enforcement agencies use Maltego to conduct investigations and gather intelligence.
Is Maltego used for doxxing?
While Maltego can gather information about individuals, it is intended for legitimate use and should not be used for illegal activities such as doxxing.
Is Maltego a good tool?
Yes, Maltego is a highly regarded tool in open-source intelligence gathering and analysis.
Is Maltego a forensic tool?
Maltego is not typically used as a forensic tool, but rather as a tool for intelligence gathering and analysis.
Is Maltego a scanning tool or not?
Maltego is not a traditional scanning tool, but rather a tool for intelligence gathering and analysis.
What is Maltego and how would an attacker use it?
Maltego is a tool for open-source intelligence gathering and analysis. While an attacker could potentially use Maltego for nefarious purposes, the tool is intended for legitimate use and should not be used for illegal activities.
Is Maltego passive or active?
Maltego is a passive tool for open-source intelligence gathering and analysis.
Do you have to pay for Maltego?
Maltego offers both free and paid versions of its software, depending on the level of functionality required.
Why would a security specialist use a tool like Maltego?
A security specialist might use Maltego to gather intelligence on potential threats, identify vulnerabilities, and help prevent security breaches.
Is Maltego a search engine?
Maltego is not a search engine, but rather a tool for gathering and analyzing data from various sources.
What is Maltego in cyber security?
Maltego is a tool for open-source intelligence gathering and analysis that can be used in various aspects of cybersecurity, such as threat intelligence and vulnerability management.
What app does the police use to track your phone?
Law enforcement agencies may use several apps and tools to track phones, including Stingray and GrayKey.
What device do police use to track your phone?
Law enforcement agencies may use various devices to track phones, including specialized software and hardware tools.
Is OSINT legal?
OSINT is generally legal as long as it is obtained from publicly available sources and not used for illegal activities.
How do you know if someone is doxxing me?
You may become aware that someone is doxxing you if you begin to receive unwanted attention, harassment, or threats online, or if you notice that personal information about you has been made public.
Does a VPN protect you from doxxing?
Using a VPN can help protect your online anonymity and prevent your IP address from being tracked, but it may not necessarily protect you from doxxing if the person doing it can obtain your personal information through other means.
Which is better SpiderFoot or Maltego?
SpiderFoot and Maltego are powerful tools for open-source intelligence gathering and analysis, but which one is better depends on the user’s specific needs and use case.
What is the alternative to Maltego in Kali?
Kali Linux, a popular distribution of Linux for penetration testing and cybersecurity purposes, includes several alternatives to Maltego such as Recon-ng and theHarvester.
What is Kali Maltego?
Kali Maltego refers to the version of Maltego included in the Kali Linux distribution.
What are the 5 forensic databases?
There are many forensic databases used by law enforcement and other organizations.
Still, five common ones include the National DNA Index System, the Integrated Automated Fingerprint Identification System, the Combined DNA Index System, the National Integrated Ballistics Information Network, and the National Crime Information Center.
What is the most reliable forensic tool?
The most reliable forensic tool depends on the specific needs and use case of the user. There are many reputable forensic tools available, such as EnCase and FTK.
What is the best security scanning services?
Many reputable security scanning services are available, such as Nessus and Qualys.
What is best auto scan tool?
There are many reputable auto scan tools available, such as OpenVAS and Nikto.
Is Maltego a footprinting tool?
Maltego can be a footprinting tool to gather information about an organization’s online presence and potential vulnerabilities.
How powerful is Maltego?
Maltego is a powerful tool for open-source intelligence gathering and analysis, allowing users to gather information from various sources and identify connections and patterns that might not be immediately apparent.
How do hackers perform reconnaissance?
Hackers perform reconnaissance by gathering information about their target, such as their online presence, potential vulnerabilities, and employee information.
What is commonly used in reconnaissance attacks?
Common tools and techniques in reconnaissance attacks include port scanning, open-source intelligence gathering, and social engineering.
Is Osint a passive or active reconnaissance?
OSINT is typically a passive form of reconnaissance, as it involves gathering information from publicly available sources rather than actively probing a target’s systems.
What is a transform Maltego?
A transform in Maltego is a plug-in that enables the software to gather information from a specific data source or perform a specific action.
What is footprint L1 machine on Maltego used for?
Footprint L1 Machine is a Maltego transform that is used to gather information about an organization’s online presence and potential vulnerabilities.
What is the difference between Maltego Pro and Enterprise?
The main difference between Maltego Pro and Enterprise is the functionality and support available. Enterprise offers additional features and support, but at a higher cost.
Is Maltego free for students?
Maltego offers a free academic license for students and educators using the software for educational purposes.
Where is Maltego based?
Maltego is based in South Africa.
How long does IT take to learn OSINT?
The amount of time it takes to learn OSINT can vary depending on the individual’s prior experience and knowledge, but it typically requires ongoing learning and practice to become proficient. Many resources are available for those looking to learn OSINT, including online courses, books, and tutorials.
What are Maltego limitations?
Some of the limitations of Maltego include its reliance on external data sources, occasional inaccuracies in the data it provides, and the need for internet connectivity.
Can police see if your phone is being tracked?
Law enforcement can determine if your phone is being tracked, but this typically requires a court order or other legal process.
What is stingray surveillance?
Stingray surveillance is a controversial law enforcement practice involving a device that mimics a cell phone tower to intercept cellular signals and track the location of targeted devices.
How do you tell if feds are following you?
It can be difficult to tell if you are being followed by law enforcement, but some signs to look out for include suspicious vehicles, repeated sightings of the same person, and unusual behavior from those around you.
What is the dark side of OSINT?
The dark side of OSINT refers to the potential for the information gathered through open-source intelligence gathering to be used for malicious purposes, such as doxxing, cyberstalking, and identity theft.
Does the CIA use OSINT?
Yes, the CIA and other intelligence agencies use open-source intelligence gathering and analysis as part of their operations.
How much does OSINT cost?
The cost of OSINT varies depending on the specific tools and resources used, but many free and low-cost options are available.
Is doxing illegal in the US?
Doxing can be illegal in the US if it involves releasing private, personal information intending to harass, intimidate, or harm an individual.
How illegal is it to dox someone?
Doxing is illegal if it involves the release of private, personal information with the intent to harass, intimidate, or harm an individual. The severity of the crime depends on the specific circumstances.
Can the government spy on me if I use a VPN?
Using a VPN can help protect your online anonymity. However, it is still possible for the government or other entities to track your online activity through other means, such as surveillance or monitoring your internet traffic.
What is better than Maltego?
Given that user demands and preferences will change depending on the tasks and objectives they are attempting to do, it is challenging to determine what is “better” than Maltego.
Certain users could favor particular OSINT (Open-Source Intelligence) programs for various reasons.
The following OSINT tools compare favorably to Maltego:-
The Harvester:- With the help of this program, you may collect email addresses, names, and subdomains from various places, including search engines, PGP keyservers, and the Shodan search engine.
Recon-ng:- This tool is intended to automate the recon process and obtain open-source intelligence. It has several modules for acquiring information from numerous sources, including social media, domain registrars, and blacklists.
Shodan:- With the use of this search engine, people may look up specific details about servers and gadgets that are online and search for them. Its applications include vulnerability analysis and open-source intelligence gathering.
SpiderFoot:- Through the use of this free and open-source intelligence-gathering tool, users can learn details about a target from a variety of sources, including social media, domain registrars, and blacklists.
Is Maltego open source?
Yes, Maltego is an open-source software tool. As it is known, it is an open-source intelligence (OSINT) tool and not an open-source project. It is a kind of intelligence collection management tool that selects, finds and acquires information from publicly available sources.
What is SpiderFoot used for?
SpiderFoot is an effective tool that may be used for many different things, including research, security, information gathering, and investigation.
SpiderFoot and other OSINT tools should, however, be used properly and by the rules and legislation that apply to the usage of open-source data.
Is there a free version of Maltego?
The Maltego has the Maltego Community Edition (CE), the free version of the Maltego Desktop Client. The app provides you with a fast method to get started, and the CE edition comes with its limited capabilities. Users can carry out OSINT and graphical link analyses.
Is Maltego a forensic tool?
Maltego cannot be termed as a forensic tool. But it is a data mining tool used in forensics and intelligence. It helps analyze and determine the relationships between entities like documents, people, websites, and files.
How Maltego is used in real-time applications?
Maltego is used in real-time applications, including social network analysis, infrastructure mapping, asset searching and tracing, social media data analysis, and more.
Can I use Maltego on Windows?
Maltego is quick to install and works with the help of Java. That means it can also work on Mac, Windows, and Linux. It would help to ensure that the PC device or laptop meets the minimum requirements.
What is Maltego in security?
Maltego is software that can be used for open-source intelligence and forensics. You will be glad to know that it was designed by Paterva, South Africa. The tool aims to offer to you information from open sources, ideal for link analysis and data mining.
What is Maltego, and how would an attacker use it?
Since Maltego is an OSINT to gather information, attackers do not stand a chance when they are against it. You can be assured that your PC device or laptop is safe from attack. You can download and use it securely.
What is OSINT analysis?
The process of compiling, examining, and interpreting material legally accessible from open sources or otherwise available to the public is known as OSINT (Open-Source Intelligence) analysis.
An in-depth understanding of a certain topic, person, group, or event can be developed through OSINT analysis.
OSINT analysis can be used for several things, including:-
Research:- Research activities like studying a certain subject or comprehending the context of an event can benefit from information gathered through OSINT analysis.
Security:- By identifying potential threats or vulnerabilities, OSINT analysis can be utilized to identify and reduce security concerns.
Intelligence:- To support operations or acquire intelligence for strategic decision-making, OSINT analysis may be used.
Investigation:– Investigative tasks like finding suspects or acquiring evidence can be supported by OSINT analysis.
Several technologies and methods, including search engines, social media platforms, open databases, and other internet resources, are used in OSINT analysis.
It calls for analytical thinking, close attention to detail, and knowledge of how to use and interpret the information acquired.
Is Maltego an OSINT tool?
Maltego is a tool for OSINT (Open-Source Intelligence). It is an open-source intelligence collecting and data mining application that enables users to collect and analyze data from various sources.
Maltego’s users can create a thorough understanding of a specific subject, person, group, or event by using it to grasp the connections between various elements.
Users can collect information from websites like social media, domain registrars, and blacklists, visualize the information in a graphical style, and then evaluate it.
Maltego is frequently employed for scientific study, security, intelligence, and investigative applications. It is an effective tool that enables users to quickly and easily collect and analyze enormous amounts of data from public sources.
Maltego and other OSINT tools should be used appropriately, and users should be aware of the rules and legislation regulating how open-source data may be used.
Conclusion
We can understand your pain while analyzing and transforming the information if you are a data investigator or analyst. Data visualization and analysis can be complex; however, the internet has eased data analysis.
You can find numerous software on the internet to assist you with data analysis, but most are spam, and only a few offer genuine services.
As discussed earlier, Maltego is one of the most trusted platforms that offer all kinds of data-related services, including data gathering and analysis.
It is an excellent open-source data-analyzing application that offers active data interpretation and threat detection. However, the platform’s service charges are a bit expensive, so most investigators and data analysts don’t prefer using it.
If you were searching for an alternative to Maltego, we hope your search has ended with this article.
Here, we have provided a list of some excellent Maltego alternatives that provide excellent data analysis services. You can choose any of the software mentioned above as per your requirements.
You can choose Gephi or SpiderFoot, which offers unique visualizing features, or you can opt for Linkurious, which offers an on-spot graphical representation of data, or Visallo which actively detects fraudulent activities.