Do you find yourself constantly juggling long, complex PowerShell commands in your scripting endeavors?💁
Are you looking for a way to streamline your code and enhance its readability? Look no further!
In this article, we delve into the world of PowerShell splatting, an ingenious technique that will revolutionize how you write PowerShell scripts.
PowerShell splatting is a lesser-known gem in scripting, often overlooked by novice users. However, for those who have mastered it, splatting is a powerful tool that can significantly simplify code, increase its maintainability, and make it more efficient.
Whether you’re a seasoned PowerShell guru or just getting started, understanding and harnessing the power of splatting can take your scripting skills to the next level.
In this comprehensive guide, we will demystify PowerShell splatting, break down its key concepts, and explore real-world examples that showcase its effectiveness.
By the end, you’ll be equipped with the knowledge and confidence to employ splatting techniques in your own scripts, reaping the benefits of cleaner, more organized code.
So, if you’re ready to unlock the full potential of PowerShell and enhance your scripting prowess, let’s dive into the fascinating world of PowerShell splatting and unleash the power of code efficiency!
What is PowerShell Splatting?💁
PowerShell, the versatile scripting language and automation framework from Microsoft, offers a wealth of powerful features to streamline administrative tasks and enhance productivity.
Among its many capabilities, one technique stands out for its ability to simplify and optimize code: PowerShell splatting.
PowerShell splatting is a technique that allows you to pass a collection of parameters to a cmdlet or function by using a single variable.
Instead of specifying each parameter individually, you can store them in a hash table, known as a splatting variable, and pass it as an argument.
This not only improves the readability of your code but also offers a more organized and efficient approach to parameter management.
By leveraging splatting, you can avoid the clutter of long command lines, reduce the chances of errors, and enhance code maintainability.
It allows you to group related parameters together, making your scripts easier to understand and modify. Moreover, splatting enables you to selectively include or exclude specific parameters during execution, offering flexibility and control.
To utilize PowerShell splatting, you create a hash table with parameter names as keys and their corresponding values.
Then, you use the “@” symbol followed by the splatting variable name to pass the hash table as an argument.
This technique is particularly useful when dealing with commands that require a multitude of parameters, making it a valuable tool for scripting complex tasks efficiently.
Understanding PowerShell Splatting and How it Functions?
To comprehend PowerShell splatting, it is important to pay attention to the fundamental parameters. When passing parameters to a PowerShell command, users typically use a dash followed by the parameter name, and then the argument, as seen below.
Copy-Item -Path "TestFile1.txt" -Destination "CopiedFile1.txt" -WhatIf -Force
An alternative would be to use backticks to pass parameters as shown below:
Copy-Item ` -Path "TestFile1.txt" ` -Destination "CopiedFile1.txt" ` -WhatIf ` -Force
The conventional way of providing parameters is great, but with numerous parameters, it quickly becomes cumbersome to work with and it could be hard to read and comprehend.
The use of a backtick, “`, seems to improve readability significantly. Due to the ease with which a backtick may be forgotten or misplaced, this method is generally not advised.
Instead, PowerShell splatting may be used. The process would involve creating a hashtable with key/value pairs for each parameter and creating the parameter argument. Then, after you’ve created the hashtable, use @<hashtable name> to give that set of arguments to the command.
As an example, you might construct a hashtable named $Vals and then use the Copy-Item cmdlet to provide that hashtable’s set of arguments to the Copy-Item cmdlet, as seen below.
$Vals = @{ "Path" = "TestFile1.txt" "Destination" = "CopiedFile1.txt" "WhatIf" = $True "Force" = $True } Copy-Item @Vals
Merging Conventional and Splatting Parameters
Users may simply mix the two techniques when testing scripts or while using the command line. When working with scripts, it’s common to construct a splatted variable for the purpose of assigning to the function or cmdlet. Here’s is what this could look like:
$Vals = @{ "Path" = "TestFile.txt" "Destination" = "CopiedFile.txt" } Copy-Item @Vals -Force -WhatIf
As the example shows, this is a really handy approach that allows users to a new alternative depending on their needs. By combining methods, users may test an extra parameter or structure the parameters differently for formatting.
How to Override Splatted Parameters
It is bow possible to override splatted arguments in PowerShell 7.1. Previously, users couldn’t use a passed argument to change a splatted parameter. Consider the splatted parameter overriding example below where I override the -WhatIf parameter.
$Vals = @{ "Path" = "TestFile1.txt" "Destination" = "CopiedFile1.txt" "WhatIf" = $True "Force" = $True } Copy-Item @Vals -WhatIf:$False
Overriding splatted arguments enables users to ignore the hashtable’s key/value parameter and instead use the value of the conventionally specified parameter.
Positional Parameters Splatting Arrays
Using named parameters is considered best practice since it requires you to provide the parameter name followed by a parameter argument. You may, however, splat parameters by location as well.
If users want to transfer a file named TestFile1.txt to a file called CopiedFile2.txt, for example, they may use positional arguments like the ones below.
Copy-Item 'TestFile1.txt' 'CopiedFile1.txt'
Users may construct an array (rather than a hashtable) using just the parameter values instead of providing positional arguments in an old-fashioned manner. You can see a model of this below.
$ValArray = @( "TestFile1.txt" "CopiedFile1.txt" ) Copy-Item @ValArray
Though not often used, this approach may be helpful since it provides a less verbose way of supplying splatted arguments.
Keep in mind that you must be aware of the locations of the arguments in a particular function or cmdlet; otherwise, you risk sending data to improperly targeted parameters.
Splatted Commands and Proxy Functions
Often a PowerShell cmdlet isn’t exactly what you’re looking for. Users might construct a “wrapper” function or a proxy function in this situation.
These functions enable a user to add new arguments to an existing cmdlet before calling it with the new parameters.
Introducing $Args and $PSBoundParameters
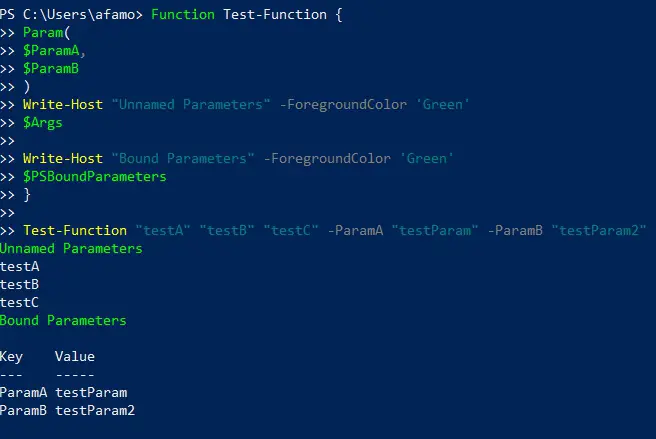
When we execute a PowerShell script, it automatically generates an array variable named $Args. All unnamed argument values provided to the function are stored in this array.
Some other automated variable named $PSBoundParameters includes a hashtable containing the bound parameters. The Test-Function function will return the $ParamA and $ParamB arguments, as seen below.
Function Test-Function { Param( $ParamA, $ParamB ) Write-Host "Unnamed Parameters" -ForegroundColor 'Green' $Args Write-Host "Bound Parameters" -ForegroundColor 'Green' $PSBoundParameters } Test-Function "testA" "testB" "testC" -ParamA "testParam" -ParamB "testParam2"
What role do automatic variables play in the splatting process? Automatically handling inbound and unbound arguments is extremely helpful when constructing a proxy command.
How to Use Splatted Parameters in Creating Wrapper Functions
Create a unique script that sends named and unnamed arguments to the Copy-Item cmdlet to demonstrate how beneficial splatting can be in wrapper functions. You may easily build new functions using this approach that provides extra functionality while keeping the same parameter set as before.
Function Copy-CustomItem { Get-ChildItem Copy-Item @Args @PSBoundParameters Get-ChildItem }
It’s essential to keep in mind that when we make use of the CmdletBinding declaration or specify argument characteristics, the automatic variable $Args disappears.
Combining Traditional Parameters and Splatting in PowerShell
When it comes to writing efficient and flexible PowerShell scripts, the combination of traditional parameters and splatting can be a game-changer.
This approach allows you to harness the benefits of both techniques, empowering you to create versatile and maintainable code.
Traditional parameters are the familiar variables used in PowerShell functions and cmdlets. They provide a straightforward way to pass values to your script and define specific inputs. These parameters have explicit names and data types, making them easy to understand and use.
On the other hand, splatting enables you to group parameters together in a hash table, providing a more concise and organized way to pass multiple values to a command.
By using a splatting variable, you can simplify the invocation of a cmdlet or function and improve code readability.
The real power lies in combining these two approaches. By using traditional parameters alongside splatting, you can achieve a fine balance between flexibility and clarity.
You can define essential parameters as traditional ones, ensuring their explicit handling, while using splatting for optional or dynamic parameters, granting you the freedom to pass multiple values in a single stroke.
This combination allows you to maximize the reusability and maintainability of your code. It simplifies the process of invoking your script while maintaining granular control over the inputs.
You can modify and extend your script without compromising its readability or breaking existing functionality.
Here’s an example of combining traditional parameters and splatting in PowerShell:-
# Define a function with traditional parameters
function Get-User {
param (
[Parameter(Mandatory=$true)][string]$Name,
)
# Function logic here
Write-Host “Name: $Name”
if ($Email) {
Write-Host “Email: $Email”
}
if ($Department) {
Write-Host “Department: $Department”
}
}
# Define a hashtable with parameter names and values
$parameters = @{
Name = “John Doe”
Email = “john.doe@example.com”
Department = “IT”
}
# Call the function using splatting
Get-User @parameters
In this example, the Get-User function has three traditional parameters: Name, Email, and Department. The Name parameter is marked as mandatory, while the other two are optional.
We then define a hashtable called $parameters with the parameter names (Name, Email, Department) as keys and their corresponding values. By using the @ symbol before the hashtable variable (@parameters), we pass the hashtable as a set of named parameters to the Get-User function.
This approach allows us to pass a dynamic set of parameters to the function without explicitly specifying them in the function call. You can modify the hashtable as needed, including or excluding parameters, based on your requirements.
By combining traditional parameters and splatting, you can create more flexible and reusable code that can adapt to different scenarios.
Last Thoughts
Congratulations! You have successfully completed your journey into the realm of PowerShell splatting. Armed with this newfound knowledge, you now possess a powerful technique to simplify and optimize your PowerShell scripts.
Throughout this article, we’ve explored the fundamental concepts of splatting, its advantages, and real-world examples that highlight its effectiveness.
By leveraging splatting, you can eliminate the clutter of lengthy command lines and embrace a cleaner, more readable codebase.
Not only does this make your scripts easier to understand, but it also enhances their maintainability, enabling you to make updates and modifications with confidence.
Remember, PowerShell splatting is not just reserved for the advanced users—it is a technique that can benefit everyone, from beginners to seasoned professionals.
Regardless of your scripting experience, incorporating splatting into your PowerShell repertoire will undoubtedly save you time and effort in the long run.
As you continue your scripting journey, don’t hesitate to experiment and explore the vast possibilities that splatting offers. The more you practice and implement this technique, the more proficient you will become in harnessing its full potential.
With your newfound knowledge of PowerShell splatting, you are now equipped to streamline your code, boost your productivity, and elevate your scripting game to new heights.
So go forth, embrace splatting, and unleash the power of code efficiency in your PowerShell scripts!
Remember, the true power of splatting lies in its simplicity. By organizing your parameters and arguments, you’ll not only improve the readability of your code but also unlock a whole new level of efficiency.
So, why wait? Start using PowerShell splatting today and experience the transformative impact it can have on your scripting journey.
PowerShell splatting is your secret weapon to conquer complexity and elevate your scripting skills. So, seize the opportunity, embrace splatting, and take your PowerShell scripting to new horizons.
Happy scripting!