Implementing business processes using IaC is becoming increasingly common in DevOps environments (Infrastructure as Code). Modern IaC tools make it easier to configure servers and fix problems faster.
Two of the most common IaC tools, Ansible and Terraform, are there to help companies as they can be scaled up or down when needed effortlessly.
So, they are one of the best software deployment options and are extremely popular. Terraform vs Ansible is a hot topic in today’s DevOps market.
What is Terraform?🤷♂️
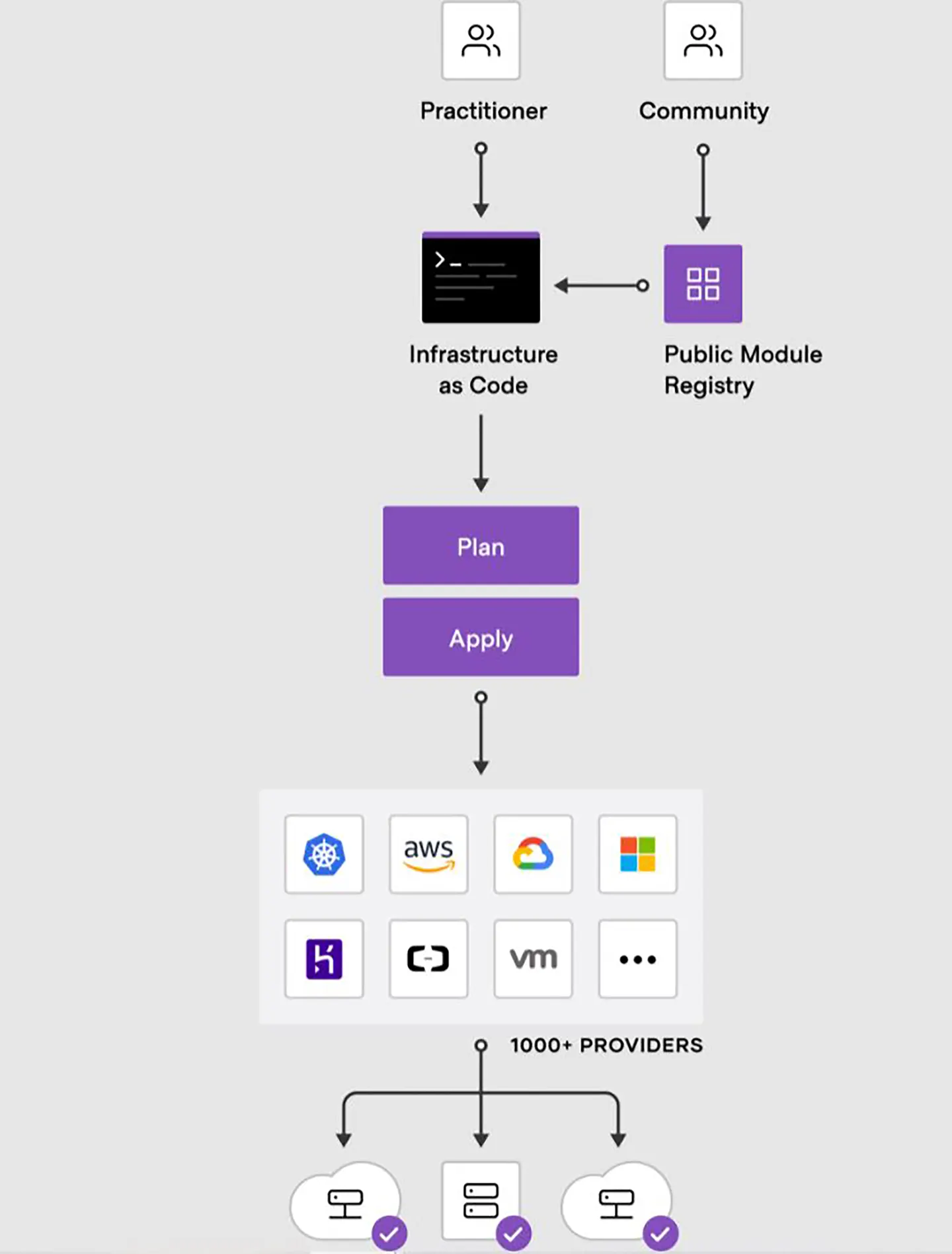
Developed by HashiCorp in 2014, Terraform is an open-source Infrastructure as a Code solution. It is declarative, meaning you write the code at a high level, and Terraform will execute the rest.
In the HashiCorp Configuration Language, the code is written. More than 200 infrastructure providers use Terraform, including public, private, and SaaS clouds.
The final state is only visible at the provider end due to the declarative nature of the code. The final state will be visible on the AWS cloud, for example. Terraform users need prerequisite scripts and virtual gadgets to use the deployed software.
Also, Terraform supports infrastructure orchestration, utilizing execution plans-basically, steps to be performed in an orderly fashion-and Resource graphs-a visual representation of the plan’s execution schedule.
An overview of resources on the stack is sufficient for Terraform engines to quickly spin up the infrastructure without the need for detailed programming.
This means that Terraform’s code is declarative, which defines the process by which results may be achieved.
Terraform is an excellent tool for automating resource provisioning processes and can also be used to migrate to the cloud. With its command-line interface, infrastructure can be deployed quickly.
Additionally, it can perform versioning and infrastructure changes, making it an ideal tool for managing clouds.
In addition to offering a large support base, Terraform allows for flexible configurations that may include a variety of service providers in addition to in-house services.
Terraform, which supports a variety of cloud providers, can be a great cloud management solution for Multicloud.
Even though it is declarative, allowing you to manage high-level instances such as SaaS and DNS, it can still manage low-level instances such as storage and network hardware. This parallel computing power is made possible by Terraform’s multi-threaded nature.
Listed below is a quick and easy summary of Terraform’s features:-
- Terraform simplifies the initial deployment process, making it quick and simple as a declarative Infrastructure as a Code platform.
- Work is easier to collaborate on when code is modular. In addition to being reusable, modular code can be easily customized for specificity.
- Terraform includes a convenient tool for displaying the resulting model in a graphical format.
- Only a handful of infrastructure-building tools can be used to build infrastructure from the ground up, whether in a single public cloud or multiple private clouds.
What is Ansible?🤷♀️
Use Infrastructure as a Code, Ansible is an open-source configuration management tool with software provisioning and application-deployment capabilities.
It has a declarative language for describing system configurations unique to the platform.
SSH or Windows PowerShell perform Ansible tasks, making managing large enterprise deployments simple. Calling Ansible just declarative is incorrect as it inherits declarative and procedural traits.
Using Ansible, you can execute ad-hoc commands, allowing for procedural and declarative configurations.
As mentioned earlier, the primary use of Ansible is to deploy the applications that the client will install on their system.
Ansible performs tasks such as installing and managing installation packages, starting services, and running scripts or config files on server instances.
Because it is used for configuration management on already deployed servers, Ansible uses IaaC.
Note:- A large enterprise with interconnected applications cannot use Ansible as an orchestration tool. Sometimes, this point can dissolute all the points made in this article, Terraform vs Ansible.
Below is a quick list of Ansible’s features:-
- Using the procedural paradigm, Ansible is used primarily for configuration management.
- Ansible uses IaaC to configure systems across the entire infrastructure.
- Allows you to deploy multi-tier apps quickly and easily while being agentless.
- Ansible re-entrant code can be interrupted and re-entered without interfering with other invocations.
Terraform vs Ansible: What’s the difference?
Here’s a detailed table comparing Terraform and Ansible.
| Criteria | Terraform | Ansible |
|---|---|---|
| Purpose | Terraform is a tool for provisioning and managing infrastructure resources. It focuses on infrastructure-as-code (IaC) and enables the management of cloud resources in a declarative way. | Ansible is a tool for automating software provisioning, configuration management, and application deployment. It focuses on task-based automation and enables the management of servers and applications. |
| Language | Terraform uses HashiCorp Configuration Language (HCL) for writing code. HCL is a declarative language that is easy to read and write. | Ansible uses YAML for writing code. YAML is a human-readable data serialization language. |
| Architecture | Terraform follows a client-server architecture. It has a local CLI that communicates with the Terraform Cloud or Terraform Enterprise. | Ansible follows a client-server architecture. It has a central management node called the control node that communicates with the managed nodes. |
| Resources | Terraform manages infrastructure resources such as virtual machines, databases, and networking. It supports all major cloud providers, including AWS, Azure, and Google Cloud. | Ansible manages servers, applications, and other software components. It can manage resources on various platforms, including Linux, Unix, Windows, and networking devices. |
| State Management | Terraform uses a state file to track the current state of infrastructure resources. The state file is used to plan and execute changes to the infrastructure. | Ansible uses modules to perform tasks on the managed nodes. The modules are idempotent, meaning they can be executed multiple times without changing the system’s state. |
| Execution | Terraform executes changes to the infrastructure in a planned and controlled way. It uses a plan file to preview changes before applying them to the infrastructure. | Ansible executes tasks on the managed nodes in an ad-hoc or playbook-based manner. Playbooks are used to define a series of tasks and apply them to the system. |
| Community | Terraform has a large and active community that provides support and contributes to the development of the tool. It also has a rich ecosystem of plugins and modules. | Ansible has a large and active community that provides support and contributes to the development of the tool. It also has a rich ecosystem of modules and roles. |
| Learning Curve | Terraform has a moderate learning curve. It requires some knowledge of cloud infrastructure and the HCL language. | Ansible has a steep learning curve. It requires knowledge of Linux system administration, YAML, and the Ansible module ecosystem. |
| Scalability | Terraform is highly scalable. It can manage infrastructure resources at any scale, from a single virtual machine to complex multi-cloud deployment. | Ansible is less scalable than Terraform. It can manage many servers and applications but may struggle with complex multi-cloud deployments. |
| Cost | Terraform has a free, open-source version that can manage infrastructure resources. It also has a paid version called Terraform Enterprise that provides additional features and support. | Ansible is free and open-source. There are no additional costs for using Ansible. |
Terraform vs Ansible: Working
How does Terraform work?
In Terraform, there are primarily two working components.
- Terraform core
- Providers
Terraform has a declarative nature. It is declarative language. It describes services and resources at a high level of abstraction.
Terraform core requires two input sources to perform its function properly. Terraform configurations are the first input source. Users create terraform configurations. The users define provisioning and creation.
Terraform core analyses the input and determines the steps to achieve a result.
Providers, A plethora of providers are at play here, be it Amazon for its AWS or Microsoft for its Azure; you need them all, both cloud and Infrastructure service providers.
Infrastructural development is facilitated at various levels. Using AWS infrastructure as an example, imagine users creating Kubernetes on top of it and then creating services within the cluster.
It is possible to access resources from Terraform’s providers for a wide range of different technologies.
How does Ansible work?
Ansible needs to create a connection, usually using SSH and other secure methods. JSON is a module with simple instructions executed on the target computer or device to install Python.
After completing their tasks, these modules are executed and removed from the computer. As a result of this strategy, no resources are wasted on the target. As a result, Python must be installed on both the target and the controlling nodes.
As the playbook’s controlling node, Ansible’s management node controls its execution. The hosts on which the modules need to be run are listed in the inventory file.
The management node establishes SSH connections with the host machine to execute modules and install the product.
Modules are removed from the system once they have been installed. This is Ansible’s simple working process.
Terraform vs Ansible: Features
Features of Terraform:-
Terraforms features will be discussed now that we’ve discussed Terraforms operation.
- According to Terraform’s declarative approach, deploying applications is quick and easy.
- One of the features of Terraform is that it can be used to represent it in a graphical format.
- If you want to build a cloud infrastructure from scratch, it’s one of the few tools that does it.
- Coding in modules promotes consistency, reuse, and collaboration.
- Terraform can manage multiple clouds to increase fault tolerance.
Terraform Lifecycle:-
Init, plan, apply, and destroy are the stages of the Terraform lifecycle.
- All configuration files are created when Terraform init is run.
- Using Terraform plan, you can create a detailed execution plan for achieving a specific infrastructure state. To reach the destinations, the configuration file was altered.
- According to the plan, Terraform applies and makes any necessary changes, resulting in a finished product.
- All old infrastructure resources marked tainted after the application phase are deleted with Terraform destroy.
Features of Ansible:-
We’ll now discuss some of the features Ansible offers to its users.
- A procedural approach is taken when using Ansible for configuration management.
- In addition to bare metal and cloud networks, Ansible also deals with hypervisor-based virtualized devices.
- The behavior is called immutability whenever Ansible places a node in the same state.
- System configuration is shared across the infrastructure using Infrastructure as a Code.
- The code can be resumed if it is interrupted.
Terraform vs Ansible: Provisioning
Terraform is a platform for automating infrastructures. Its current declarative model lacks certain features, which add to the program’s complexity.
Each element of a required environment is described separately, including their relationships, using Terraform. Infra as a Service is given optimized commands after the model is assessed.
Repeated runs will have no effect if the environment or strategy does not change. The cloud infrastructure is updated whenever there is a change to the plan or environment.
Ansible takes a procedural approach to development. Playbooks are created for deep analysis and evaluation and to execute the task sequentially.
Using playbooks allows network devices to be configured procedurally. The cloud infrastructure is, of course, also provisioned using Ansible.
On the other hand, its procedural approach limits it to large-scale infrastructure deployments.
Terraform vs Ansible: Procedural vs Declarative
By examining how they work, we can make the most accurate comparison between the two tools under discussion.
Let’s look at the differences between Terraform and Ansible based on procedural or declarative processes before asking, “Why Ansible?” Procedural and declarative tools are the two main categories of DevOps tools.
Though procedural and declarative categories are defined briefly, many tools meet both requirements. It is a procedural application. Determining the number of instances is required when scaling up the EC2 instances.
The process of downscaling instances in Amazon EC2 differs greatly from this. For a better understanding, we can return to the orchestra scenario.
Professional tools are similar to a conductor who demands five guitars only to receive five more.
No matter what process is used to achieve the desired results, declarative tools provide a clear picture of the requirements.
There are 5 guitars in the orchestra, and the conductor still has 5 guitars after a performance in this case. Please specify the exact number of EC2 instances you require in the real world.
These categories and the nature of the tools within them are now crystal clear to us. Exactly what does this mean to you? Terraform, as you can see, meets the criteria for decorativeness.
Terraform requires that you define the environment precisely, and “Terraform Apply” can be used to correct any changes made to the environment as a result of your efforts.
Why, then, Ansible, are you doing this? As a result, Ansible is a hybrid of procedural and declarative programming languages. For procedural configuration, you could issue ad hoc commands.
Other options include using Ansible modules that perform declarative configuration.
Which one to choose: Terraform or Ansible?
Every tool these services offer has different purposes and pros and cons. So, it is vital to have know-how on them before deciding.
As well as having excellent scheduling capabilities, Terraform is extremely user-friendly. This is because Terraform’s configuration management is slightly better than Docker’s. The procedure to bring the target devices to their final configuration is unclear.
Improved security and ACL functionality are included in Ansible. Due to its compatibility with traditional automation frameworks, it is regarded as a mature product.
It allows for simple operations and helps coders to work more quickly and efficiently with the language. And yet on the other hand, logical dependencies, orchestration, and interconnected applications are not well served by it.
Both options are now available for you to choose from, depending on the situation and the job. Terraform is preferable, for example, if the containerized solution is used to provision software in the cloud.
In contrast, Ansible is more suitable if you want to gain reasonable control over your devices and find alternative ways to deploy underlying services. They will be used in the future to develop more comprehensive solutions.
Terraform and Ansible Provisioning: What’s the difference?
Terraform vs Ansible: Orchestration or Configuration Management
Terraform and Ansible are most comparable in terms of their applications. The most important thing to remember is that both of these applications are similar, albeit with some differences.
Orchestration and configuration management are two key DevOps concepts that distinguish these tools.
As such, these terms are ideal for describing the functions of certain tools. As a configuration management tool, Ansible is used by many organizations. Terraform is a tool that allows you to orchestrate your application’s resources.
Even though configuration management and orchestration share many functionalities, the differences are significant.
A clear understanding of the differences between these tools can aid in selecting the most appropriate applications based on their strengths and weaknesses.
Terraform and Ansible have both placed their cards on the table. Consider the pros and cons of each tool to determine who wins.
This aspect of the Terraform vs Ansible battle can be better understood by examining a practical example. Pretend they’re both parts of a band of musicians.
Terraform, a tool for orchestration, serves as the orchestra’s manager or conductor. When it comes to instruments, the conductor has the final say.
Additionally, the conductor ensures that all of the instruments are playing properly. A malfunctioning instrument can be removed by the conductor and replaced with a properly functioning instrument.
Because of this focus on final objectives, we can see that orchestration tools like Terraform are very effective. Terraform places a high value on maintaining a certain state of the environment.
A better disaster recovery foundation is provided by Terraform, which stores the ideal state of the environment. Terraform can automatically provide the resource if there is a discrepancy when it is re-run.
When asked “Why Terraform?” people need to know that it is the ideal tool for maintaining stable environments. It’s as simple as selecting “Terraform Apply” whenever an issue arises with the environment.
In this Ansible vs Terraform battle, let’s focus on Ansible. Ansible is a configuration management tool, as we all know. In an orchestra, a configuration management tool’s role is similar to that of a technician who fixes broken instruments.
A configuration management tool like Ansible keeps an environment in working order.
Each instrument must be in tune, working properly, and free of damage. A configuration management tool, Ansible, is used to fix problems rather than replace the entire infrastructure.
Amusingly, Ansible also has some orchestration capabilities built-in. As a result, it is a hybrid. As a configuration management tool, Ansible performs best.
Terraform, on the other hand, excels at state management. Consequently, the main difference between the two IAC tools is their DevOps configuration management and orchestration functionalities.
Let us know about Terraform vs Ansible with the help of the given information.
| Terraform | Ansible |
| Terraform is a tool for setting up infrastructure. | As a configuration management tool, Ansible is used by many organizations. |
| A declarative Infrastructure as a Code approach is used in its implementation.
|
It is primarily used to configure servers with the correct software and update resources already set up on the server.
|
| In addition to orchestrating cloud services, it can also be used to create a cloud infrastructure from nothing. | It is primarily used to configure servers with the correct software and update resources already set up on the server.
|
| Terraform by default does not support provisioning bare metal. | Servers can be provisioned using Ansible.
|
| In terms of packaging and templating, it does not provide better support. | Packaging and templating are supported to the fullest extent possible.
|
Infrastructure as Code
It refers to defining (usually) virtualized infrastructure in a declarative model defined in text files that can be stored in conventional version control systems common to software engineering.
In conjunction with a cloud orchestrator, the virtualized infrastructure configuration is kept up-to-date with changes as they occur in the configuration files (i.e., the “code”)
Immutable Infrastructure
In an immutable infrastructure, components are replaced rather than their configurations changed. A common problem when modifying configuration over time is configuration drift and snowflake servers, which can be addressed using this approach.
It will instead create a new instance with the new configuration, switch traffic to it, and then switch over instead of changing the configuration.
However, this isn’t realistic for frequently reconfigured components such as firewalls. Terraform is more compatible with this approach than the other two products.
A perfect answer to the question, “Why Terraform?” or “Why not Ansible?”
Depends in large part upon what you want to accomplish with it. Both tools have many similarities and some differences, which are worth noting.
Which one do you think is the best in Terraform vs Ansible?
Ansible is recommended for configuration management and Terraform orchestration from a practical perspective. Terraform’s primary purpose is orchestration, and it’s remarkably intuitive to use.
Terraform updates are ideal for orchestration, as you’ll see. Terraform Plan can also provide more useful information than Ansible –dry-run.
Ansible, on the other hand, is your ideal configuration management tool. Please be aware that Ansible has certain limitations regarding orchestration tasks.
📗FAQ
Which is better, Terraform or Ansible?
Terraform and Ansible are both excellent tools with their strengths and weaknesses. Terraform is great for provisioning infrastructure and managing cloud resources, while Ansible is a powerful configuration management tool. Which tool is better depends on your specific needs and use case.
What is the difference between Ansible and Terraform?
The main difference between Ansible and Terraform is that Ansible is a configuration management tool that focuses on automating the deployment and configuration of software.
At the same time, Terraform is an infrastructure as a code tool that focuses on automating infrastructure provisioning and management.
Should I learn Terraform or Ansible?
Terraform and Ansible are popular and widely used tools in the DevOps ecosystem. Learning either tool is a valuable investment in your career.
If you’re looking to manage cloud resources and infrastructure, Terraform might be the better choice. If you’re looking to automate configuration management tasks, Ansible might be the better choice.
What is the difference between Terraform and Ansible, and Puppet?
Terraform, Ansible, and Puppet are all infrastructure as code tools but have different focuses. Terraform focuses on provisioning and managing infrastructure, while Ansible and Puppet focus on configuration management. Ansible is agentless, while Puppet requires an agent installed on the target nodes.
Why use Terraform over Ansible?
Terraform is better suited for provisioning and managing infrastructure than Ansible. Terraform’s robust provider ecosystem allows you to manage resources across multiple cloud providers, while Ansible’s provider support is more limited.
What is the downside to using Terraform?
One potential downside to using Terraform is that it can be complex to learn and use, especially for those new to infrastructure as code. Additionally, Terraform’s state management can be difficult in large-scale deployments.
Why is Terraform so popular?
Terraform’s popularity is due to its ability to manage infrastructure as code across multiple cloud providers.
Its provider ecosystem, which allows you to manage resources across AWS, Azure, and Google Cloud, is a major selling point.
Should I use Terraform and Ansible together?
Yes, you can use Terraform and Ansible together. Terraform can provision infrastructure, while Ansible can configure and manage the software running on that infrastructure.
Why use Terraform instead of AWS?
Terraform can manage infrastructure across multiple cloud providers, while AWS CloudFormation is limited to managing AWS resources.
Additionally, Terraform’s provider ecosystem allows you to manage resources across multiple cloud providers, while AWS CloudFormation only supports AWS resources.
Can you replace Ansible with Terraform?
Terraform and Ansible serve different purposes, so it’s not a matter of replacing one with the other. Terraform can manage infrastructure, while Ansible can configure and manage software running on that infrastructure.
What is the downside of Ansible?
One potential downside of Ansible is that it can be resource-intensive, especially when running playbooks across large numbers of nodes. Additionally, Ansible’s dependency on SSH can be a security concern for some organizations.
Should I learn Kubernetes or Terraform first?
It depends on your specific needs and uses case. If you’re looking to manage infrastructure and cloud resources, Terraform might be the better choice.
If you’re looking to manage containerized applications and orchestrate them at scale, Kubernetes might be the better choice.
Is Kubernetes like Ansible?
Kubernetes and Ansible serve different purposes. Kubernetes is a container orchestration platform, while Ansible is a configuration management tool. While both tools can be used together, they are not interchangeable.
Why is Terraform used in DevOps?
Terraform is used in DevOps because it provides a way to manage infrastructure as code, making it easier to version control and automate infrastructure deployments.
This helps teams to work more efficiently and reduces the potential for human error when deploying infrastructure changes.
Is Ansible the same as Docker?
Ansible and Docker are not the same. Ansible is a configuration management tool that can be used to manage software running on the infrastructure.
At the same time, Docker is a containerization platform that allows you to package and deploy applications portly.
Should I learn Ansible?
Yes, Ansible is still a widely used and popular configuration management tool in the DevOps ecosystem. Learning Ansible can help you to automate configuration management tasks and manage software deployments at scale.
Why use Terraform for Kubernetes?
Terraform can be used to provision and manage the underlying infrastructure that supports Kubernetes, such as networking, storage, and compute resources. This makes it easier to deploy and manage Kubernetes clusters at scale.
Is Ansible still relevant?
Yes, Ansible is still a relevant and widely used configuration management tool in the DevOps ecosystem. It provides a powerful and flexible way to automate configuration management tasks and manage software deployments.
Why use Terraform instead of Docker?
Terraform and Docker serve different purposes. Terraform is used to manage infrastructure as code, while Docker is used for packaging and deploying applications in a portable way. While both tools can be used together, they are not interchangeable.
Is Terraform stateful or stateless?
Terraform is stateful. It maintains a state file that keeps track of the resources it has provisioned and their current state. This allows Terraform to manage infrastructure changes safely and predictably.
Do data engineers use Terraform?
Data engineers can use Terraform to provision and manage the infrastructure supporting their data pipelines and analytics workloads.
Which language is used in Terraform?
Terraform uses its domain-specific language (DSL) called HashiCorp Configuration Language (HCL).
What language is Terraform based on?
Terraform is not based on any other programming language, but JSON and YAML influence its syntax.
In which language is Terraform code written?
Terraform code is written in HCL.
Does Terraform use YAML or JSON?
Terraform uses HashiCorp Configuration Language (HCL), which has its syntax and is not based on YAML or JSON.
What is the replacement for Ansible?
There is no one-to-one replacement for Ansible, as it provides a unique set of capabilities for configuration management. Other tools in the same space include Chef, Puppet, and SaltStack.
Why use Terraform over Azure?
Terraform can manage infrastructure across multiple cloud providers, while Azure Resource Manager is limited to managing resources on Azure.
Terraform’s provider ecosystem also allows you to manage resources across multiple cloud providers, while Azure Resource Manager only supports Azure resources.
Is it worth learning Terraform?
Learning Terraform is worth it if you want to manage infrastructure as code and automate infrastructure deployments. Terraform is a widely used and popular tool in the DevOps ecosystem.
Why is Terraform better than other tools?
Terraform is better than other tools in some contexts but not all. Its strength lies in its ability to manage infrastructure as code across multiple cloud providers and its large provider ecosystem. Other tools may be better suited for specific use cases.
Which is better, Google Cloud deployment or Terraform?
Google Cloud deploy and Terraform serves different purposes. Google Cloud deployment focuses on deploying and managing Google Cloud resources, while Terraform can manage infrastructure across multiple cloud providers. Which tool is better depends on your specific needs and use case.
Can Kubernetes replace Terraform?
Kubernetes and Terraform serve different purposes. Kubernetes is a container orchestration platform, while Terraform manages infrastructure as code. While both tools can be used together, they are not interchangeable.
Can Jenkins replace Ansible?
Jenkins and Ansible serve different purposes. Jenkins is a continuous integration and continuous delivery (CI/CD) tool, while Ansible is a configuration management tool. While both tools can be used together, they are not interchangeable.
What is Terraform vs Jenkins?
Terraform is an infrastructure as code tool used to manage infrastructure, while Jenkins is a CI/CD tool used to automate software builds and deployments.
Is Ansible no longer free?
Ansible is still a free and open-source configuration management tool. There is also a paid version, Ansible Tower, which provides additional features and support.
Should I run Ansible as root?
It is generally not recommended to run Ansible as root, as it can be a security risk. Instead, it is recommended to use a dedicated user account with limited privileges.
Does Microsoft use Ansible?
Yes, Microsoft uses Ansible internally for configuration management and automation.
How many days will it take to learn Terraform?
The time it takes to learn Terraform depends on your existing knowledge and experience with infrastructure and cloud technologies. Dedication and practice make it possible to become proficient in Terraform within a few weeks to a few months.
Is Terraform tough to learn?
Terraform can be challenging to learn, especially for those new to infrastructure as code. However, many resources, such as documentation, tutorials, and online courses, are available to help you get started.
Do cloud engineers use Terraform?
Cloud engineers often use Terraform to manage cloud resources and infrastructure as code.
What will replace Kubernetes?
It is difficult to predict what will replace Kubernetes as it dominates the container orchestration market.
However, there are emerging technologies, such as Istio and Knative, that may have a role to play in the future of container orchestration.
Do companies still use Ansible?
Yes, many companies still use Ansible for configuration management and automation tasks.
Does Ansible use YAML or Python?
Ansible uses YAML for its playbooks and Python for its modules.
What are the 2 main components of Terraform?
The two main components of Terraform are the configuration files, which define the desired state of infrastructure, and the state file, which keeps track of the current state of infrastructure.
Does AWS use Terraform?
AWS does not officially endorse or recommend any specific tool for managing AWS resources, but Terraform has a strong provider ecosystem that allows you to manage AWS resources.
Can we write Terraform in YAML?
No, Terraform uses its domain-specific language called HashiCorp Configuration Language (HCL), which has its syntax.
Does Ansible use SSH or API?
Ansible uses both SSH and API to manage and configure remote systems. SSH is used for initial setup and configuration, while API is used for ongoing management and configuration tasks.
What is Ansible vs Jenkins?
Ansible is a configuration management tool used to automate the deployment and configuration of software, while Jenkins is a CI/CD tool used to automate software builds and deployments.
Is Ansible used for CI or CD?
Ansible can be used for both CI and CD. It can be used to automate the deployment and configuration of software as part of a CI/CD pipeline.
Terraform vs Ansible: Final Verdict
Terraform and Ansible share many similarities and differences. Code and infrastructure are deployed using both tools in environments with complex requirements that are repeatable over time.
So, for Orchestral, go for Terraform, and for Configuration management, go for Ansible.
Even though the complexity of data centers is increasing daily, each tool has a place in the development process. Both have limitations, however, and you should be aware of them before implementing them in your workforce.
Hopefully, you can find the winner in this battle, Terraform vs Ansible.


























