Xagt.exe or FireEye EndPoint Agent is the process used by the FireEye Endpoint Security to Protect your PC against any zero-day vulnerabilities, Scanning malware in your PC, Protecting Your PC or server against any Exploits along with it’s also scanning Real-Time indicators presence based on the threat feed that they are receiving from their Threat Intelligence feeds.
I will recommend you watch out the below-mentioned video to understand the FireEye Endpoint point security.
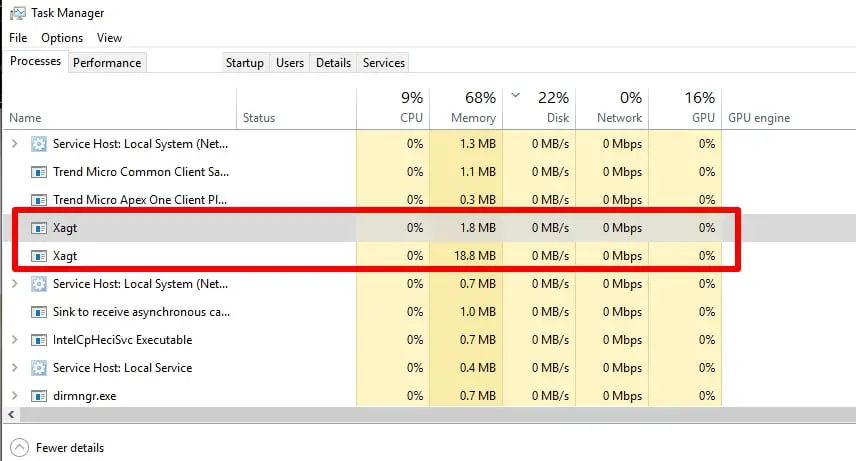
If you open your PC task manager you will find the Xagt process like below screenshot that is running in the Process.
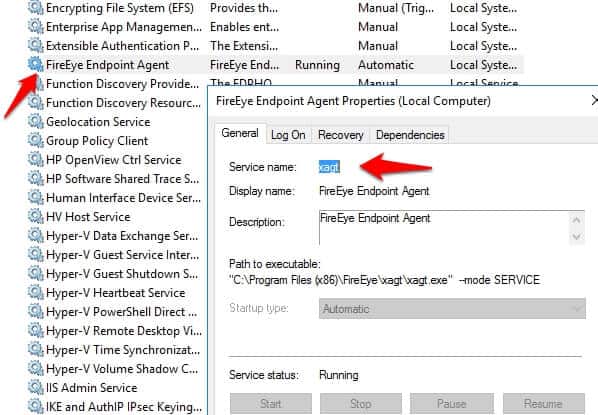
or you might be seeing “FireEye Endpoint Agent” Services but the main services name is Xagt only.
Xagt.exe: How To Disable It
First thing I want to clear you, this program is really required in your PC to protect your pc against any new zero-day vulnerabilities and malware. Only disable it once it’s really required.
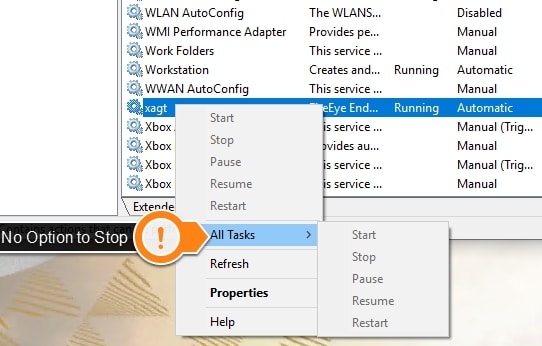
If you go to Services in the manager and right-click on the Xagt process, you have no option to disable it. 🙄
No worry, it’s FireEye they will not allow you to disable their agent easily and the main reason behind this security is to protect the agent itself against any malicious activity.
Follow the Below steps to disable it.
Step1:- Click on the Start button and search for cmd and right-click on it and select the option Run as Administrator,
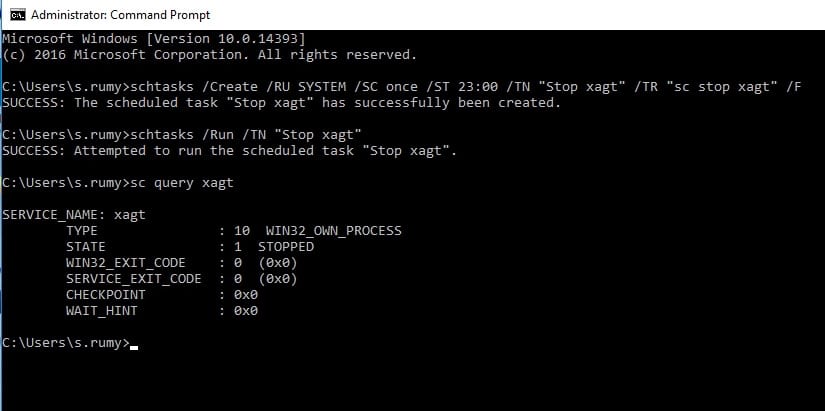
Enter the Below command to Create a Task:-
schtasks /Create /RU SYSTEM /SC once /ST 23:00 /TN “Stop xagt” /TR “sc stop xagt” /F
Which will give you out of “SUCCESS: The scheduled task “Stop xagt” has successfully been created.” out
Step2:- Now you need to Run Task with below command.
schtasks /Run /TN “Stop xagt”
it will give you “SUCCESS: Attempted to run the scheduled task “Stop xagt”” output
Which will stop the Xagt process in your PC. 😍
Step3:- Now you can easily Verify if the agent is stopped with the below command.
sc query xagt
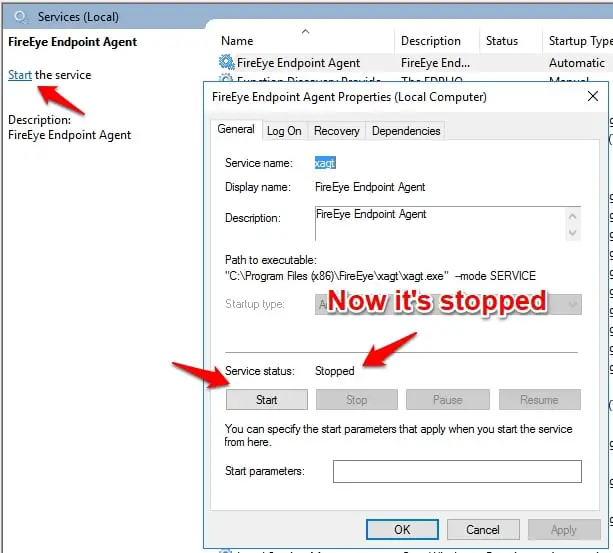
Now If you again go back to the Services you will find the Xagt Services is stopped like the below-mentioned screenshot. Now here you have the option to enable it also.
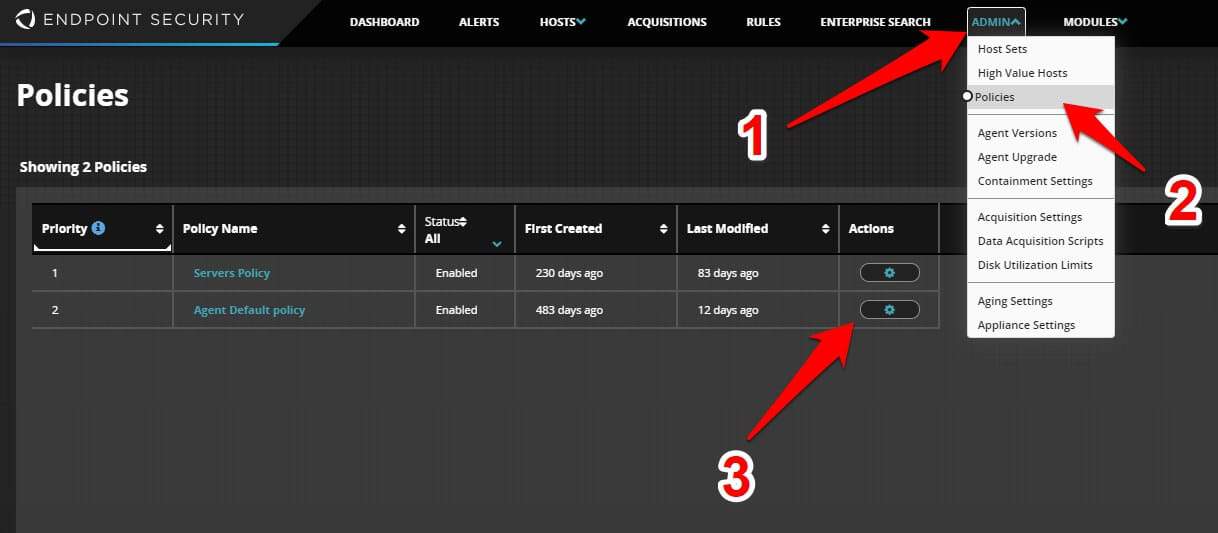
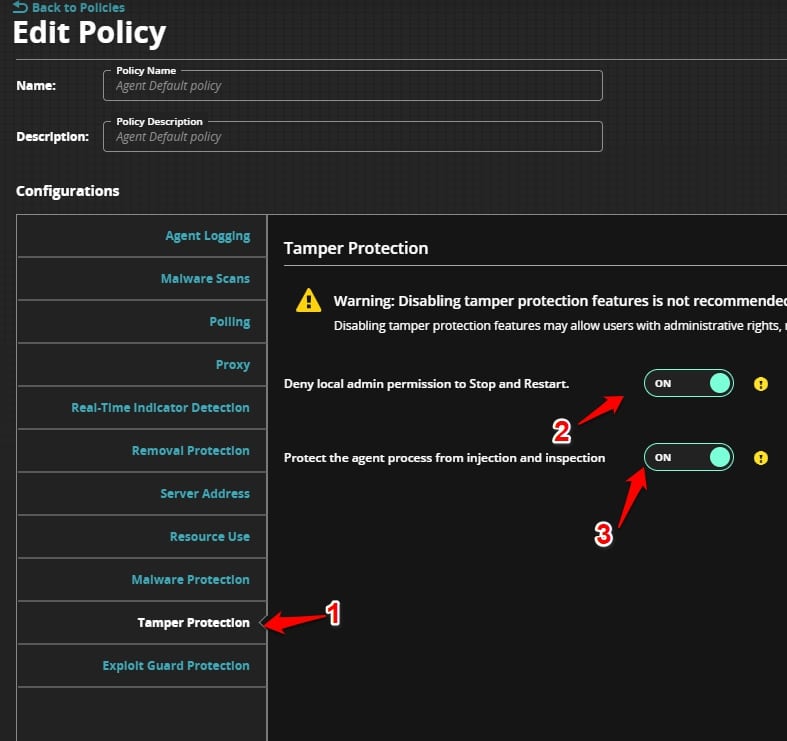
By default, Tamper protection is enabled to protect the Xagt client but if you are a FireEye HX admin, you are able to disable in the Policy.
Open the FireEye HX admin dashboard and navigate to the Admin > Policies and click on the policy and edit the policy that is applied on the host sets.
Here you have option to Disable Temper Protection.
Note:- Disabling tamper protection features may allow users with administrative rights, malicious actors, and/or malware to disable or weaken endpoint protection.
Xagt.exe: How To Uninstall
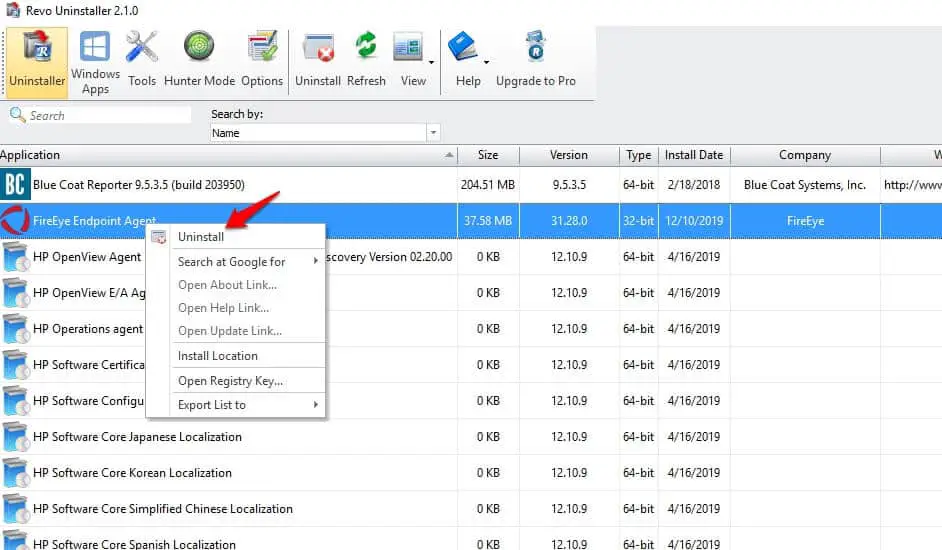
I faced one issue with the FireEye endpoint agent where it was installed on the PC and it was not communicating with the manager and it was password protected and i was not able to remove it.
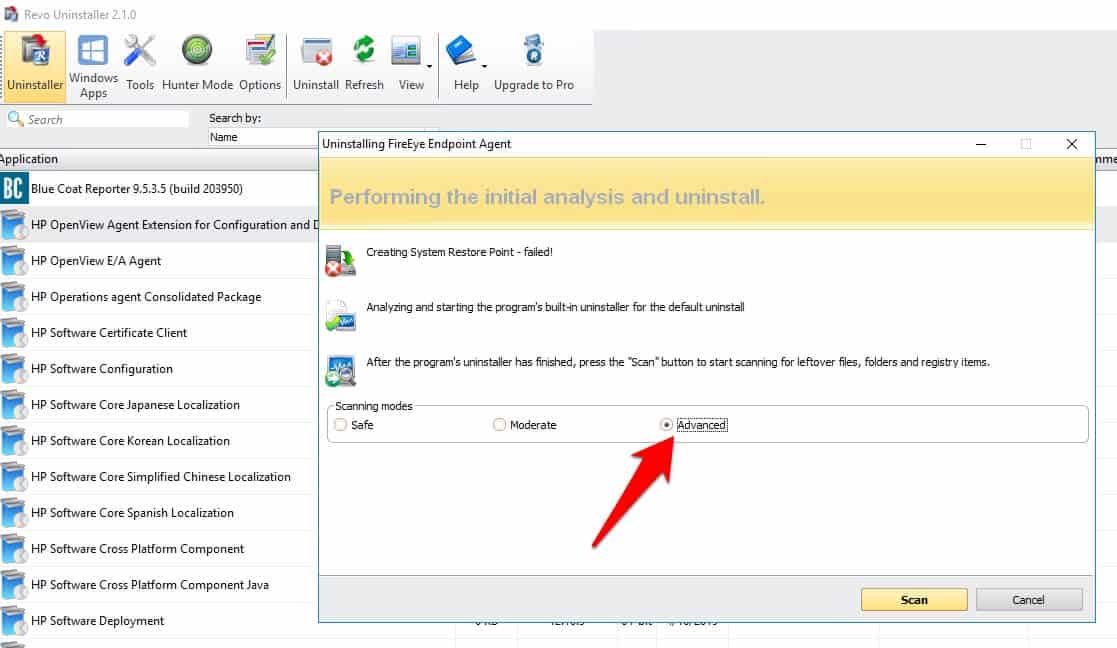
So Here is the Way to Uninstall it, Firest navigates to the https://www.revouninstaller.com/ and download and install the Revo Installer ( Select the Free One) on the PC.
Right-Click on the “FireEye EndPoint Agent” and select the Uninstall option.
it will start the uninstallation of the client but here you need to select the “Advanced‘ option and click on the Scan Optio to scan it.
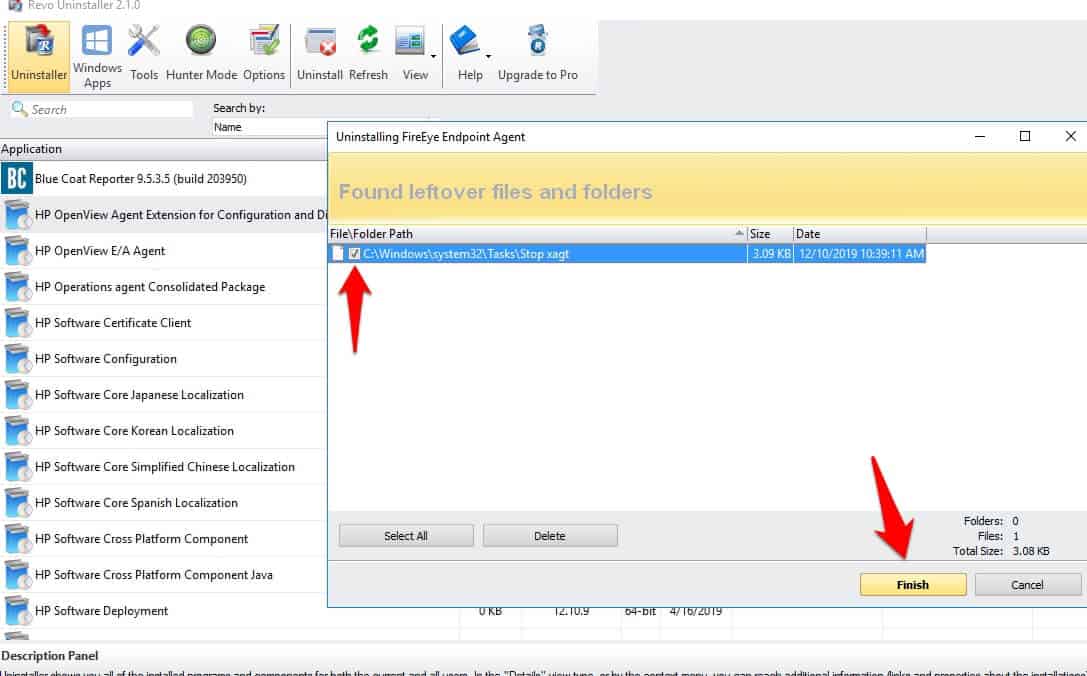
it will show you all the leftover of the program, click on the ‘Select All” option and click on the “Delete” option to delete that leftover. That’ it. 😎
if still it’s not removed then
Open/Run this Microsoft Tool ( Download here ) to verify and make sure no remnants of FireEye agent is present. If present, please remove it.
How To Check The Running Xagt Process?
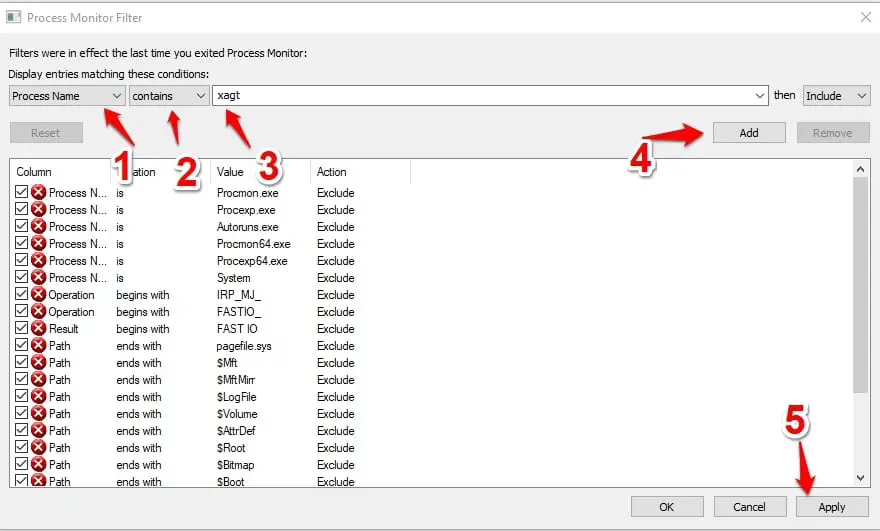
If you want to know How many Process is used by the Xagt then download the Process Monitor on your PC and run it with admin rights.
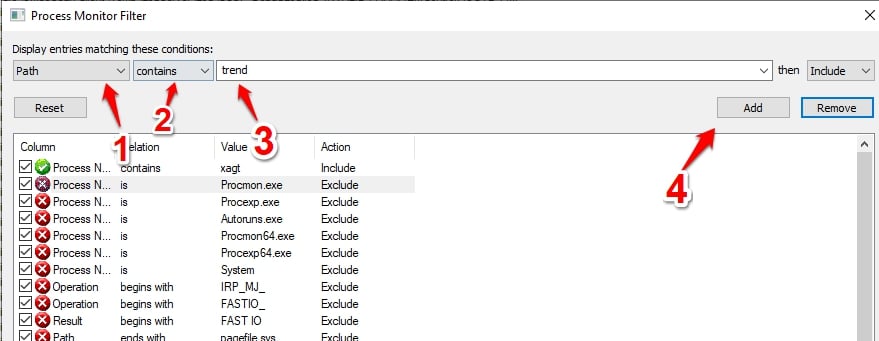
Follow the below screenshot where you need to select Process Name Contains Xagt option and click on the Add after that.
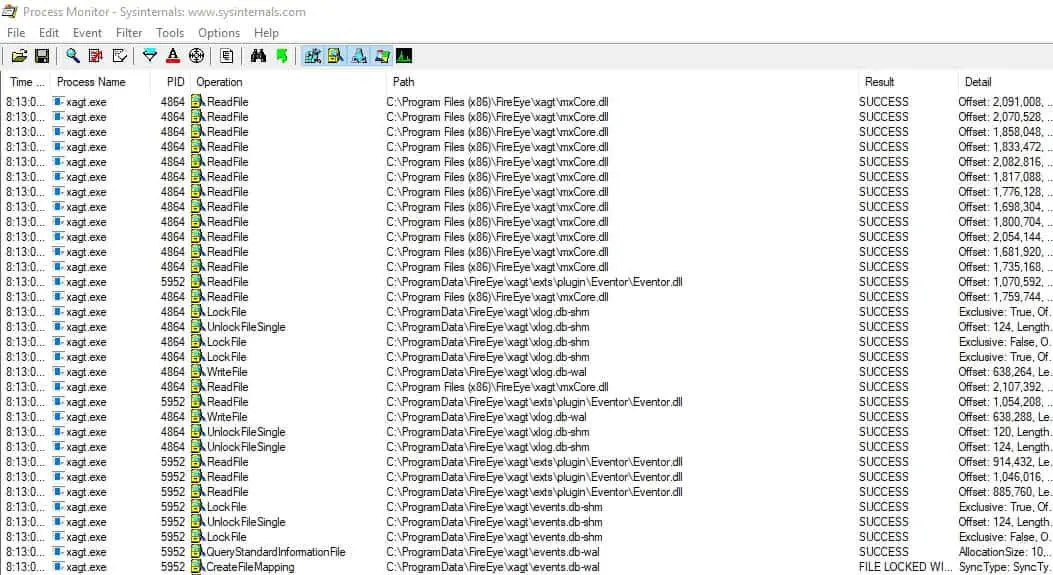
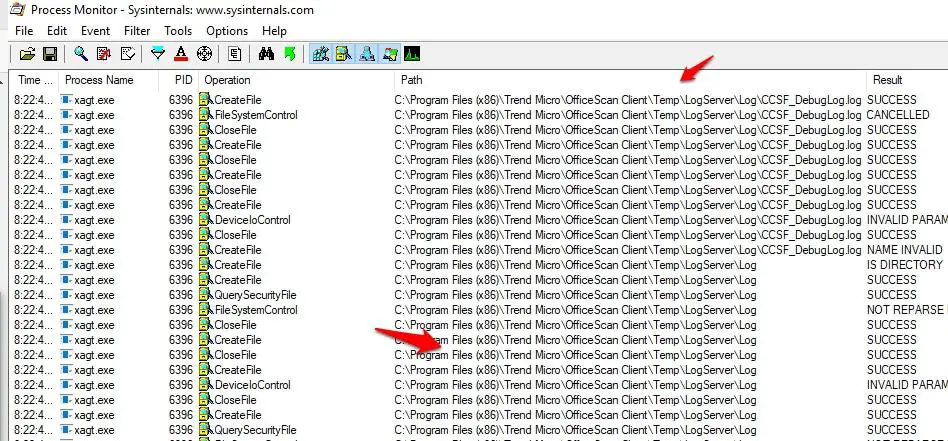
it will show you all the path that xagt is scanning
in case you are suspecting xagt is scanning another antivirus then in the same window you need to select Path contains your antivirus name, like in my case it’s TrendMicro.
Click on the Add to add in the scanning.
it will show you the exact path that FireEye is scanning.
How Much Memory Xagt Process is Consuming?
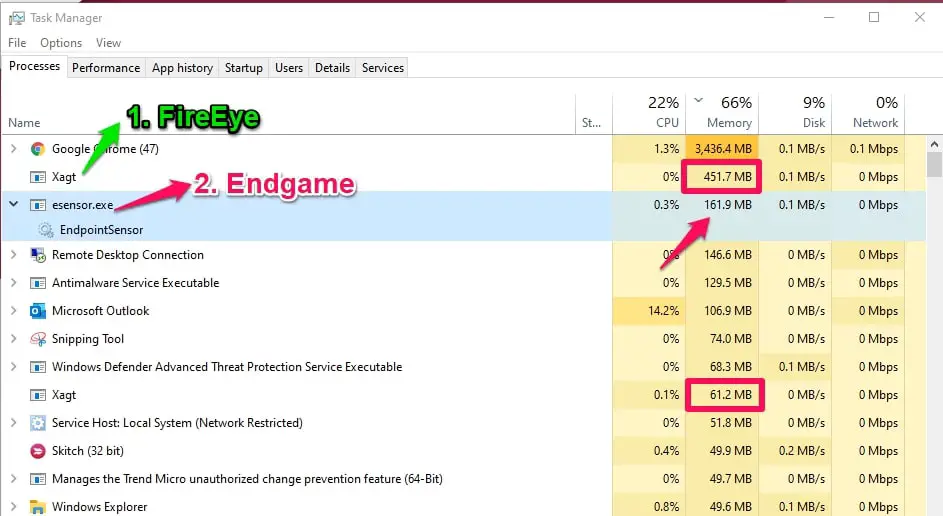
In my laptop, three EDR software (FireEye, Endgame, and Trendmicro EDR) are installed and I observed Xagt is average consuming memory between 400 to 600 MB.
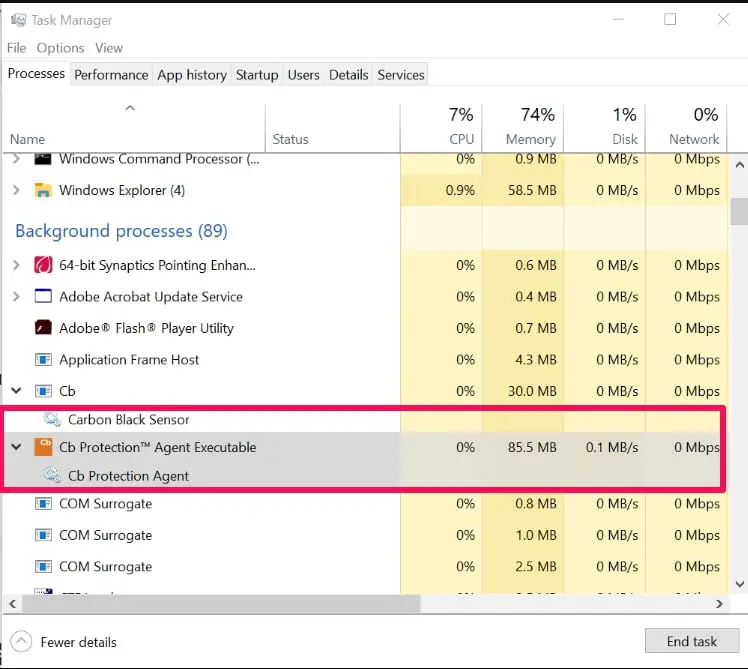
Look at the below screenshot of my Taskmanager, Fireye is running two processes and consuming an average 500 MB RAM and Endgame EDR is consuming 161 MB RAM.
Note:- All the module of FireEye is enabled in my PC,
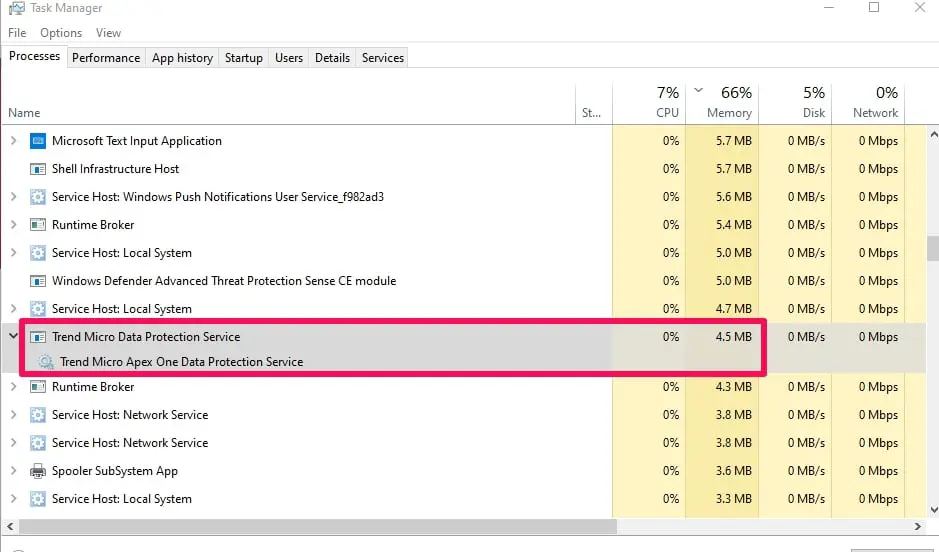
Trendmicro is consuming less memory than any other EDR.
In TrendMicro, Application control, Behavior Monitoring, DLP, Endpoint Sensor, Predictive Machine learning, and smart scan feature is enabled by it’s consuming less memory than any other EDR installed in my PC.
Note:- We are not comparing which EDR is Best here, I am just explaining to you which three top EDR is consuming how much RAM in normal operations.
I know you are missing Carbon black in this memory consumption, here is the carbon black consumption.
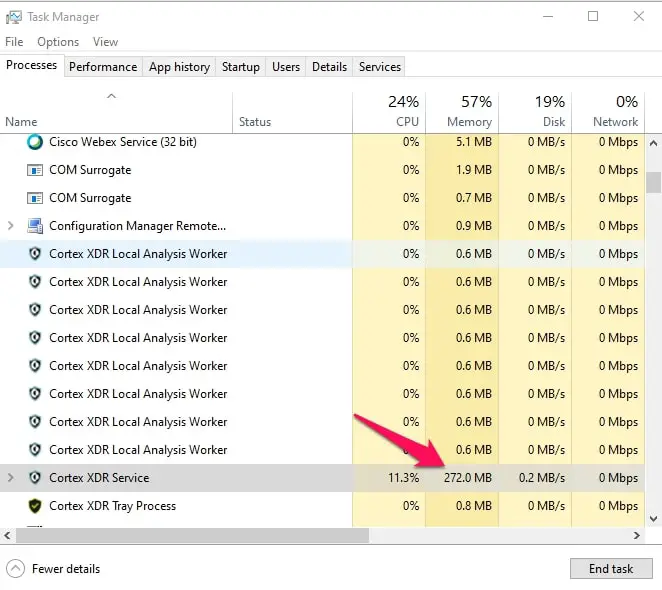
if you are missing Paloalto cortex XDR in this list then don’t worry we also added cortex memory consumption from the same pc.
it’s consuming memory between 160 MB to 275MB.
📗FAQ
What is Xagt used for?
Xagt is a FireEye Endpoint Security product component responsible for monitoring system events, processes, and files.
It is a lightweight agent that runs in the background and does not require user interaction. Xagt works alongside other FireEye Endpoint Security components to provide advanced threat detection and response capabilities.
What is Xagt on my computer?
Xagt is a FireEye Endpoint Security component installed on your computer as part of the FireEye Endpoint Security software package.
It is a lightweight agent that runs in the background and monitors system events, processes, and files for any signs of a suspicious activity or malicious behavior.
What is the FireEye agent used for?
FireEye agent, or FireEye Endpoint Security, is a software solution that provides advanced threat detection and response capabilities.
The agent is designed to protect endpoint devices like laptops and desktops from various advanced cyber threats, including malware, ransomware, and zero-day exploits.
How do I disable FireEye endpoint agent?
To disable the FireEye Endpoint Security agent, you must have administrative privileges on your computer.
You can then open the FireEye Endpoint Security console, navigate to the “Policies” tab, and create a new policy that disables the agent. Alternatively, you can uninstall the software from your computer using Windows’s “Add or Remove Programs” feature.
Is FireEye an IPS or IDS?
FireEye is neither an IPS (Intrusion Prevention System) nor an IDS (Intrusion Detection System). It is a software solution that provides advanced threat detection and response capabilities.
FireEye combines signature-based detection, behavior-based detection, and machine learning to detect and respond to cyber threats.
What type of tool is FireEye?
FireEye is a cybersecurity tool that provides advanced threat detection and response capabilities.
It is designed to protect endpoint devices like laptops and desktops from various advanced cyber threats, including malware, ransomware, and zero-day exploits.
How do I know if FireEye is installed?
To check if FireEye is installed on your computer, look for the FireEye Endpoint Security icon in your system tray, open the Windows “Add or Remove Programs” feature, and look for the FireEye Endpoint Security software.
You can also check with your IT department or security team to confirm if FireEye is installed on your computer.
What is FireEye malware protection?
FireEye malware protection is a feature of the FireEye Endpoint Security product that provides advanced protection against malware, ransomware, and other cyber threats.
FireEye combines signature-based detection, behavior-based detection, and machine learning to detect and respond to cyber threats.
What companies use FireEye?
FireEye is used by various companies across multiple industries, including financial services, healthcare, government, and technology. Some notable companies that use FireEye include Sony, Target, and JP Morgan Chase.
Is FireEye a SIEM tool?
FireEye is not a SIEM (Security Information and Event Management) tool. It is a software solution that provides advanced threat detection and response capabilities and can work alongside SIEM tools to provide comprehensive security for an organization’s endpoint devices.
Is FireEye antivirus software?
FireEye is not antivirus software in the traditional sense. While it does protect against malware, ransomware, and other types of cyber threats, it uses a combination of signature-based detection, behavior-based detection, and machine learning to detect and respond to threats rather than relying solely on virus signatures.
Is FireEye Endpoint Security good?
FireEye Endpoint Security is a highly regarded cybersecurity tool with advanced threat detection and response capabilities.
It is designed to protect endpoint devices like laptops and desktops from various advanced cyber threats, including malware, ransomware, and zero-day exploits.
The product has received positive reviews from security professionals and is considered a leading endpoint security solution in the industry.
How does FireEye Endpoint Security work?
FireEye Endpoint Security monitors system events, processes, and files on endpoint devices for any signs of a suspicious activity or malicious behavior.
The software uses a combination of signature-based detection, behavior-based detection, and machine learning to detect and respond to cyber threats in real time.
When a threat is detected, FireEye Endpoint Security can automatically quarantine the affected endpoint device and provide detailed threat intelligence to help security teams respond quickly and effectively.
Conclusion
Xagt or FireEye Endpoint Agent is a legitimate process running on your PC, which your Security team implements to protect your PC against any zero-day vulnerabilities and exploits. If it’s not required, don’t disable it or uninstall it.