In the most literal sense of the word, the cryptic code TLS stands for Transport Layer Security. The standard describes how the encryption of web connections should proceed, for example, using HTTPS.
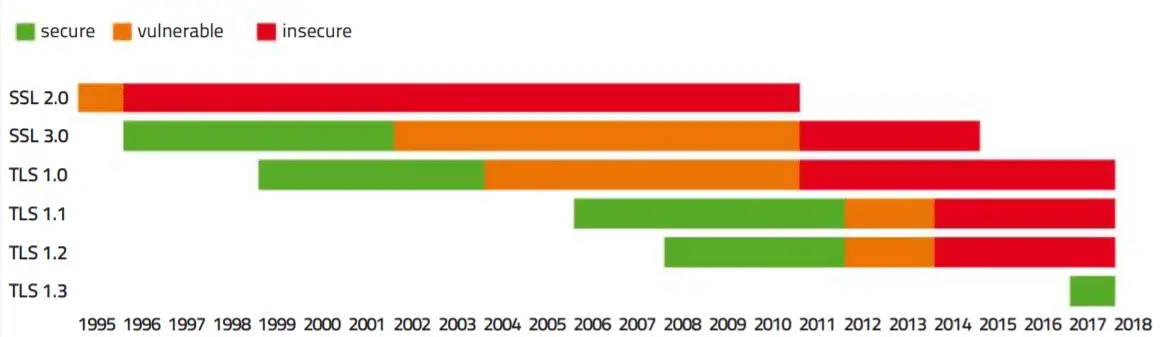
Search queries, email access, online shopping, money transfers via PayPal are secured equally, but it may not be the case with the more accessible, current version of 1.2, which has been under fire for the last few years. Even worse is the fact that many web servers offer older versions of long outdated SSL 3.0
Attacks on web encryption require a lot of resources and technical know-how. Since Snowden, we know that both of these are available in abundance for intelligence services like the NSA.
In the center of these attacks is always the man-in-the-middle, i.e. someone who can listen, capture and manipulate the encrypted packages of the connection.
Actually, web encryptions should withstand these tricks but TLS is plagued by its many insecure legacy systems, which were only eliminated in version 1.3.
Connect securely faster
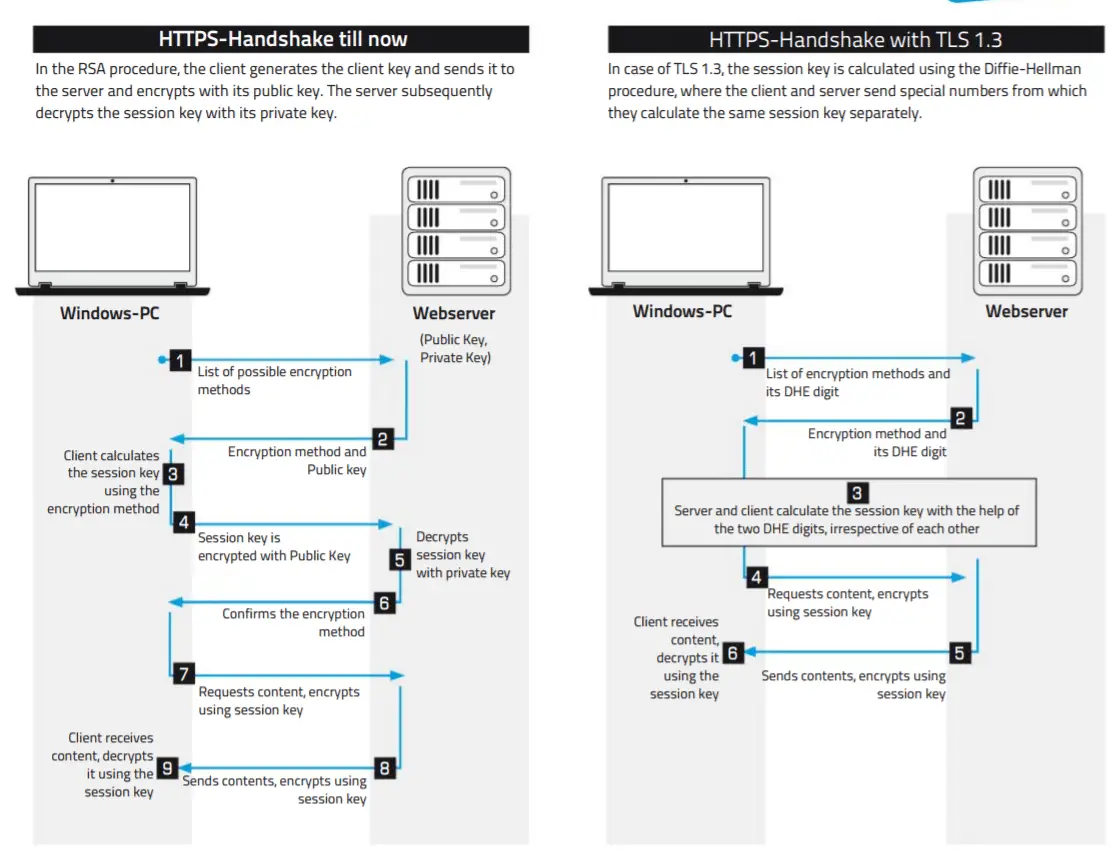
TLS 1.3 speeds up the setup of the encrypted connection as it saves a round trip (from the browser to the server and back). The browser is already sending all information for calculating the session keys for the server (see right) during the contact.
And as soon as the server transmits its DHE number, the browser can also start the calculation. The information about the encryption method is skipped since only a handful of permitted methods remain as a result of the cleanup.
The browser can then assume that the server will control the proposed encryption.
If browsers and servers were already connected, then TLS 1.3 also allows contact without a roundtrip.
This is done via a resume key which the browser receives during the first communication from the server. Subsequent contacts with the server are then started by the browser and encrypted using the resume key.
Apart from the query, it also includes a DHE digit with the second communication. Once that is received, the browser no longer requires the key, but will use a newly calculated session key for security reasons. Many users already have access to TLS
Many users already have access to TLS 1.3, courtesy of the latest versions of Firefox or Chrome, but have likely not activated it. If it’s for Firefox, this is done via ‘‘about:config” and in Chrome via ‘‘chrome://flags”. On the server.
On the server side, the implementation may last longer. But TLS 1.3 is just the first step in the right direction, as there are already plans in place to release the frequently used crypto library OpenSSL with the next version. With that, shopping, banking, and emails as well as surfing, in general, will become much safer.
Bug-free encryption
With the switchover to TLS 1.3, the web encryption basically gets renovated. The encrypted connection from the browser to the server can be achieved in a few steps
and uses another method to calculate the session key with the help of Diffie-Hellman.
It makes the handshake via the Internet more secure.
Web encryption with insecure history
In the course of time, every version of web encryption proves itself to be vulnerable and has been hacked. SSL 2.0 and 3.0 have been fully sorted out by the Internet Engineering Task Force.
Also, Check How the Blockchain Works
All You Need to Know about Next-Gen Virus Protection
Hope my article “An overview of Transport Layer Security (TLS) 1.3” helps you to understand TLS 1.3 in the best way.