Are you frustrated by encountering the dreaded “Request Header or Cookie Too Large” error message while browsing the web?💁
This perplexing error can disrupt your online experience and leave you wondering how to overcome it.
Fortunately, you’ve come to the right place. This article will delve into the causes behind this error and provide practical solutions to get your browsing back on track.
Whether you’re a website owner, a developer, or an internet user who wants to understand and fix this issue, we’ve got you covered.
By the end of this article, you’ll clearly understand why this error occurs and a toolbox of techniques to resolve it effectively.
So, let’s dive in and unravel the mysteries of the “Request Header or Cookie Too Large” error, empowering you to navigate the web seamlessly again. Ready to overcome this challenge?
Let’s get started!
Recently I faced one strange “Request Header Or Cookie Too Large” error while updating the post on my website.
Still, I found this error is nowhere related to my website because the website is working fine for others, and even it’s working fine on another browser.
This error mostly comes to you once you visit a site a lot, and Cache is stored in your browser, causing this error.
Step-by-Step Process to Fix Request Header Or Cookie Too Large Error
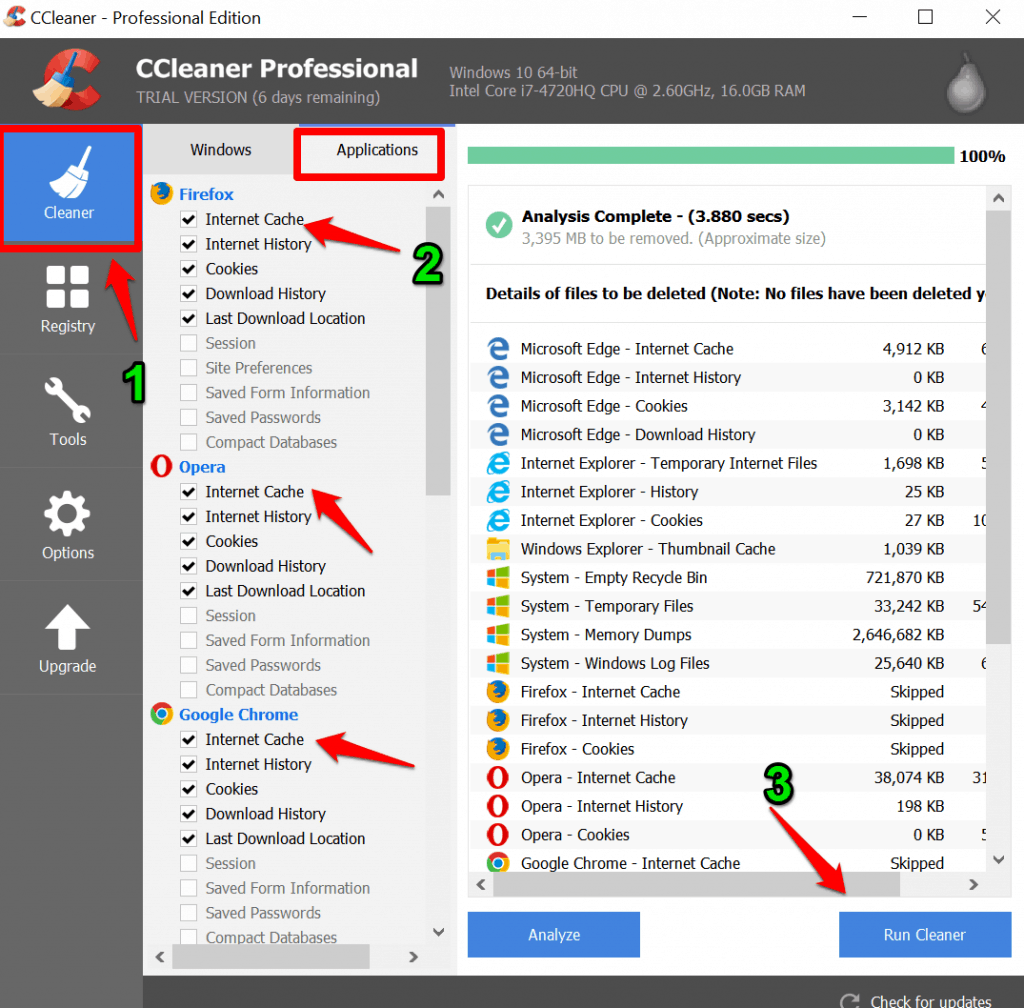
1. Personally, I loved to use Ccleaner to clear my PC browser cache or cookies to speed up my pc.
If you are using CCleaner, you can easily do it by selecting the Cleaner > Application tab and Select the particular browser that you are facing “Request Header Or Cookie Too Large” error and click on the Run cleaner option to clear your browser cache.
I will recommend you to read How To Fine Tune Your Windows 10 PC For Best Performance
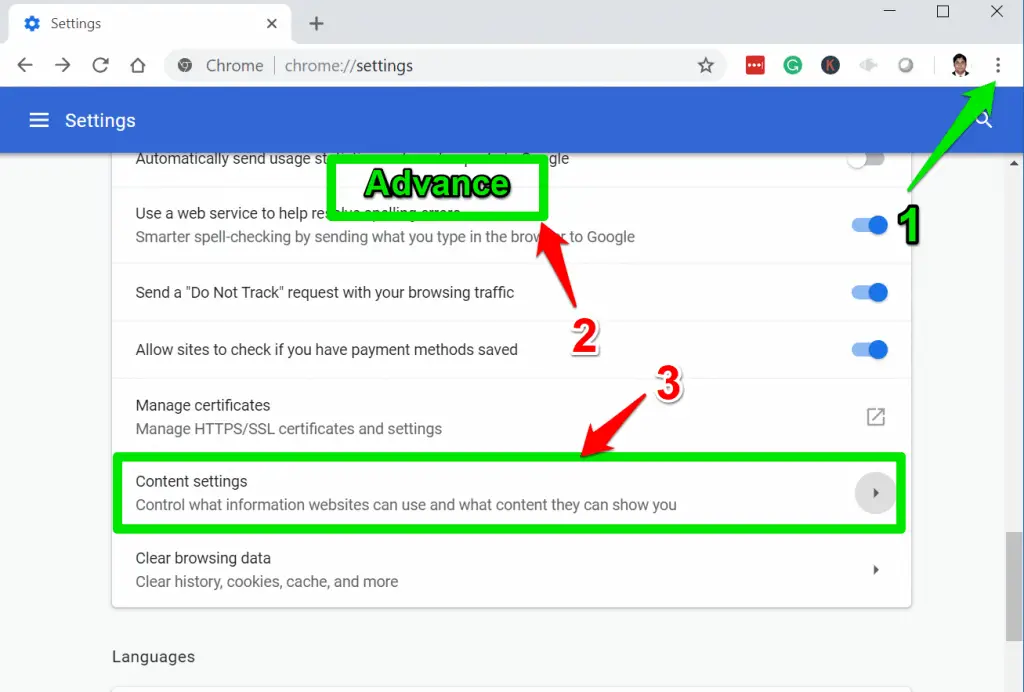
2. If you don’t want to use CCleaner you can clear the cache of a particular website in your browser also.
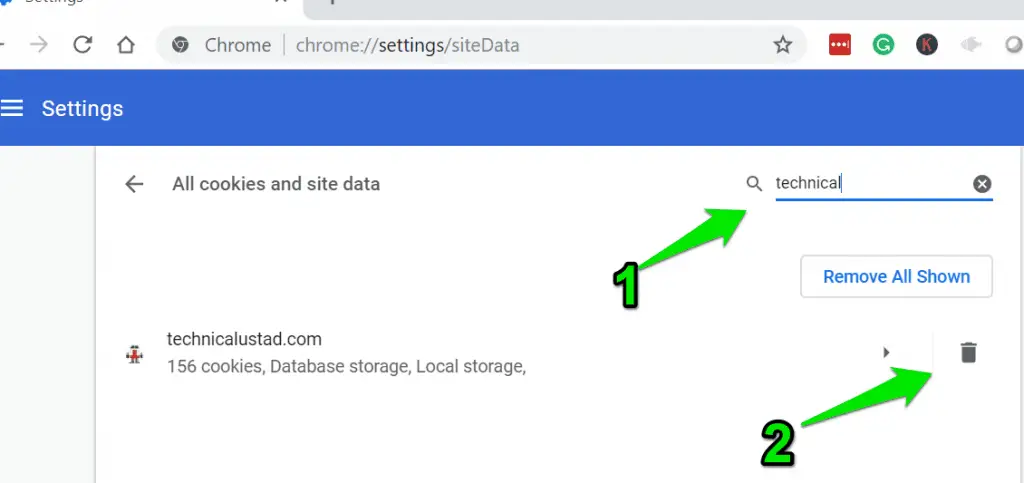
To Clear in Google Chrome, Navigate to Three-dot menu and select Settings and scroll down and click on the ” Advanced” option and select the ” Content Setting” option.
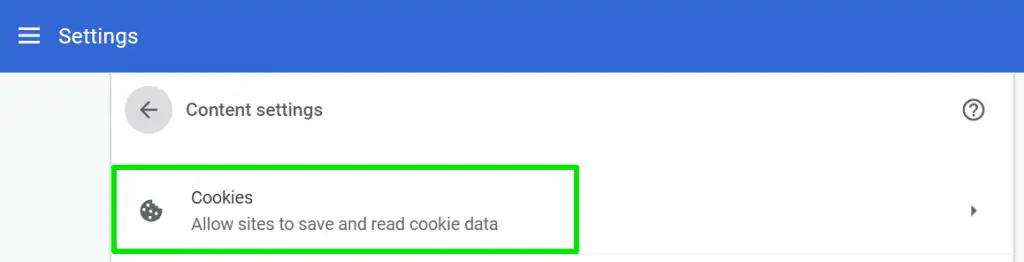
and select “Cookies” option where you will find information about allowed sites to save and read cookie data.
Click on the ” See all cookies and site data” and search for the particular website and click on the ” Delete” icon to delete a particlar cookie.
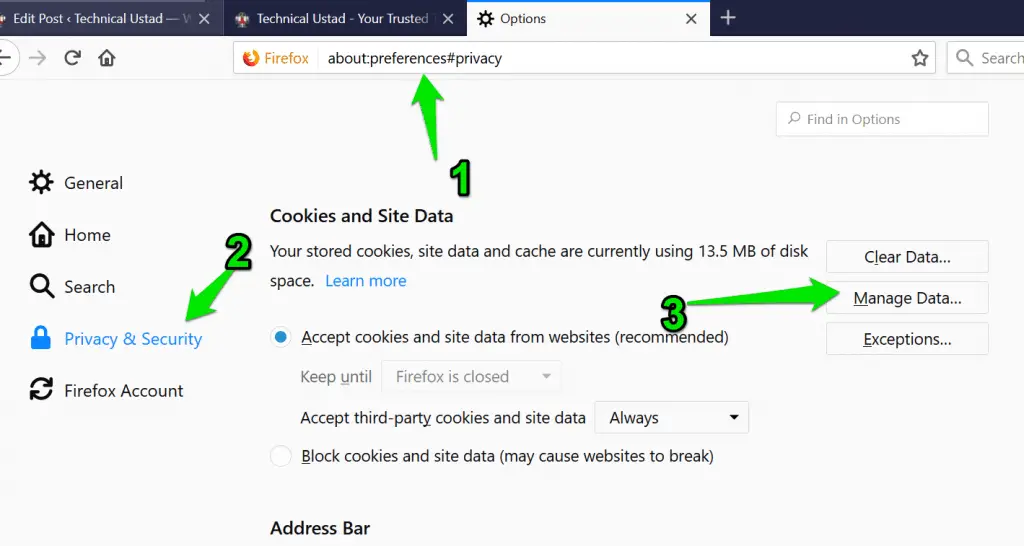
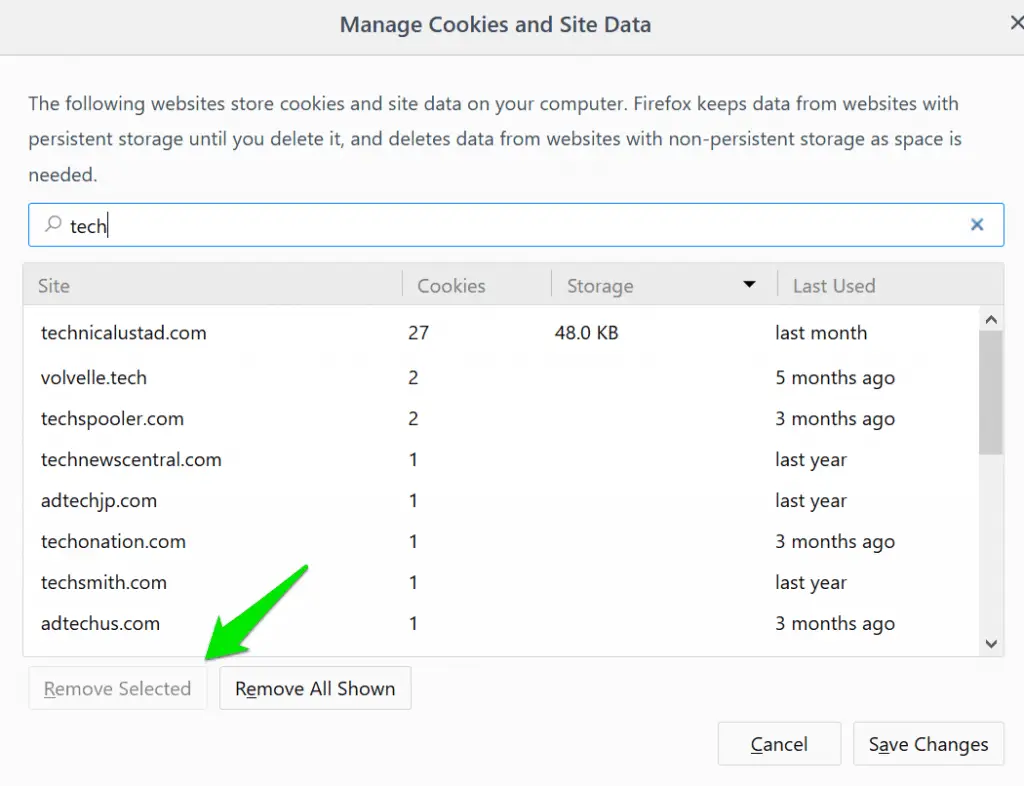
3. In Firefox, Enter about:preferences#privacy in the address bar and click on the ” Manage Data” option.
and Search for your particular website and Select the ” Remove selected” option.
Pro Tip:- Switch your browser to Brave Browser ( Download Here ) which is not storing your cookies or any personal data. I am using this from the last six months and trust me it’s the best browser that I ever used.
We have a Brave Vs Chrome: An In-Depth Comparison Guide For You, which will help you understand the differences between browsers.
The error message “Request Header or Cookie Too Large” in Nginx indicates that the request header or cookie size exceeds the defined limit.
When a client sends a request to an Nginx server, it includes important information in headers and cookies. However, if these data packets exceed the specified size threshold, Nginx rejects the request, triggering the aforementioned error.
Understanding this error is crucial for maintaining optimal server performance and ensuring a smooth browsing experience for users.
When encountering the “Request Header or Cookie Too Large” error, there are a few key steps you can take to address the issue:-
Review Nginx configuration:- Check the Nginx configuration file (nginx.conf) to determine the maximum allowable size for request headers and cookies. Look for the client_header_buffer_size and large_client_header_buffers directives, which control the size limits.
Adjust size limits:- If the default values are too restrictive for your application, you can modify these directives to increase the size limits. However, be cautious not to set them excessively high, as it may impact server performance or leave it vulnerable to potential attacks.
Optimize request headers and cookies:- Analyze the size of the request headers and cookies being sent. Identify any unnecessary or oversized data and optimize them accordingly. Techniques like compression and minification can help reduce the overall size.
Consider load balancers or proxies:- If you’re using them in conjunction with Nginx, they may also impose their own limits on request headers and cookies. Review their configurations and adjust the limits if necessary.
Encountering a 400 Bad Request Header or Cookie Too Large error in Nginx can leave you wondering about the underlying causes.
Let’s delve into the reasons behind this error and shed some light on the matter.
Oversized request headers:- One common cause is the inclusion of excessively large data in the request headers. When the size exceeds the predefined limit set by Nginx, the server rejects the request, resulting in the 400 error.
Excessive cookie size:- Another culprit could be the size of the cookies sent with the request. If the cookie data surpasses the permitted limit, Nginx interprets it as a bad request and returns the error.
Nginx configuration:- The server’s configuration can also contribute to this error. Nginx has certain parameters that define the maximum size allowed for request headers and cookies. If these values are set too low, even normal-sized headers or cookies can trigger the error.
Proxy or load balancer restrictions:- If you’re using a proxy or load balancer in front of Nginx, they may impose their own limitations on request sizes. Ensure that their configurations align with the intended request limits.
Encountering a Request Header or Cookie Too Large error in Safari can be frustrating, but worry not! There are several steps you can take to address this issue and ensure a seamless browsing experience.
Let’s explore the solutions:-
Clear browser cookies:- Start by clearing the cookies stored in Safari. Sometimes, accumulated cookies can exceed the maximum size limit, triggering the error. To clear cookies, go to Safari Preferences, select “Privacy,” and click on “Manage Website Data.” Remove all the stored cookies and restart Safari.
Update Safari:- Ensure you are using the latest version of Safari. Updates often include bug fixes and improvements, addressing known issues that could cause the error. To update Safari, go to the App Store, click on “Updates,” and install any available updates for Safari.
Disable extensions and plugins:- Third-party extensions and plugins can sometimes interfere with request headers or cookies, leading to the error. Temporarily disable all extensions and plugins in Safari to identify if any are causing the issue. Then, enable them one by one to pinpoint the problematic one and either update or remove it.
Reset Safari:- As a last resort, you can reset Safari to its default settings. This action clears cache, cookies, extensions, and other personalized data. To reset Safari, go to Safari Preferences, select “Privacy,” and click on “Manage Website Data.” Then, click on “Remove All” to reset Safari.
Encountering a “400 Bad Request: Request Header or Cookie Too Large” error can be frustrating, but fret not! I’m here to guide you through resolving this issue swiftly and effectively.
To begin, it’s important to understand that this error occurs when the size of the request header or cookie exceeds the server’s predefined limit. When this happens, the server rejects the request, resulting in the “400 Bad Request” error message.
So, how can you fix it? Let’s dive in.
Check request headers and cookies: Start by examining the request headers and cookies involved in the problematic request. Look for any excessively large data or unnecessary information. Trim down the content to reduce its size and ensure it fits within the server’s limits.
Optimize content: Compressing or minifying your website’s resources can significantly reduce their size. Employ tools like Gzip compression or minification plugins to shrink the content without compromising its functionality.
Adjust server configurations: Explore your server’s settings and configurations. Increase the maximum header size or cookie length to accommodate larger requests. However, be cautious not to set these limits too high, as it may leave your server vulnerable to attacks.
Consider load balancers and reverse proxies: If you’re using load balancers or reverse proxies, they might be the culprit.
Some configurations can limit the allowed header or cookie size. Adjust the settings accordingly or consult with your network administrator for assistance.
By diligently following these steps, you can tackle the “400 Bad Request: Request Header or Cookie Too Large” error head-on.
Remember, optimizing request headers and cookies, tweaking server configurations, and leveraging compression techniques are key to resolving this issue and ensuring a smooth browsing experience for your users.
📗FAQ’s
If you receive an error message that says “request header or cookie too large,” you can fix it by clearing your browser’s cache and cookies. If that doesn’t work, you can try using a different browser or adjusting your browser’s cookie settings.
When you see a 400 error with the message “request header or cookie too large,” it means that the server cannot process your request because the data you are sending is too large for the server to handle. This is often caused by an issue with your browser’s cookies or cache.
How do I get rid of 400 Bad Request?
To get rid of a 400 Bad Request error, you can try clearing your browser’s cache and cookies. If that doesn’t work, you can try using a different browser or adjusting your browser’s cookie settings.
If you are getting cookie errors that are too large, you can fix it by clearing your browser’s cache and cookies. If that doesn’t work, you can try adjusting your browser’s cookie settings or using a different browser.
To clear your browser’s cache and cookies, you can go to your browser settings and look for the option to clear browsing data. From there, you can select the time range and the type of data you want to clear, including cookies and cache.
How do I clear my Cookie request?
To clear a specific cookie request, you can go to your browser’s settings and look for the option to manage cookies. From there, you can select the specific cookie you want to remove and delete it.
How do I fix HTTP error 400 in Chrome?
To fix an HTTP error 400 in Chrome, you can try clearing your browser’s cache and cookies. If that doesn’t work, you can try disabling any extensions or plugins that may be causing the error.
To clear cookies on Chrome, you can go to your browser’s settings and look for the option to clear browsing data. From there, you can select the time range and the type of data you want to clear, including cookies.
What causes a 400 Bad Request error?
A 400 Bad Request error is often caused by an issue with the data you send to the server. This can include issues with your browser’s cookies, cache, or the format of the data you are sending.
What does 400 Bad Request mean in API?
In an API, a 400 Bad Request error means that the client’s request was invalid or could not be understood by the server. Issues with the request format can cause this, the data being sent, or the server’s configuration.
What is an example of bad request 400?
An example of a 400 Bad Request error could be a user trying to access a page on a website without proper authentication or sending invalid data to the server.
Cookies can become too big when they contain too much data, or when they are being used inefficiently by the website or application. This can cause issues with the server’s ability to handle the requests.
Your cookies may get big if the website or application is storing too much data in the cookie or if the cookie is being used inefficiently. This can cause issues with the server’s ability to handle the requests.
Deleting your cookies can help improve your privacy and security online, as well as clear any issues that may be causing errors in your browser. However, deleting your cookies may also block you from websites and erase any personalized settings or preferences.
Deleting cookies may also clear your browser’s cache, depending on the settings you choose when clearing your browsing data.
Deleting cookies and cache can help resolve issues with your browser and improve its performance. However, it may block you from websites and erase any personalized settings or preferences.
The commands to clear cookies depend on your browser and operating system. In most cases, you can go to your browser’s settings and look for the option to clear browsing data, which will include the option to clear cookies.
Deleting cookies may block you from websites and erase any saved login information, including passwords. However, some browsers allow you to save passwords separately from cookies, so deleting cookies may not always delete your saved passwords.
When you remove all cookies, you will be logged out of any websites you are currently logged into, and any personalized settings or preferences will be erased. You may also need to re-enter login information and other data the next time you visit those websites.
How do I fix HTTP error on Chrome?
To fix an HTTP error on Chrome, you can try clearing your browser’s cache and cookies, disabling any extensions or plugins, or updating your browser.
Why is Google giving me a 403 error?
A 403 error from Google typically means that you do not have permission to access the resource you are trying to view. This can be caused by issues with your account or settings, or by the website or application you are trying to access.
Deleting cookies can help speed up Chrome by clearing any data causing issues with your browser’s performance. However, it may also block you from websites and erase any personalized settings or preferences.
Deleting cookies may improve Chrome’s performance by clearing any data causing issues with your browser. However, other factors such as internet speed and computer performance, may also impact your browsing experience.
Chrome may clear cookies automatically if you have set it to do so, or if you have chosen to clear your browsing data at regular intervals.
How to fix 400 error in JavaScript?
To fix a 400 error in JavaScript, you can check your code for any syntax errors or issues with the data being sent to the server. You can also try clearing your browser’s cache and cookies or using a different browser.
What is error 400 validation error?
A 400 validation error typically means the data sent to the server does not meet the required format or criteria. This can be caused by issues with the code or the data being sent.
What is the HTTP status code for bad requests?
The HTTP status code for a bad request is 400.
What is the difference between 400 Bad Request and 401?
A 400 Bad Request error means that the server is unable to process the request due to issues with the data being sent, while a 401 error means that the request is unauthorized and requires authentication.
What is the difference between 400 Bad Request and 422?
A 400 Bad Request error means that the server is unable to process the request due to issues with the data being sent, while a 422 error means that the request is valid but the server is unable to process it due to semantic errors.
How do I fix a bad server request?
To fix a bad server request, you can review the error message and the request data to determine the specific issue. You may need to adjust the data being sent, update the code or configuration, or contact the server administrator for assistance.
What is the difference between 400 Bad Request and 500?
A 400 Bad Request error means that the server is unable to process the request due to issues with the data being sent, while a 500 error means that the server encountered an internal error and is unable to process the request.
Conclusion
In conclusion, understanding the error message “Request Header or Cookie Too Large” is essential for maintaining a seamless browsing experience on your website.
By grasping the root causes and implementing effective solutions, you can overcome this issue and ensure a smoother interaction between your website and its users.
Remember, when encountering this error, start by assessing the size of your request headers or cookies.
Check for any oversized data that could be causing the problem. It’s crucial to optimize the content and reduce the overall size to fit within the specified limits.
Additionally, reviewing server configurations and settings is paramount. Adjusting parameters such as the maximum header size or cookie length can help prevent this error from occurring in the future.
Furthermore, utilizing compression techniques, such as gzip compression, can significantly reduce the size of your request headers or cookies.
By compressing the data, you can enhance the performance of your website and avoid exceeding the allowable limits.
Lastly, remember to stay up to date with the latest best practices and guidelines provided by web standards and protocols.
This ensures that your website aligns with industry recommendations and avoids potential issues like the “Request Header or Cookie Too Large” error.
By implementing these strategies and maintaining a vigilant approach to managing request headers and cookies, you can provide a seamless browsing experience for your users while avoiding this common error.
Take proactive steps today to optimize your website’s performance and ensure a smooth user experience.