This article is for you if you’re a developer using Sandboxie and want to try different solutions or new software features. There are a lot of important factors to consider when you want to find a Sandboxie alternative for your needs.
We have listed eight alternatives here, including what they do, their features, and the pros and cons.
There are limitations to this software; not all work on different platforms and some are limited only to Linux or Windows, but a few work on different platforms. Some are free to use, while others need to be bought. Another factor is also if they are lightweight.
All these factors have been detailed in the article below and will be able to help you pinpoint the alternative that helps you best with your specific needs.
What is Sandboxie?
We will answer this question and how it changed over time before getting into its alternatives.
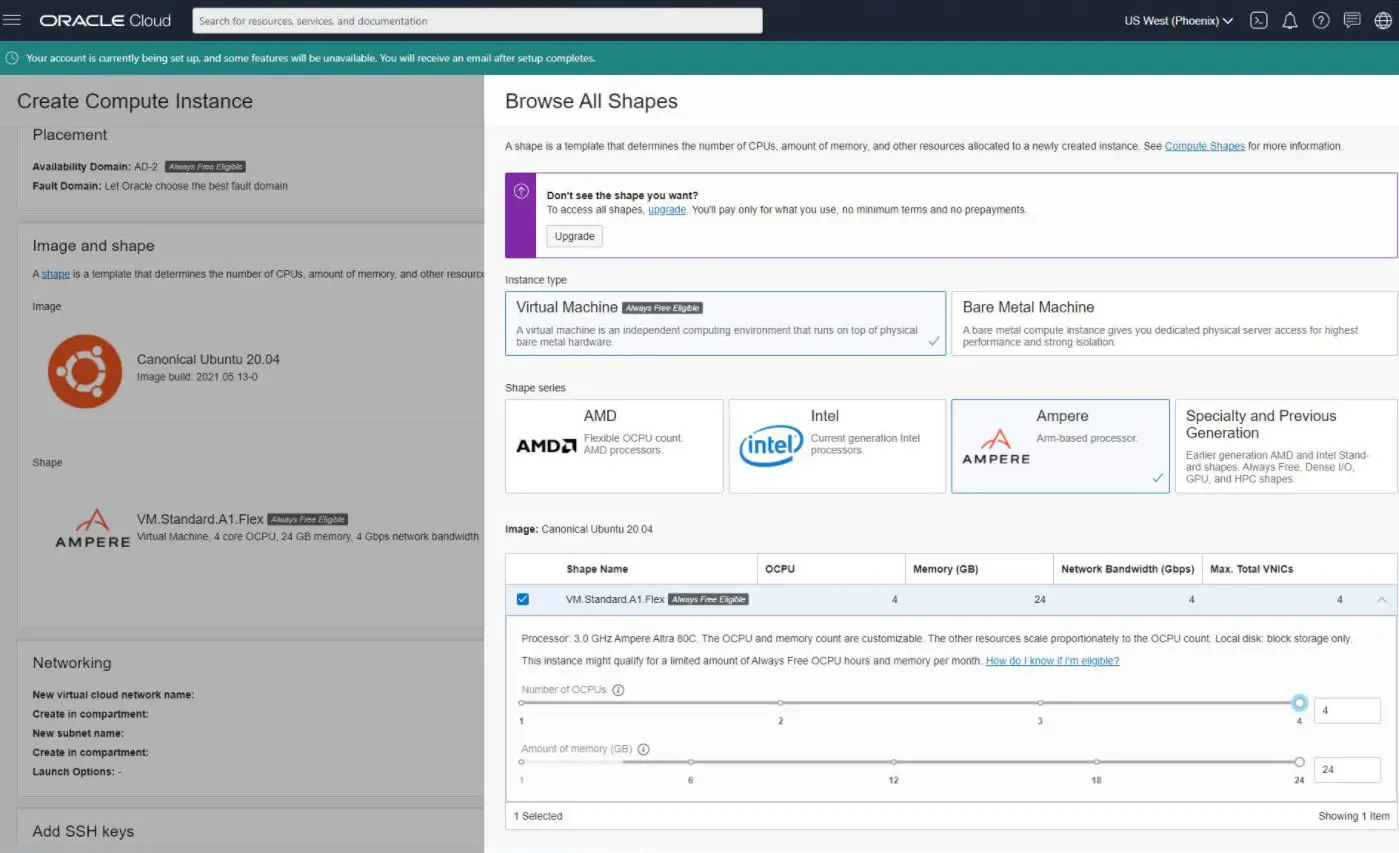
It is an open-source sandboxing program made for Microsoft Windows and what it does is that it creates an isolated operating environment where applications can be run or installed without them modifying the local system permanently.
This virtual environment is great for the controlled testing of untested programs and web surfing.
When it was released in 2004, it was initially a tool for sandboxing Internet Explorer, but over time, it was expanded to support arbitrary Win32 applications and other browsers.
In 2013, Invincea acquired Sandboxie, and the original developer stated he would no longer be involved with the program.
In 2017, Sophos acquired Invincea, but the development and support continued as normal. In 2019, the released Sandboxie version was done under a license with plans to transition the software to an open-source tool.
In April 2020, the source code under the GPL-3.0-or-later license was released by Sophos, and they said that they would not be involved in Sandboxie’s development but that the open-source community would have to take this on by themselves.
Best Sandboxie Alternatives – Our Top Pick👌
We have eight alternatives listed here, along with their features and pros and cons.
This way, you will find it easy to choose a Sandboxie alternative that is within your budget, works on the platforms you want, and is perfect for the specifications of your laptop or whatever else it is that you would use it on.
1. Docker Hub
Docket Hub is a great Sandboxie alternative and began in the year 2013. This was when they introduced something that would become the industry standard for containers.
These containers are standardized software units, allowing developers to isolate their apps from their environments so that it’s not limited to being worked on in only one place.
Millions of developers today use Docker to build containerized apps and share them; this works on the desktop and the cloud. The team at Docker works on building their unique connected experience from code to the cloud for all sorts of developers and also the various developer teams.
It is important to understand that app development needs more than just writing code today. You would need architectures, frameworks, multiple languages, and discontinuous interfaces between the tools for every lifecycle change, which results in enormous complexity.
Docker not only simplifies the workflow but also accelerates it and gives developers the freedom to innovate with the application stacks and tools of their choice. It can also choose deployment environments for every project they work on.
The CLI-based workflow is accessible to developers of various skill and expertise levels, making it great for beginners. You can install it from a single package and then get it up and running in minutes.
You can also code and test locally while also being able to ensure consistency between production and development.
Pros:-
- Works well for all OS
- Easy to set up and integrates well with most of the available CI/CD tools.
- There is a community forum that can help resolve any issues.
Cons:-
- Resource sharing can be a little complex.
- There are limitations to the security since there is no actual OS.
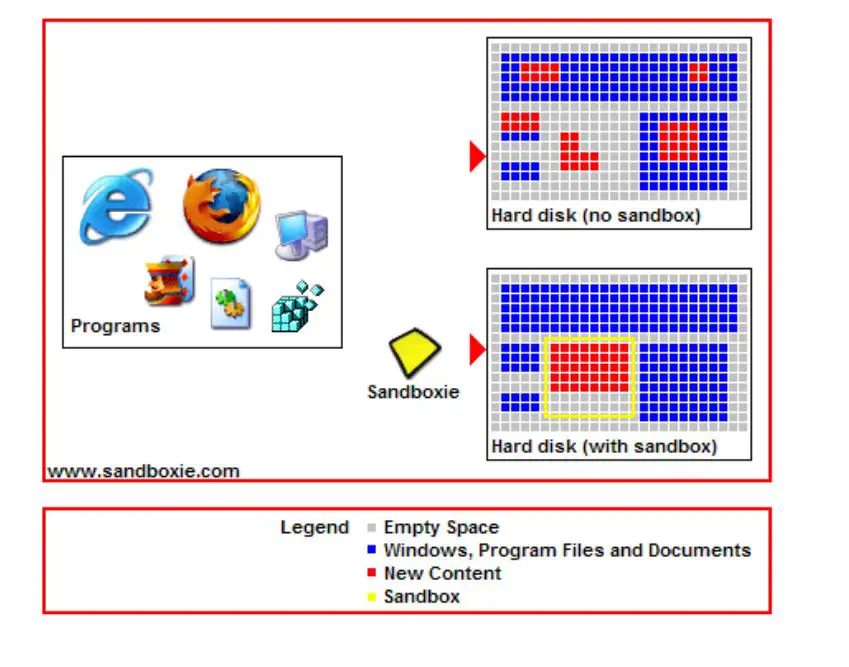
2. Oracle Cloud Infrastructure—Compute
Oracle Cloud Infrastructure (OCI) is another Sandboxie alternative. It can provide elastic and secure compute capacity in the cloud, ranging from flexible virtual machines to container management and orchestration, GPU, HPC, and high-performance bare metal servers.
Enterprise workloads spanning from modern cloud-native applications to the traditional back-office need economics, scalability, and choice, and all this is available on-demand with Oracle Cloud Infrastructure. Customers can choose from Arm-based compute shapes, AMD, and Intel.
OCI protects all applications and data by combining the layers of defense across the web-facing servers, physical hardware, and the network aligned to the hardened operational procedures.
OCI enables high performance and consistency across the HPC workloads, cloud-native, and enterprise by not oversubscribing to storage, network, and compute resources.
Something that works well for enterprise customers that need efficient, high-performance infrastructure while also being able to respond to all ongoing application demands consistently.
It also supports many prebuilt Oracle-provided images and custom, user-created images. You can choose from the popular Windows and Linux operating systems to run on bare metal or virtual machines, including Microsoft Windows, Ubuntu, CentOS, or Oracle Autonomous Linux.
It is also consistently less expensive as compared to AWS. Their instances are 75% less expensive, and the cost-effect data egress pricing lets customers love data to and from the cloud inexpensively.
Pros:-
- The interface is simple and easy to use.
- It has all the features you would want for cloud data center infrastructure.
- Pricing is reasonable.
Cons:-
- Termination time is longer than expected.
- It can be difficult to manage the load by provisioning gears in the same host for large-scale applications.
3. Apache Mesos – Sandboxie free alternative
This Sandboxie alternative states that it can let you program against the data center as if it is one pool of resources.
Apache Mesos abstracts storage, memory, CPU, and other compute resources away from any virtual or physical machines, thereby enabling elastic and fault-tolerant distributed systems to be built and run easily and effectively.
Mesos can also be called a distributed systems kernel. It is built with the same principles used for the Linux kernel, but the level of abstraction here is different.
The kernel will run on every machine, providing applications like Elasticsearch, Kafka, Spark, and Hadoop, with the APIs needed for scheduling and resource management across entire cloud environments and data centers.
The scalability is linear and is industry-proven to scale to 10,000s nodes with ease. There is a high availability of fault-tolerant replicated agents and masters using Zookeeper, and the upgrades are non0disruptive.
There is also native support for launching containers with AppC images and Docker. To get custom resource isolation, you will also get first-class isolation support for modules, GPU, ports, disk, memory, and CPU.
Mesos offers support for running legacy and cloud-native applications in the same cluster, along with pluggable scheduling policies. There are HTTP APIs, so you monitor, operate the cluster and develop new distributed applications.
You will find a built-in WEB UI for navigating container sandboxes and viewing cluster states. It runs on Windows, OSX, and Linux.
Pros:-
- You can use frameworks here.
- There is stability, and problems are often not because of Mesos itself.
- There is a great community for support and queries.
Cons:-
- UI is not very user-friendly.
- It can be difficult to debug a task at times.
4. OpenVZ
Open VZ is a source container-based virtualization that works for Linux and is a Sandboxie alternative that is a bit limited. But it is a great free, open-source software that comes under GNU GPL.
Multiple isolated, secure Linux containers known as VPSs or VEs are on a single physical server, ensuring that applications do not conflict and enabling better server utilization.
Every container executes and performs just like a stand-alone server. Containers can have root access, configuration files, system libraries, applications, files, processes, memory, IP addresses, and users and can be rebooted independently.
It is important to note that though virtualization technologies like KVM, Xen, and VMware provide complete virtualization and can run different kernel versions and multiple operating systems, OpenVZ can run only Linux as it uses a single Linux kernel, which is why it is said to be limited.
All of the OpenVZ containers have the same kernel version and architecture, so it may not be a good fit if you would need different kernel versions than that of the host. But since it does not have the overhead of a true hypervisor, it is very efficient and fast.
Memory allocation using OpenVZ is soft in that memory not being used by one virtual environment could be used for either disk caching or for others.
In older versions of OpenVZ, you would find that chroot was used to isolate the directory of files, which was basically what the virtual environments were. But the newer current versions allow every container its file system.
Pros:-
- Installation is easy.
- Management is simple.
- There are no complex upgrades or workarounds.
Cons:-
- The Dockerization feature is not available.
- Not enough support from developers for bugs.
5. Open Container Initiative – Sandboxie alternative for games
The Open Container Initiative is a Sandboxie Alternative and is an open governance structure made to create open industry standards around runtime and container formats.
It is a collaborative project hosted under the Linux Foundation so that common standards for containers can be established.
The open governance structure here is lightweight. It was unveiled on the 22nd of June, 2015, as the Open Container Project at DockerCon but later renamed to the Open Container Initiative (OCI) as we know it today.
OCI has support from quite a few prominent companies, but the project itself is something that will remain independent from any commercial organization. Its founders include Google, Goldman Sachs, INM, Red Hat, Nutanix, EMC, VMware, Microsoft, CoreOS, Docker, and Amazon Web Services.
In fact, Docker was quite pivotal in donating draft specifications, a lot of the existing code for the container runtime, image formate, and founding the initiative.
OCI’s formation was driven by the interest in container-based virtualization that was rapidly rising and also as a method of increasing application portability in and across multiple environments.
This project’s core goals are to ensure that the standards for containers and any future container platforms reserve containers’ open and flexible nature.
They say containers should be bound to a particular orchestration stack or client or be associated with a vendor tightly but should be portable across various architectures, hardware, and operating systems.
Pros:-
- Egress cost is low.
- The database is self-managing, self-repairing, and self-tuning.
- Monitoring of infrastructure is simple.
Cons:-
- Navigation within UI/Console can be a little complicated.
- It is challenging to build in OCI when it comes to multi-tier architecture.
6. Canonical LXD – Sandboxie alternative For Linux
The LXD project was founded and is led by Canonical Ltd while having contributions from other individual contributors and companies.
It is a great Sandboxie alternative and is said to be the next-generation system container manager; it offers a user experience like virtual machines, but Linux containers are used here.
LXD is image-based and has pre-made images available for several Linux distributors while being built around a simple yet powerful REST API.
It is secure by design as it offers things like resource restrictions, unprivileged containers, and more. It is also scalable from the containers on your system or laptop to thousands of compute nodes.
It is also intuitive, with a clear and simple API and a crisp command-line experience. It is image-based, and various Linux distributions are published daily. There is support for cross-host image transfer and container, including live immigration, that comes with CRIU.
Device passthrough includes paths, disks, NICs, block devices, UNIX characters, GPU, and USB. There is also great network management involving cross-host tunnels, bridge configuration and creation, and much more. Storage management is also available with support for multiple storage volumes, storage pools, and storage backends.
It works with any recent Linux distribution, and the upstream will directly maintain the Ubuntu packages. It also publishes a snap package that can be used with the most common and popular Linux distributions. It is not a rewrite of LXC but builds on top of LXC for a better user experience.
Pros:-
- It gives high performance.
- It has powerful servers for robust architectures.
- LXD is secure, scalable, and intuitive.
Cons:-
- Does not have a configuration and administration interface.
- Configurations can be complex.
7. Turbo
Turbo is a Sandboxie alternative and is a set of services and software products developed by the Code Systems Corporation for digital distribution, portable application creation, and application virtualization.
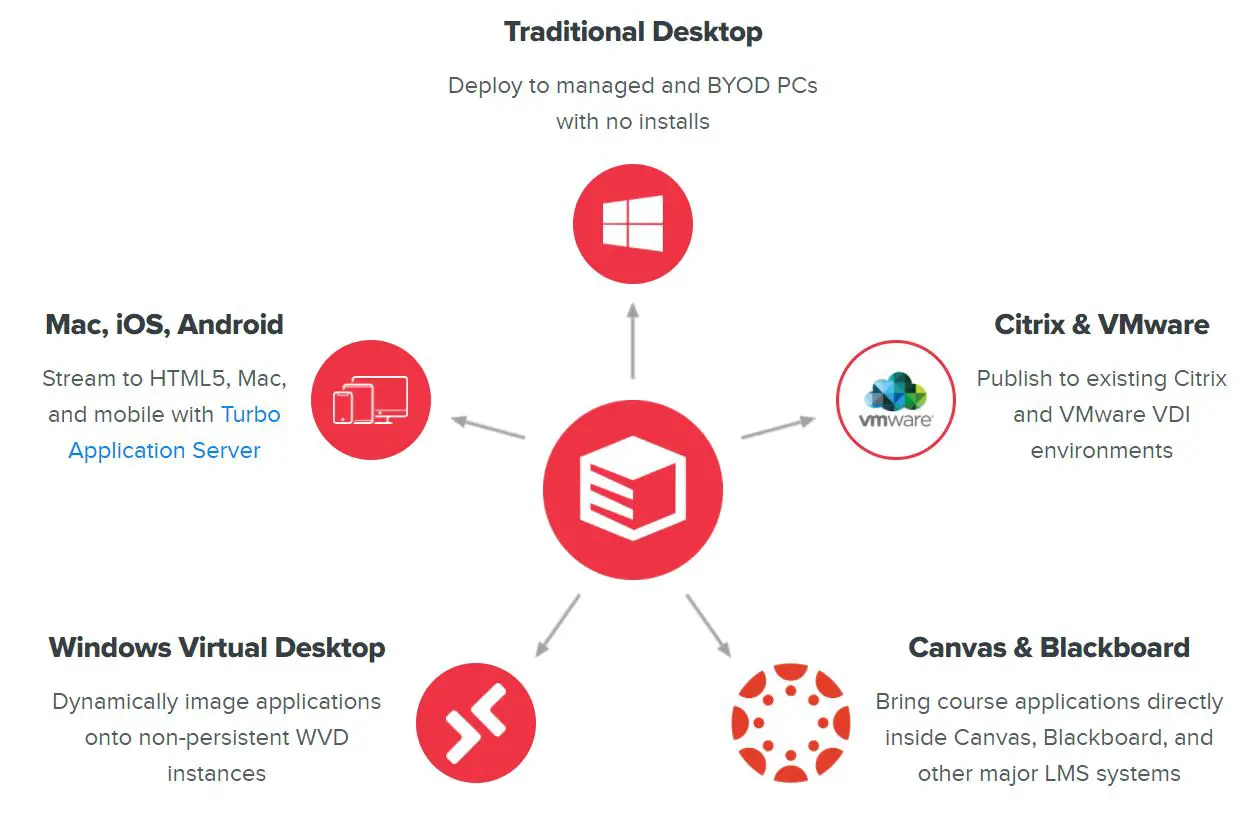
The website hosts applications that can be launched without installation and via the web. The application library includes software like SketchUp, VLC Media Player, Skype, Chrome, and hundreds of other free, open-source applications; it works via a small browser plugin, and no drivers or administrative privileges are necessary.
It functions as a tool for individuals but is also used by professionals and larger workforces, even those that are remote or distributed.
Turbo combines Turbo browsers with Selenium, so there is unlimited automated browser testing, which has increased the utilization of Turbo as web development and testing tool.
It works by materializing a virtual environment on endpoint devices. It transfers the application components needed for execution, captures the application interactions through the storage system right to a sandbox, and then synchronizes the contents of the sandbox to the cloud.
The Turbo Virtual Machine (SVM) is an implementation of core operating system APIs, and it includes the threading subsystems, process, registry, and filesystem while all being lightweight. It is also implemented within the Windows user-mode space completely.
Applications executing within the virtual Turbo environment interact with the virtualized filesystem registry and then process the environment instead of directly using the host device operating system.
The virtualization engine is what handles the requests in the virtualized environment internally or will route the request to the host device filesystem when appropriate.
Pros:-
- Portable and easy to use.
- You don’t need to virtualize the entire operating system but can virtualize only the application required.
- It is extremely flexible.
Cons:-
- The initial build process can be complex.
- Not easy for beginners.
8. Windows Sandbox – Free Sandboxie alternative with Window 10 Pro
Windows Sandbox is another Sandboxie alternative in our list and is a lightweight desktop environment where you can run applications safely and in isolation.
Any software that is installed inside the environment of the Windows Sandbox will stay sandboxed and will run separately from the host machine.
The sandbox here is temporary and, when closed, will delete all the files and software. Every time you open the application, you get a brand-new sandbox instance.
As it is a part of Windows, there is no need to download a VHD, and everything you would need comes with Windows 10 Pro and Enterprise.
You will get a clean and brand-new installation of Windows each time you run the Windows Sandbox. As mentioned, everything gets discarded, and absolutely nothing will persist on the drive when the application is closed by the user.
Hardware-based virtualization is used for kernel isolation. The Microsoft hypervisor is relied on to run a separate kernel that will isolate Windows Sandbox from the host, making it very secure.
It is also efficient as it uses smart memory management, the integrated kernel scheduler, and a virtual GPU.
The Windows 10 Pro of Enterprise (with the build version 18305 0r later) is needed for installation. You will also have to enable virtualization on the machine.
Virtualization capabilities in the BIOS need to be enabled for a physical machine. And for a virtual machine to enable nested virtualization, a PowerShell command is needed.
Pros:-
- It is lightweight, and setting up is quick and easy.
- Any process within the environment is isolated from the main installation.
- There are no extra steps required to create or download a virtual machine.
Cons:-
- Changes you want to retain while running the sandbox can be complex to maintain.
- If your browser is sandboxed, getting a downloaded file you want to use outside the sandbox will need more steps.
📗FAQ
Is there another program like Sandboxie?
Docker Hub, Oracle Cloud Infrastructure, Apache Mesos, OpenVZ, Open Container Initiative, etc., are some of the most similar programs like Sandboxie and can make your life much easier as a developer.
Is Sandboxie still free?
Yes, Sandboxie is a free application with aspirations to make it an open-source application.
Can Sandboxie run malware?
No. While Sandboxie is an anti-malware measure, it functions differently from conventional anti-virus software.
Sandboxie does not make an effort to distinguish between “good” and “bad” (or hazardous) apps, unlike an anti-virus.
An anti-virus program could fail to detect a new virus, allowing it to infect your machine. While Sandboxie forbids any software from altering your computer, it views all programs as potentially hazardous.
How secure is Sandboxie?
Using Sandboxie would be very safe for you. However, it should be highlighted that occasionally, users can identify a weakness in Sandboxie, an unpatched opening through which harmful software can still enter the system.
The attack vector hole is immediately sealed to prevent this, which is quite uncommon. So having more conventional anti-malware software is a good idea.
What happened to Sandboxie?
The purchasing options remained absent between May and September 2019 (when Sandboxie became freeware).
Software engineer David Berdik scraped the Sandboxie website’s content in response to the closing notice and posted the archive on GitHub on May 10, 2020.
Does Windows 10 have a sandbox?
Yes, the sandbox in Windows 10 has the following features:-
- Everything needed for this capability is included with Windows 10 Pro and Enterprise as it is a component of Windows. No need to get a VHD!
- Each time Windows Sandbox is used, it is as spotless as a fresh installation of Windows.
- Disposable means that nothing stays on the device after you close the application; everything is discarded.
- Secure – runs a separate kernel that isolates Windows Sandbox from the host using hardware-based virtualization, which relies on Microsoft’s hypervisor.
- It utilizes a virtual GPU, an integrated kernel scheduler, and smart memory management to be efficient.
Conclusion on the Sandboxie alternative list
We hope this article has helped you find a Sandboxie alternative that works best for you and is by your budget and work.
Many of them allow for collaborative work; some are free, while others you will need to pay for. But the ones that require payment are worth the money for all the features you have access to.
If you work across different platforms and need something that will let you do that, something like Docker Hub, Oracle, or Apache might be the right fit. Open VZ, on the other hand, is only for Linux and Windows Sandbox, as the name suggests for Windows.
What’s left now is for you to choose the perfect software so you can get to work and even introduce it to your team of developers.