In today’s digital era, online privacy and security are paramount. It’s never been more critical to safeguard your data from prying eyes, whether you’re an investigative journalist, a privacy advocate, or just an everyday user concerned about the safety of your information.
However, finding the right tools to ensure your online anonymity can be a perplexing task, with many options available and each claiming to offer the best protection. Two such options often come up in discussions about internet security are Whonix and Tails.
While both Whonix and Tails have their merits, choosing the right one for your needs isn’t always straightforward. Should you opt for Whonix’s layered security model that isolates your workspace from potential threats?
Or should you choose Tails for its unique amnesic feature, leaving no trace behind after your session? Without comparing these systems, you might choose the wrong tool for your needs, compromising privacy or causing unnecessary complications.
That’s where this article comes in. We’ll dive deep into the Whonix vs Tails debate, analyzing the key differences, strengths, and weaknesses of each. We aim to provide you with a comprehensive understanding of these platforms so you can make an informed choice and achieve maximum online security and privacy.
So, read on as we unravel the complexity of these privacy-focused operating systems and guide you toward making the right choice for your unique needs.
Understanding Whonix: Unraveling the Depths of Online Anonymity
In an era where data breaches, surveillance, and online tracking have become commonplace, safeguarding our digital privacy has become paramount.
Whonix, an open-source privacy-focused operating system, offers a robust solution for individuals seeking to enhance their online anonymity and protect their sensitive information from prying eyes.
Whonix derives its name from the combination of “Whonix Gateway” and “Whonix Workstation,” providing a unique and highly secure virtualization approach that separates the user’s applications from the internet.
Using VirtualBox as its hypervisor, Whonix ensures that users’ online activities are routed through the Tor network. This anonymity-focused overlay network conceals the user’s IP address and encrypts data at multiple levels.
Whonix consists of two distinct components, each serving a vital purpose in the pursuit of online anonymity. The Whonix Gateway is a virtual machine that channels all internet traffic through the Tor network.
It acts as a middleman between the user’s applications and the outside world, effectively stripping away identifiable information and location data, leaving the user’s digital footprint virtually untraceable.
On the other hand, the Whonix Workstation provides a secure and isolated environment where users can access the internet and perform various tasks without compromising their identity.
The Workstation communicates exclusively with the Gateway, ensuring all internet-bound traffic is directed through the Tor network. This two-tiered system adds an extra layer of security, preventing any accidental leaks of sensitive information.
One of the key advantages of Whonix lies in its “amnesic” nature. Since Whonix runs within a virtual environment, all changes made during a session are confined to the virtual machine.
Any malware, tracking cookies, or unwanted files that may infiltrate the system will be discarded once the session ends, leaving no lasting impact on the user’s host system.
As an isolated and anonymous operating system, Whonix shields users from various online threats, such as malicious websites, tracking attempts, and man-in-the-middle attacks. This level of protection is especially critical for journalists, activists, whistleblowers, and any individual seeking to exercise their right to free speech without fear of retribution or surveillance.
While Whonix offers a formidable defense against online adversaries, users must remain vigilant and adhere to best practices to maximize their anonymity. For instance, combining Whonix with a VPN service can provide an additional layer of encryption and further obscure the user’s identity. It’s essential to avoid logging into personal accounts or revealing any personally identifiable information while using Whonix to maintain a strong shield of anonymity.
Moreover, Whonix does not protect against all threats on its own. Users must still exercise caution with the websites they visit, the files they download, and the information they share. Cybersecurity awareness and education remain integral components of a robust online defense strategy.
In conclusion, Understanding Whonix is paramount for anyone seeking to reclaim their online privacy and anonymity. With its innovative approach to virtualization, Whonix offers a secure and isolated environment that routes all internet traffic through the Tor network, ensuring that users’ identities and sensitive information remain hidden from prying eyes.
While not infallible, Whonix is a potent tool for protecting digital privacy in an increasingly interconnected and surveilled world. By combining Whonix with other privacy-enhancing measures and practicing cybersecurity awareness, individuals can fortify their online defenses and regain control of their digital lives.
Advantages of Whonix
Whonix offers many advantages that set it apart from conventional operating systems, making it an exceptional choice for those seeking to maintain high online security and anonymity.
Virtualized Protection: At the core of Whonix lies its unique virtualization approach. By leveraging VirtualBox as its hypervisor, Whonix creates a segregated environment where all internet traffic is routed through the Tor network. This ensures that user applications are isolated from the outside world, shielding them from potential attacks and data breaches.
Anonymity Assurance: Whonix takes anonymity seriously. By employing the Tor network, it effectively conceals the user’s IP address. It encrypts data, making it incredibly challenging for malicious entities or prying eyes to track or monitor online activities.
Gateway and Workstation Architecture: The separation of the Whonix Gateway and Whonix Workstation adds an extra layer of security. The Gateway handles all internet communication, while the Workstation is dedicated to user applications. This two-tiered structure prevents unintentional leaks of sensitive information, ensuring maximum privacy.
Amnesic Nature: One of the remarkable advantages of Whonix is its amnesic nature. Since it runs in a virtual environment, all changes made during a session are discarded once it ends. This erases any trace of potential malware or tracking cookies, leaving the user’s host system unaffected.
Security for High-Risk Users: Whonix caters to individuals who require a higher level of security, such as journalists, activists, and whistleblowers. By safeguarding their identities and activities, Whonix empowers them to exercise their rights to free speech and information without fear of retribution.
Enhanced Privacy with VPN: Whonix can be used with a VPN service for those seeking an extra layer of encryption. This combination bolsters the already robust anonymity provided by Whonix, further protecting user data.
Open-Source Community: Being an open-source project, Whonix benefits from a collaborative community. Regular updates and contributions from cybersecurity experts ensure the system remains up-to-date and fortified against emerging threats.
In conclusion, Whonix is a testament to the power of privacy-centric operating systems. Its virtualized protection, anonymity assurance, and amnesic nature offer unparalleled advantages for safeguarding online anonymity.
Whether you are an average user seeking to bolster your digital privacy or a high-risk individual aiming to protect sensitive information, Whonix provides the tools and security needed to navigate the online world confidently and safely.
Limitations of Whonix
Whonix, a commendable effort in bolstering online anonymity, has its limitations. While it stands as a stalwart guardian of privacy, understanding these boundaries is essential for comprehensively evaluating the system’s capabilities.
Below, we explore some of the key limitations of Whonix:
Resource Intensive: As a virtualized environment, Whonix demands substantial computing resources. Running the Whonix Gateway and Whonix Workstation simultaneously can strain older or less powerful hardware, potentially leading to decreased system performance.
Connection Speed: Internet traffic routing through the Tor network can lead to reduced connection speeds. Users may experience slower browsing and download times, especially when accessing bandwidth-intensive content.
DNS Leaks: Despite its robust architecture, Whonix is not immune to potential DNS leaks. In certain scenarios, user applications may bypass the Tor network and directly query the DNS server, compromising anonymity.
Limited Application Support: Due to the isolation provided by Whonix, not all applications may function seamlessly within the environment. Some software may require additional configuration or may not be compatible at all.
User Awareness: To maintain high anonymity, users must remain vigilant and knowledgeable about potential risks. Incorrect configurations or lapses in security practices can inadvertently expose sensitive information.
Single Point of Failure: While separating the Gateway and Workstation adds security, it also introduces a potential single point of failure. If the Gateway is compromised, the entire system’s integrity may be at risk.
Exit Node Vulnerabilities: The Tor network relies on volunteer-run exit nodes to connect to the wider internet. These exit nodes may pose security concerns, as data passing through them can be intercepted.
Limited Protection Beyond Whonix: While Whonix provides a robust defense against online threats, it does not protect against all attack vectors. Users must exercise caution outside the Whonix environment to maintain their privacy.
High Learning Curve: Whonix may present a steep learning curve for less tech-savvy individuals. Proper setup and configuration require a degree of technical knowledge that may deter some potential users.
In conclusion, while Whonix undeniably serves as a formidable guardian of online anonymity, it is not without its limitations. The resource-intensive nature, potential connection speed reductions, DNS leaks, and the need for user awareness all contribute to the system’s boundaries.
Additionally, the reliance on exit nodes and the requirement for continued diligence beyond Whonix underscore the importance of informed and cautious use. Despite these limitations, Whonix remains a compelling choice for individuals seeking higher privacy and anonymity in the digital realm. Understanding these constraints enables users to make informed decisions and utilize Whonix effectively in their pursuit of online security.
Unveiling Tails: The Enigmatic Operating System for Privacy Advocates
Privacy-conscious individuals and security experts seek innovative solutions to protect online activities in an era of escalating digital surveillance and data breaches. One such remarkable tool that has garnered attention is Tails OS – “The Amnesic Incognito Live System.”
Developed with the core principle of leaving no trace, Tails is a live operating system designed to ensure user anonymity and privacy. This article delves into the brief history and developers of Tails, explores its core features, and explains the concept of a live operating system that maintains the utmost confidentiality.
Tails OS has its roots in the Debian Linux distribution and was initially released in 2009. The project was inspired by the growing demand for a secure and anonymous operating system that could be booted from a USB drive or DVD without leaving any digital footprint.
The development team behind Tails comprises dedicated individuals who prioritize user privacy and open-source principles. Their collaboration has enabled Tails OS’s continuous improvement and refinement, making it a powerful tool in the fight for digital anonymity.
Tails OS operates on a live operating system. This operating system can be booted and run directly from removable media, such as a USB drive or DVD, without the need for installation on the host computer.
This allows users to carry their secure and private environment, independent of the host machine’s configuration. Tails wipe all data when the user shuts down the system, leaving no trace of the session on the host computer.
The amnesic nature of Tails is made possible by running entirely in RAM, as opposed to saving data on the computer’s hard drive. This design ensures that no sensitive information, such as browsing history, documents, or login credentials, is left behind once the session ends. As a result, Tails is an ideal solution for users who require privacy and security without compromising convenience.
Advantages of Tails: Empowering Privacy and Security Advocates
In a world where digital privacy and security are constantly threatened, Tails emerges as a formidable solution for individuals seeking a secure and anonymous online experience.
Tails, also known as “The Amnesic Incognito Live System,” offers many advantages that set it apart as a preferred choice among privacy advocates and security-conscious users.
1. Enhanced Privacy and Anonymity
Tails provide a robust shield of privacy and anonymity through its tight integration with the Tor network. Tails conceal the user’s IP address by routing internet traffic through encrypted nodes, making it nearly impossible for anyone to trace online activities back to the source. This anonymity is crucial for journalists, activists, and whistleblowers, who must protect their identities while communicating sensitive information.
2. Amnesic Operation
One of the most remarkable advantages of Tails lies in its amnesic nature. When booted from a live USB or DVD, Tails operates solely from the device’s RAM, leaving no trace of activity once the session ends. This ensures that all data and settings are wiped clean, offering users a fresh start with every session and minimizing the risk of leaving behind sensitive information.
3. Portable and Versatile
As a live operating system, Tails is highly portable and can be booted on any computer with compatible hardware. This allows users to carry their secure environment, making it an ideal choice for individuals who require privacy on the go. Moreover, its versatility extends to its ability to function from various media, including USB drives and DVDs, providing convenient options for different user preferences.
4. Preinstalled Security Tools
Tails come with a preconfigured set of security tools and applications, empowering users with enhanced protection. From the Tor Browser for secure web browsing to email clients and encryption tools, Tails equips users with the necessary instruments to communicate safely and protect sensitive data.
5. Encrypted Persistence
Tails offer an option for encrypted persistence for users who require a personalized experience while maintaining the highest level of privacy. This allows users to create a secure and encrypted partition on their USB drive, where specific data and settings can be stored across sessions. The encrypted persistence feature strikes a balance between anonymity and personalization.
6. Security Against Malware and Attacks
Since Tails operates independently from the host computer’s hard drive, it provides an extra layer of security against malware and attacks that may compromise the host system. With its live and read-only nature, Tails ensures that any malicious software encountered during a session is discarded upon shutdown, safeguarding the user’s data and privacy.
7. Open-Source and Community-Driven
Tails is an open-source project, meaning its source code is accessible to the public, allowing for scrutiny and contributions from the community. This transparent and collaborative approach ensures continuous improvement and robust security measures, making Tails a community-driven effort to safeguard user privacy.
In conclusion, the advantages of Tails make it a standout choice for privacy and security-conscious individuals. Its integration with the Tor network provides enhanced anonymity, while its amnesic operation ensures a clean slate with every session.
The portability and versatility of Tails enable users to maintain their secure environment wherever they go. Including preinstalled security tools and the option for encrypted persistence further bolster its appeal.
With its commitment to open-source principles and community-driven development, Tails is a powerful tool for empowering users to take control of their online privacy and security, reclaiming their digital identities in a world of ever-evolving threats.
Limitations of Tails: Exploring the Boundaries of Online Anonymity
While it excels in providing users with a secure and discreet online experience, it is not without its limitations. Understanding these boundaries is crucial for users seeking to make informed decisions and harness the full potential of Tails.
1. Connection Speed and Tor Network
One of the primary limitations of Tails lies in the connection speed when using the Tor network. As data is routed through multiple nodes to ensure anonymity, this process can introduce latency, resulting in slower browsing speeds than traditional internet connections.
2. Hardware Compatibility
While Tails is designed to be versatile and portable, its functionality may be impacted by hardware compatibility issues. Certain devices or components may not be fully supported, which can lead to suboptimal performance or even prevent Tails from booting altogether on certain systems.
3. Data Persistence and Storage Vulnerability
While Tails boasts an amnesic nature, it does offer an option for encrypted persistence. However, this feature has limitations in terms of storage space. The size of the encrypted partition may be limited, restricting the amount of data that can be securely stored across sessions. Additionally, the physical storage device, such as a USB drive, could be lost or stolen, potentially compromising the security of stored data.
4. Complexity for Novice Users
The setup and configuration of Tails can be relatively complex, especially for novice users with limited technical expertise. Troubleshooting issues or customizing the system to suit individual needs may require a deeper understanding of Linux and related technologies.
5. Anonymity Precautions
While Tails prioritizes anonymity, users must remain vigilant about online behavior and activities. Engaging in potentially identifying activities, such as logging into personal accounts or revealing sensitive information, can compromise the effectiveness of Tails in maintaining privacy.
6. Lack of Automatic Updates
Unlike traditional operating systems, Tails does not provide automatic updates. Users are responsible for regularly checking for updates and manually applying them to ensure the latest security patches and improvements are implemented.
7. Single Point of Failure
Despite its amnesic nature, Tails relies on a physical storage device, such as a USB drive, to boot the operating system. This introduces a potential single point of failure. If the device becomes damaged, lost, or compromised, access to the secure environment of Tails may be jeopardized.
8. Limited Application Support
While Tails comes with a selection of preinstalled applications, it may not support all software users require. This can be a limitation for users who rely on specific applications for their work or other tasks.
In conclusion, while Tails excels as a privacy-oriented operating system, it is essential to be aware of its limitations. From connection speed and hardware compatibility to the complexity for novice users, each limitation informs users of the challenges they may encounter while using Tails.
Being mindful of the data persistence, taking appropriate anonymity precautions, and understanding the absence of automatic updates ensures users can navigate the boundaries and fully appreciate the remarkable privacy features that Tails has to offer.
Now let’s start with a Head-to-Head Comparison of Whonix vs Tails OS.
Whonix vs Tails: Comparison of the Installation Process
While both systems prioritize user anonymity and security, their installation process differs. Let’s compare how Whonix and Tails handle the installation and what sets them apart.
Whonix Installation Process:-
Whonix takes a unique approach to installation, employing a two-part architecture consisting of the Whonix Gateway and Whonix Workstation. The Gateway is responsible for handling all internet communication, while the Workstation is dedicated to running user applications.
The Whonix installation involves setting up two virtual machines (VMs). First, users must install supported virtualization software, such as VirtualBox or KVM, on their host system. Then, they download the Whonix Gateway and Whonix Workstation images and import them into the virtualization software.
The Whonix Gateway is configured as the network gateway for the Whonix Workstation, ensuring that all internet traffic is routed through the Tor network. This two-tiered virtualized approach offers an additional layer of security and isolation.
Tails Installation Process:-
In contrast, the Tails installation process follows a more straightforward and user-friendly approach. To start with Tails, users must download the Tails ISO image from the official website.
Once the Tails ISO image is downloaded, users can create a live USB or burn it to a DVD. This bootable media serves as the installation medium for Tails. Users then need to boot their computer from the USB or DVD, and Tails will start running live from the media without making any changes to the host system.
Tails offer the option to configure persistent storage if desired. This allows users to store specific data and settings securely across sessions. However, it is important to ensure the storage medium is encrypted and protected by a strong passphrase to maintain the highest level of security.
The Whonix installation process is more involved and may require technical proficiency with virtualization software. It provides a robust virtualized environment with separate Gateway and Workstation components, ensuring complete isolation and protection.
On the other hand, the Tails installation process is relatively straightforward, making it accessible to a broader audience, including novice users. It operates from a live USB or DVD, leaving no trace on the host system, making it a convenient and portable privacy solution.
In conclusion, the Whonix vs Tails comparison of the installation process reveals distinct approaches to achieving privacy and anonymity. Whonix relies on a virtualized two-part architecture, requiring the installation and configuration of separate Gateway and Workstation virtual machines. On the other hand, Tails offers a more user-friendly live operating system experience, requiring the creation of a bootable USB or DVD.
Whonix and Tails are valuable tools in the quest for online privacy, each with unique strengths and target audiences. The choice between the two ultimately depends on the user’s technical expertise, security requirements, and personal preferences in digital privacy and anonymity.
Whonix vs Tails: User Interface Comparison
When it comes to privacy-oriented operating systems, Whonix, and Tails are two prominent contenders, both vying for the attention of privacy-conscious users.
As users explore these options, one critical aspect to consider is the user interface of each system, as it directly impacts user experience and ease of navigation.
Let’s dive into a comparison of the user interface of Whonix and Tails to understand how they differ and what they offer.
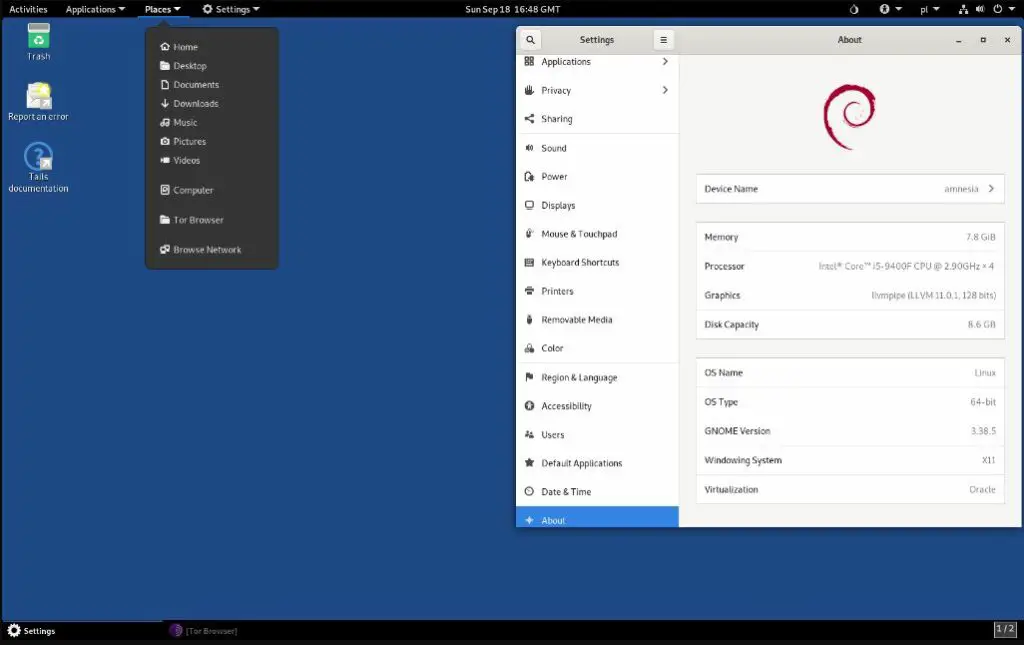
Whonix User Interface:-
Whonix presents users with a text-based interface during installation, requiring some familiarity with the command line. However, once installed, Whonix offers a graphical user interface (GUI) that closely resembles a standard Linux desktop environment.
This familiar layout allows users to interact with the system using icons, menus, and windows, providing a comfortable experience for those accustomed to traditional desktops.
The Whonix GUI employs a minimalistic design, focusing on functionality and efficiency. Its simplicity ensures that users can quickly access the tools and applications necessary for secure online activities. While the initial setup may require technical knowledge, the Whonix GUI offers an uncomplicated and streamlined daily user interface.
Tails User Interface:-
In contrast, Tails emphasizes a simplified and user-friendly interface from the outset. The system is designed to be accessible to users of all technical backgrounds, allowing them to boot directly from a live USB or DVD without requiring installation. This live environment ensures a seamless experience without altering the host system.
The Tails user interface is crafted to maintain a secure and private environment while being intuitive and straightforward. It incorporates a point-and-click approach from mainstream operating systems that users are familiar with. This includes a taskbar, a start menu, and pre-installed applications for secure communication, web browsing, and file management.
While Whonix and Tails are privacy-centric operating systems, their user interfaces cater to different audiences. Whonix caters to users with a slightly higher technical aptitude, as the initial setup involves the command line. However, it rewards users with a more standard desktop experience once installed.
On the other hand, Tails prioritizes accessibility for all users, offering a user-friendly and familiar point-and-click interface from the moment it boots. This makes it an excellent choice for individuals seeking a hassle-free and secure privacy solution.
In conclusion, the user interface comparison between Whonix and Tails demonstrates distinct approaches to user experience. Whonix provides a standard graphical desktop once the initial setup is complete, catering to users with some technical background. Tails prioritize accessibility and ease of use from the outset, appealing to a broader audience, including novice users.
Ultimately, the choice between Whonix and Tails depends on the user’s comfort with the initial installation process and preference for a more traditional Linux desktop environment or a streamlined and user-friendly live operating system.
Both options offer robust privacy features, and understanding the user interface can help users make informed decisions based on their specific needs and preferences.
Whonix vs Tails: Security Features Comparison
In the realm of privacy-oriented operating systems, Whonix, and Tails have earned commendable reputations for their strong emphasis on security. As users seek the highest level of protection for their online activities, comparing the security features of Whonix and Tails becomes crucial.
Let’s delve into the security offerings of both systems to understand how they differ and how they prioritize user safety.
Whonix: Fortifying Security with Isolation
Whonix employs a unique approach to security, focusing on isolation as its primary defense mechanism. It utilizes a two-part architecture consisting of the Whonix Gateway and Whonix Workstation.
The Whonix Gateway is a separate virtual machine (VM) responsible for handling all internet traffic. Routing all communications through the Tor network ensures that the user’s IP address is concealed and online activities remain anonymous.
The Whonix Workstation is another VM dedicated to running user applications. As all internet communication is channeled through the Whonix Gateway, the Workstation remains isolated from the host system and any potential threats lurking on it.
This air-gapped design of Whonix provides an extra layer of security, preventing direct communication between the host system and the internet.
Tails: Emphasizing Live and Amnesic Operation
On the other hand, Tails focuses on two fundamental aspects of security – live operation and amnesic nature. As a live operating system, Tails can be booted directly from a USB drive or DVD without the need for installation on the host system. This ensures that the host remains unaffected by any potential malware or malicious activities.
The amnesic nature of Tails guarantees that all data and activities are wiped clean once the session is terminated. No trace of user activity is left on the host system or the Tails media, safeguarding the user’s privacy and ensuring no sensitive information remains exposed.
Furthermore, Tails offers an optional encrypted persistence feature, allowing users to store specific data and settings across sessions securely. This ensures a personalized experience while still maintaining a high level of privacy and protection.
Both Whonix and Tails excel in providing robust security features, but their approaches differ significantly.
Whonix prioritizes isolation to prevent direct communication between the host system and the internet. Using separate VMs for the Gateway and Workstation creates a secure environment for online activities.
On the other hand, Tails emphasizes live operation and the amnesic nature of its operation. The live booting feature ensures a clean slate with each session, while the encrypted persistence option enables users to strike a balance between privacy and personalization.
In conclusion, the security features comparison between Whonix and Tails reveals distinct approaches to safeguarding user privacy and protection.
Whonix relies on isolation through its two-part architecture, creating a secure and private environment for online activities.
Tails, on the other hand, emphasizes live operation and the amnesic nature of its operation. By ensuring that no trace of activity remains, Tails provides users with a fresh start with each session.
Both Whonix and Tails are powerful tools in the quest for online security, and the choice between the two depends on the user’s specific security requirements and preferences. Understanding the security features offered by each system allows users to make informed decisions and confidently navigate the digital realm with a heightened sense of privacy and protection.
Whonix vs Tails: Anonymity and Privacy Features Comparison
In the realm of privacy-centric operating systems, Whonix, and Tails have emerged as two prominent contenders, each offering robust anonymity and privacy features.
As users seek to navigate the digital landscape with a heightened sense of confidentiality, comparing the anonymity and privacy features of Whonix and Tails becomes essential.
Let’s explore the strengths of each system to understand how they prioritize user anonymity and safeguard personal information.
Whonix: Maximizing Anonymity through the Tor Network
Whonix strongly emphasizes anonymity, achieved primarily through its integration with the Tor network. The two-part architecture, consisting of the Whonix Gateway and Whonix Workstation, ensures that all internet traffic is routed through the Tor network, concealing the user’s IP address and providing high anonymity.
The Whonix Gateway is an intermediary between the host system and the internet, acting as a secure entry point into the Tor network. All network connections from the Whonix Workstation are routed through the Whonix Gateway, ensuring the user’s online activities remain anonymous and untraceable.
Additionally, Whonix employs various security measures, including full disk encryption, to protect user data and maintain privacy even in the event of physical access to the system.
Tails: A Comprehensive Privacy-First Approach
Tails embrace a comprehensive privacy-first approach, offering various features to safeguard user anonymity and personal information. As a live operating system, Tails can be booted directly from a USB drive or DVD, ensuring that the host system remains untouched and no trace of user activity is left behind.
One of the standout features of Tails is its amnesic nature, which ensures that all data and activities are wiped clean from the system once the session ends. This helps maintain the user’s anonymity by leaving no digital footprint or history of online activities.
Moreover, Tails tightly integrates with the Tor network, enabling secure and anonymous web browsing. All internet traffic is automatically routed through the Tor network, preventing anyone from tracing the user’s online activities to their IP address.
The option for encrypted persistence allows users to securely store specific data and settings across sessions, providing a personalized experience while prioritizing privacy.
Both Whonix and Tails excel in providing anonymity and privacy features, but their approaches differ in certain aspects.
Whonix focuses on maximizing anonymity through its integration with the Tor network and its two-part architecture, offering a secure and isolated environment for online activities.
On the other hand, Tails emphasizes a comprehensive privacy-first approach, utilizing live booting and amnesic operation to ensure that no trace of user activity remains.
In conclusion, the anonymity and privacy feature comparison between Whonix and Tails reveals distinct approaches to safeguarding user confidentiality and protecting personal information.
Whonix prioritizes anonymity through its integration with the Tor network and secure architecture.
Tails adopt a privacy-first approach, ensuring no trace of user activity is left behind and incorporating features like live booting and amnesic operation.
Both Whonix and Tails offer powerful tools for users seeking a privacy-focused operating system, and the choice between the two depends on the user’s specific needs and preferences. Understanding each system’s anonymity and privacy features empowers users to make informed decisions and confidently embrace a more secure and anonymous online experience.
Whonix vs Tails: Use Case Scenario Comparison
Let’s compare the use case scenarios for Whonix and Tails to gain insights into how they excel in different contexts.
Whonix: Maximum Anonymity and Online Privacy
Whonix is a formidable choice for users prioritizing maximum anonymity and online privacy. Its unique two-part architecture, consisting of the Whonix Gateway and Whonix Workstation, offers unparalleled isolation and security.
One of the primary use case scenarios for Whonix is for users who need to access the internet while ensuring their online activities remain anonymous and untraceable. By routing all internet traffic through the Tor network, Whonix conceals the user’s IP address, providing a robust shield against surveillance and tracking.
Another compelling use case for Whonix is for individuals engaged in sensitive research or communication. It offers a safe and secure environment where users can communicate, share information, or conduct investigations without leaving any digital footprints.
Moreover, Whonix is well-suited for users who require a highly private and isolated workspace for tasks that demand an added layer of protection, such as cryptocurrency transactions or whistleblowing activities.
Tails: On-the-Go Anonymity and Temporary Sessions
Tails excel in use-case scenarios where users prioritize on-the-go anonymity and require temporary sessions. As a live operating system, Tails can be booted directly from a USB drive or DVD, making it portable and convenient for users who need a secure environment while using public computers or untrusted networks.
One of the primary use case scenarios for Tails is for users who require a quick and secure online session without leaving any traces on the host system. This is ideal for individuals accessing sensitive information or conducting confidential tasks while maintaining high privacy.
Another compelling use case for Tails is for journalists, activists, or travelers who must communicate securely and access information while moving. The amnesic nature of Tails ensures that all data and activities are wiped clean once the session is terminated, making it an excellent choice for temporary usage.
Moreover, Tails is well-suited for users who need a versatile and portable operating system for security assessments, penetration testing, or ethical hacking endeavors.
While both Whonix and Tails are privacy-centric operating systems, they cater to different use case scenarios based on their unique strengths and features.
Whonix is ideal for users who require maximum anonymity and need an isolated and secure environment for long-term activities or sensitive tasks.
Tails, however, is perfect for users who prioritize on-the-go anonymity and require a temporary and portable operating system for secure communication and browsing.
In conclusion, the use case scenario comparison between Whonix and Tails reveals distinct strengths that cater to different privacy needs.
Whonix excels when users demand maximum anonymity and a secure workspace for long-term activities or sensitive tasks.
Tails is well-suited for scenarios where on-the-go anonymity and temporary sessions are paramount, making it ideal for portable and secure usage in various contexts.
Ultimately, the choice between Whonix and Tails depends on the user’s specific needs and requirements for privacy and security. Understanding their respective use case scenarios empowers users to make an informed decision, ensuring that their chosen operating system aligns perfectly with their digital privacy goals.
Whonix vs Tails: Community and support comparison
When choosing a privacy-oriented operating system, having a strong community and reliable support can significantly affect the overall user experience. Whonix and Tails have passionate communities behind them, providing valuable resources and assistance.
Let’s compare the community and support for Whonix and Tails to understand how they stack up in this critical aspect.
Whonix Community and Support
Whonix has cultivated a dedicated and active community of users, developers, and privacy enthusiasts. Their official website is a hub for users to access the latest documentation, guides, and FAQs, providing a wealth of knowledge for troubleshooting and customization.
The Whonix community thrives on open-source principles, encouraging user engagement and contributions to the project. Users can actively participate in discussions, report issues, and suggest improvements through their forums and mailing lists.
Additionally, Whonix benefits from continuous updates and improvements due to its open-source nature, with developers worldwide contributing to its growth and security.
For support, the Whonix community is known for its responsiveness and helpfulness, making it an excellent choice for users seeking a welcoming and informative space.
Tails Community and Support
Similar to Whonix, Tails also boasts an active and engaged community. Their website provides extensive documentation and a comprehensive knowledge base, offering guidance on various topics related to Tails usage and troubleshooting.
The Tails community encourages user feedback and involvement, allowing users to report bugs, suggest features, and participate in discussions. Their communication channels, including mailing lists and forums, facilitate collaboration and peer-to-peer assistance.
In terms of support, the Tails community is known for being responsive and attentive to user inquiries. Their commitment to user privacy and security ensures that users receive prompt and helpful responses.
Both Whonix and Tails enjoy strong communities that actively contribute to the growth and development of their respective projects. The Whonix community thrives on open-source principles and embraces user engagement, while the Tails community emphasizes user privacy and feedback.
Regarding support, both communities are known for their responsiveness and willingness to assist users, creating a positive and nurturing environment for individuals seeking help or information.
In conclusion, the community and support comparison between Whonix and Tails reveals that both operating systems enjoy passionate communities committed to user engagement and project development. Whether users opt for Whonix or Tails, they can rest assured that they will have access to valuable resources, knowledgeable peers, and reliable support.
Ultimately, the choice between Whonix and Tails may come from user preference and specific privacy needs. The strong community backing ensures that users can confidently navigate these privacy-centric operating systems, knowing they have a supportive network of individuals dedicated to safeguarding their online privacy and security.
Whonix vs Tails: System Requirements Comparison
The Whonix vs Tails: System Requirements Comparison presents an intriguing insight into two formidable privacy-focused operating systems. These systems have been meticulously designed to furnish end-users with robust security and anonymity online, yet they demand different resources from your hardware.
When evaluating Whonix, its system requirements are somewhat more lenient than its competitor, Tails. A virtual machine environment, such as VirtualBox or Qubes, is required to run Whonix.
This implies that your system needs sufficient processing power and memory to operate a virtual machine with your primary operating system. As a rule of thumb, a dual-core processor and 4GB of RAM should be an adequate baseline for most users.
On the other hand, Tails operates as a live operating system, which means it is typically booted from a USB stick or a DVD. Consequently, it does not necessitate as much processing power or memory as Whonix, making it an ideal choice for older or less powerful hardware. Tails require a minimum of 2GB RAM and can run on almost any computer built in the last decade.
The Whonix vs Tails: System Requirements Comparison demonstrates that while both operating systems are steadfast in their commitment to privacy and security, they accommodate different user requirements and system specifications. Whonix fits newer, more robust hardware users who demand the added security benefits of operating within a virtual machine.
Conversely, with its minimalistic system requirements, Tails offers a flexible solution for individuals with older hardware or those seeking a portable privacy-focused operating system.
This comparison is a testament to the dynamic landscape of privacy-focused operating systems, where user choice and system constraints are expertly catered for. Both Whonix and Tails have etched out a niche in this sphere, serving different user needs while never compromising on the ultimate goal: user privacy and online security.
Here’s a comparison table between Whonix and Tails:-
| Feature | Whonix | Tails |
|---|---|---|
| Main Purpose | Privacy-focused operating system | Privacy-focused, amnesic operating system |
| Anonymity | Built-in Tor integration for high anonymity | All network connections are routed through Tor |
| Security Model | Isolation through Tor and VMs (Virtual Machines) | Ephemeral session-based model |
| Usability | Primarily used for tasks requiring high anonymity | Primarily used for tasks requiring high anonymity |
| Installation | More complex due to VM requirement | Can be installed and run from a USB stick or DVD |
| Applications | Applications primarily focused on privacy | Pre-installed with a set of privacy-centric applications |
| Networking | All network traffic is routed through Tor | All network traffic is routed through Tor |
| Updates | Regular updates, including Tor | Regular updates, plus entire system is wiped between uses |
| Underlying OS | Based on Debian | Also based on Debian |
| Persistence | Persistent system, saves changes between sessions | Non-persistent by default, with optional encrypted persistence |
| Threat Model | Protects against global passive adversaries, at risk of targeted attacks | Protects against both mass surveillance and targeted attacks, session-based |
| Ease of Use | Slightly more complex for beginners due to Tor and VM usage | More user-friendly due to live boot, but anonymity features require some learning |
Whonix vs Qubes vs Tails
In today’s technological epoch, privacy and security in operating systems are paramount concerns. This brings us to an insightful exploration of three unique, privacy-focused systems – Whonix, Qubes, and Tails.
Each of these platforms, while sharing the same objective of fortifying user security and preserving online anonymity, manifests their privacy doctrines in a uniquely specialized manner.
When dissecting the distinct offerings of these operating systems, we first turn our attention to Whonix. An OS housed within a virtual machine environment, Whonix’s principal advantage lies in its strict network-level compartmentalization.
Isolating network and non-network activities into separate entities ensures that any potential malware remains confined within its realm, negating its ability to leak your real IP address. To run Whonix, your hardware should pack a punch. A dual-core processor and a minimum of 4GB RAM are recommended, alongside a host machine capable of running VirtualBox or Qubes.
Speaking of Qubes, this operating system applies compartmentalization to all aspects of your computer activities, not just network interactions. In the Qubes environment, everything is isolated – your browser, email client, or word processor.
This comprehensive level of compartmentalization, known as security through isolation, can thwart even the most resolute of malicious attacks. However, this beefed-up security approach calls for beefed-up system resources. Qubes stipulates a 64-bit Intel or AMD processor, a minimum of 4GB RAM (though 16GB is recommended), and at least 32GB of disk space for a comfortable experience.
Finally, we come to Tails in this Whonix vs Qubes vs Tails comparison. Tails’ primary selling point is its amnesic nature, which leaves no trace of the user’s activities once the session is terminated. The Tails OS is a live operating system typically booted from a USB stick or DVD, allowing for remarkable portability.
Tails have the lowest system requirements of the trio, requiring just 2GB RAM and the ability to boot from a USB or DVD. This makes it an excellent choice for those with older or less powerful hardware.
The Whonix vs Qubes vs Tails debate illustrates that each OS shines in its unique light, addressing diverse user needs and system constraints. Whonix, with its innovative network compartmentalization, appeals to those with powerful hardware and a need for seamless online anonymity.
Qubes, with its rigorous security-through-isolation approach, attract users seeking the ultimate fortification of their digital activities. Meanwhile, with its amnesic properties and minimal system demands, Tails provides a formidable option for those requiring a portable, easy-to-use privacy-focused solution.
In conclusion, the Whonix vs Qubes vs Tails comparison is not about crowning a definitive winner but appreciating the different flavors of privacy and security these operating systems bring. Each has its niche, its unique approach, and its target audience.
They all share a common goal – to provide users with enhanced security and privacy in an increasingly interconnected world. So, the final choice hinges upon individual needs, preferences, and, of course, the hardware capabilities of the user’s machine.
With privacy and security at the forefront of technological discourse, these three operating systems make a compelling case for the vast options available to the discerning user.
Here’s a comparison table among Whonix, Qubes, and Tails:-
| Feature | Whonix | Qubes OS | Tails |
|---|---|---|---|
| Main Purpose | Privacy-focused operating system | Security-focused operating system | Privacy-focused, amnesic operating system |
| Anonymity | Built-in Tor integration for high anonymity | Uses Whonix for Tor integration; not by default | All network connections are routed through Tor |
| Security Model | Isolation through Tor and VMs (Virtual Machines) | Isolation through compartmentalized VMs | Ephemeral session-based model |
| Usability | Primarily used for tasks requiring high anonymity | Used for tasks requiring strong security | Primarily used for tasks requiring high anonymity |
| Installation | More complex due to VM requirement | Complex due to VM setup | Can be installed and run from a USB stick or DVD |
| Applications | Applications primarily focused on privacy | Supports a wide range of applications | Pre-installed with a set of privacy-centric applications |
| Networking | All network traffic is routed through Tor | Networking depends on specific VM | All network traffic is routed through Tor |
| Updates | Regular updates, including Tor | Regular updates | Regular updates, plus entire system is wiped between uses |
| Underlying OS | Based on Debian | Based on Xen hypervisor, supports various Linux distros | Also based on Debian |
| Persistence | Persistent system, saves changes between sessions | Persistent system, saves changes between sessions | Non-persistent by default, with optional encrypted persistence |
| Threat Model | Protects against global passive adversaries, at risk of targeted attacks | Designed for compartmentalization against various types of threats | Protects against both mass surveillance and targeted attacks, session-based |
| Ease of Use | Slightly more complex for beginners due to Tor and VM usage | Complex for beginners due to VM setup | More user-friendly due to live boot, but anonymity features require some learning |
Kicksecure vs Whonix
In an age where privacy, anonymity, and digital security are increasingly coveted commodities, operating systems that emphasize these attributes garner considerable attention.
This brings us to a compelling analysis of two stalwarts in this arena: Kicksecure vs Whonix. Although intrinsically linked, each platform offers distinctive features that cater to divergent user needs.
Delving into the heart of Whonix, we find an operating system intricately crafted to provide users with an unmatched level of online anonymity. Whonix leverages the Tor network to anonymize all internet traffic, allowing users to explore the digital expanse without fear of IP address leakage.
Furthermore, Whonix segregates network and non-network activities into separate virtual machines, reinforcing its defense against potential malware. To harness the full capabilities of Whonix, users must have hardware robust enough to run a virtual machine environment, such as VirtualBox or Qubes, alongside their primary OS. A dual-core processor and at least 4GB RAM is advised.
Kicksecure, on the other hand, is a security-hardened, non-anonymous Linux distribution. This may appear counterintuitive in a world where anonymity is usually intertwined with security, yet Kicksecure’s focus is a robust defense against malware and security threats.
It achieves this through several features, such as a hardened Linux kernel, minimized attack surface, verified boot, and reproducible builds. Furthermore, Kicksecure can run directly on your hardware, unlike Whonix, which operates within a virtual machine environment. As such, Kicksecure has lower system requirements and can function efficiently on most systems that can run a modern Linux distribution.
The Kicksecure vs Whonix comparison brings to light the unique traits of these two operating systems. While Whonix prioritizes user anonymity and mitigates the risk of IP address exposure, Kicksecure strengthens system security and resilience against malware.
Therefore, the choice between Kicksecure and Whonix largely depends on the user’s needs. If absolute online anonymity is your priority, Whonix is the better option. Conversely, if your focus lies on bolstering your system’s defense against potential security threats, Kicksecure is the favorable choice.
In summing up the Kicksecure vs Whonix comparison, it is critical to emphasize that both operating systems exhibit a staunch commitment to privacy and security. Their uniqueness lies in their specific approaches to achieving these objectives.
Whonix caters to users who need an extra layer of anonymity, while Kicksecure is an ally for those who need a sturdy line of defense against malware and other threats. Each OS has its niche and appeals to different sectors of the privacy-conscious community.
In the realm of privacy-focused operating systems, the Kicksecure vs Whonix comparison is a testament to the variety of tools available to users to pursue a secure and private digital life. The diversity of their offerings assures us that in this technology-driven world, privacy and security are desired and achievable for everyone.
Here’s a comparison table between Kicksecure and Whonix:-
| Feature | Kicksecure | Whonix |
|---|---|---|
| Main Purpose | Security-focused general purpose operating system | Privacy-focused operating system |
| Anonymity | Does not include Tor by default | Built-in Tor integration for high anonymity |
| Security Model | Non-anonymous, uses various hardening techniques | Isolation through Tor and VMs (Virtual Machines) |
| Usability | Suitable for a wide range of tasks | Primarily used for tasks requiring high anonymity |
| Installation | Easier to install | More complex due to VM requirement |
| Applications | General purpose, broad range of applications | Applications primarily focused on privacy |
| Networking | Uses clearnet | All network traffic is routed through Tor |
| Updates | Regular system updates | Regular updates, including Tor |
| Underlying OS | Based on Debian | Also based on Debian |
| Threat Model | Protects against general threats and malware | Protects against global passive adversaries, at risk of targeted attacks |
| Ease of Use | Easier for beginners and general users | Slightly more complex for beginners due to Tor and VM usage |
How Does Whonix Work?
Whonix, an innovative and security-focused operating system, is designed to provide users with high anonymity and privacy while navigating the internet’s vast and often perilous landscape.
Employing a unique architecture and a blend of advanced techniques, Whonix ensures that users can shield their online identities from prying eyes and malicious actors. To comprehend the inner workings of this cutting-edge system, it is essential to explore its fundamental components and the robust defense mechanisms it employs.
Virtualization at its Core:- At the heart of Whonix lies the concept of virtualization, where two separate virtual machines (VMs) interact to create a secure and isolated environment for online activities.
The first VM, the Gateway, functions as a transparent Tor router, channeling all internet traffic through the Tor network. The second VM, the Workstation, operates as the user’s primary interface for web browsing, communication, and other online tasks.
Tor – The Anonymity Network:- The Tor network is central to Whonix’s potency. It is renowned for its ability to conceal users’ IP addresses and route traffic through relays, encrypting and anonymizing data.
By funneling all network communication through the Tor network, Whonix ensures that a user’s real IP address remains hidden, making it remarkably difficult for adversaries to trace their online activities back to their origin.
Defense in Depth:- Whonix adopts a principle of “defense in depth,” implementing multiple layers of security to mitigate the risks of potential attacks and leaks. The virtual machine-based architecture provides inherent isolation between the Gateway and Workstation, preventing direct communication and minimizing attack vectors. Additionally, the Gateway enforces a strict firewall to regulate traffic flow, safeguarding against leaks.
Isolated Applications:- One of Whonix’s standout features is using separate Qubes Disposable VMs for specific applications. This approach ensures that each application operates within its own sandboxed environment, hindering the ability of adversaries to correlate activities or gain unauthorized access to other parts of the system. This isolation enhances security and reinforces anonymity.
Constant Updates:- To remain robust against emerging threats and vulnerabilities, Whonix follows a proactive approach by regularly updating its components and software packages. By keeping pace with the latest security patches and upgrades, Whonix ensures that users are shielded from known exploits, offering peace of mind and continued protection in an ever-evolving digital landscape.
Persistent Tor Circuits:- Whonix enhances Tor’s anonymity by employing persistent Tor circuits. This means that the same entry and exit nodes are retained for an extended period, providing continuity in the user’s online activities and reducing the likelihood of information leakage due to circuit changes.
Stream Isolation:- Whonix implements stream isolation to segregate different types of internet traffic. This ensures that each application utilizes a separate circuit, preventing the possibility of data correlation and safeguarding against certain traffic analysis attacks.
Security by Default:- Whonix adopts a security-first approach, implementing strict default settings to minimize potential risks. For instance, all internet-bound traffic is forced through the Tor network, eliminating accidental leaks that could compromise anonymity.
In conclusion, Whonix’s unique architecture, combined with its emphasis on virtualization, Tor integration, and multi-layered security, makes it a compelling choice for users seeking unparalleled anonymity and privacy.
By understanding how Whonix works and harnessing the power of this exceptional operating system, individuals can confidently navigate the online realm, knowing that their digital footprints are effectively veiled from prying eyes and potential threats.
📗FAQ’s
Can You Use Whonix with Tails?
Whonix and Tails are distinct privacy-focused operating systems, and while it is technically possible to combine them, it is generally not recommended. Both systems serve different purposes, and using them together could lead to conflicts and compromise their effectiveness.
Does Whonix Hide IP Address?
Yes, Whonix is designed to provide a high level of anonymity by routing all internet traffic through the Tor network. This process ensures that the user’s IP address remains concealed, making it challenging to trace their online activities back to their real identity.
Should I Use Whonix?
Whether to use Whonix depends on your specific privacy and security needs. If you prioritize maximum anonymity and protection against tracking, Whonix can be a suitable choice, particularly for activities requiring a high level of privacy.
Does Snowden Use Whonix?
While there is no concrete evidence about Edward Snowden’s current software choices, he is known to value privacy and security. Given its reputation as a robust privacy tool, it is plausible that he may have used or considered using Whonix.
How Much RAM Does Whonix Need?
Whonix requires a minimum of 1GB of RAM to function adequately. However, it is recommended to have at least 2GB or more for optimal performance, especially when running multiple applications.
Is Whonix Untraceable?
While Whonix provides a high degree of anonymity, claiming complete untraceability would be misleading. Anonymity tools like Whonix can significantly reduce the likelihood of tracing, but absolute untraceability is challenging to achieve.
Is Tails Safer Than Whonix?
Tails and Whonix have different security models, each with its strengths. Tails is an amnesic system, leaving no trace on the host machine, whereas Whonix provides isolation between the user and the internet. The choice between them depends on your specific security requirements.
Do You Need a VPN If You Use Whonix?
Using a VPN with Whonix is generally unnecessary and might compromise your anonymity. Whonix already routes traffic through Tor, which provides robust anonymity. Adding a VPN could create potential vulnerabilities and is not recommended.
Can IP Address Be Traced in Tor?
While Tor enhances privacy by routing traffic through a volunteer network, it is not entirely invulnerable. In some cases, with enough resources and sophisticated techniques, it is possible to trace an IP address back to its source, though this is challenging and rare.
Is Whonix Encrypted?
Whonix provides encryption for its data, ensuring that sensitive information remains protected even if the system is compromised. This encryption adds layer of security to the overall setup.
Is Whonix Persistent?
Whonix supports both persistent and non-persistent modes. In the persistent mode, changes made to the system persist across reboots, allowing the user to customize their environment and keep certain data secure.
Is Whonix Better Than a VPN?
Whonix and VPNs serve different purposes. Whonix focuses on providing anonymity by routing all traffic through Tor, while VPNs primarily offer encrypted connections and may not necessarily ensure anonymity. The choice depends on the user’s specific needs.
What OS Is Whonix Based On?
Whonix is based on Debian, a popular and widely used Linux distribution known for its stability and security.
Is Whonix a Gateway or Workstation?
Whonix combines two virtual machines – a “Gateway” that routes all traffic through Tor and a “Workstation” where users perform their tasks. This setup enhances privacy and isolation.
How Many People Use Whonix?
The exact number of Whonix users is not publicly disclosed. However, Whonix has a substantial user base among privacy-conscious individuals, journalists, activists, and researchers.
Do I Need a VPN If I Use Tails?
Using a VPN with Tails is generally unnecessary, as Tails already routes all internet traffic through the Tor network, providing robust anonymity and encryption.
Can Tails OS Be Tracked?
Tails OS is designed to enhance privacy and minimize tracking. However, no system can provide guarantees, and certain advanced tracking methods could compromise anonymity.
Can Tails Get Malware?
Tails OS is designed to resist malware, but it is not entirely immune like any operating system. Users should practice safe browsing habits and avoid downloading files from untrusted sources.
Does Whonix Have Tor?
Yes, Whonix relies on the Tor network to provide its users anonymous and secure internet access.
What Are Alternatives to Whonix?
If you’re looking for alternatives to Whonix, consider Tails, Qubes OS, or other privacy-focused Linux distributions.
Is Whonix a VM?
Yes, Whonix operates as a combination of two virtual machines – the Gateway and Workstation – enhancing security and privacy.
What Is the Difference Between Qubes and Whonix?
Qubes and Whonix are privacy-oriented operating systems but employ different security models. Qubes focuses on compartmentalization using virtualization, while Whonix relies on Tor-based anonymity.
Can Whonix Run on a USB?
Yes, Whonix can be installed and run from a USB drive, making it a portable and convenient option for enhanced privacy.
Is Whonix a Proxy?
Whonix is not a proxy in the traditional sense. It operates as a virtual machine setup, combining a Gateway and a Workstation to provide secure and anonymous internet access.
What Linux Is Whonix?
Whonix is based on Debian Linux, a well-established and secure Linux distribution.
Can I Use Whonix on Windows?
Yes, Whonix can be used on Windows systems through virtualization software like VirtualBox or VMware.
How to Install Tor Browser on Whonix?
To use Tor Browser on Whonix, it is already pre-installed in the Workstation. Simply launch the Tor Browser application as you would on any other system.
Is Tails OS Debian Based?
Yes, Tails OS is Debian-based, leveraging the stability and security of the Debian Linux distribution.
What Is Whonix-Gateway For?
The Whonix-Gateway is a virtual machine responsible for routing all internet traffic through the Tor network, providing enhanced anonymity for the user.
Can Whonix Leak IP?
Whonix is designed to minimize the risk of IP leaks. However, like any complex system, it may still be vulnerable to certain IP leak scenarios, especially if misconfigured or not updated.
Can I Be Tracked Using Tails?
Tails is designed to enhance privacy and anonymity, making it difficult for adversaries to track users. However, no system can guarantee absolute anonymity, and other factors, like user behavior, can impact tracking risks.
Is Tails OS Still Secure?
As a privacy-oriented operating system, Tails continues to receive updates and improvements to enhance security. However, users must stay vigilant and follow best practices to maintain security.
Does Tails Mask Your IP?
Yes, Tails routes all internet traffic through the Tor network, effectively masking the user’s IP address and providing high anonymity.
Is Whonix Really Anonymous?
Whonix is designed to provide high anonymity by leveraging the Tor network and isolating the user’s activities. While it enhances anonymity, users should still take precautions to remain anonymous.
Can You Run Whonix on VMware?
Yes, you can run Whonix on VMware, similar to VirtualBox. Both virtualization platforms are compatible with Whonix.
How Much RAM Does Tails OS Use?
The RAM usage of Tails OS varies depending on the user’s activities and the number of open applications. Tails is designed to run efficiently on systems with 2GB of RAM or more.
Conclusion
In this comprehensive comparison of Whonix and Tails, we’ve dissected each system’s core features, strengths, and potential pitfalls. Both systems have unique capabilities, Whonix with its isolated workspaces and Tails with its commitment to leave no trace behind. The choice between them ultimately hinges on your unique requirements, technical expertise, and the kind of security you need.
We hope that this detailed analysis has helped unravel the intricacies of the Whonix vs Tails debate, shedding light on what each has to offer and which might be best suited for your needs.
Remember, the landscape of internet security is ever-evolving, and staying informed is the best defense against potential threats. Keep exploring, stay curious, and, most importantly, keep prioritizing your online safety.
Continue your journey into online privacy and make sure to revisit your security choices as technology continues to advance regularly. We’ll be here to assist you along the way with the latest insights into internet security.