Are you looking for the best Ubuntu antivirus software? If you have stumbled upon the correct webpage. I will share a list of the best Ubuntu Antivirus in this article.
So, without any further ado, let’s get started –
Do you need an antivirus for Ubuntu?💁
Throughout my life, I’ve heard that Linux-based operating systems don’t require antivirus software.
To be honest, there is some truth in that argument, but that is not because Linux is virus-proof. Instead, it is because, for viruses, gaining root-level access on Linux is relatively more complex.
In addition, one most popular arguments are that Linux is not as popular and widely used as Windows and macOS. Therefore, hackers don’t target Linux and write viruses for it.
Another popular argument is that Linux is intrinsically more secure. Since gaining root-level access to Linux distros for viruses is nearly impossible, why to install an antivirus?
Let’s keep all arguments aside and face the truth. No matter what OS you use, Windows, macOS, or Linux, you are prone to get infected by viruses if you are not careful enough.
You can get infected by these viruses in various ways, such as while downloading or bringing files from other computers using a USB drive.
If you can avoid these things, you don’t need an antivirus, even for Windows or macOS. But the sad part is that we cannot do that, so we need antivirus software.
So, now the main question is, what are the best Ubuntu antivirus programs I can use to protect my Ubuntu machine? To help you make the right choice, below, we have covered some of the best antivirus software available for Ubuntu.
But before that, let us share some precautions that you can take to keep you safe in Ubuntu even without installing any Ubuntu antivirus program.
Practices that can keep you safe from viruses and malware in Ubuntu:-
The best thing about Ubuntu and other Linux-based OS is that they are safe and secure.
This is because the Ubuntu APT library is the primary source for downloading software and other utility tools in Ubuntu. This APT library is relatively safe and secure from viruses.
Therefore, if you don’t download files from third-party sources on your Ubuntu machine, you won’t even need a third-party antivirus if you take some safety precautions. These safety precautions include the following –
1. Disable Scripts
Web scripting viruses are the most common malware that directly injects your browser and compromises its security.
These viruses generally enter your computer when you click malicious pop-up ads or infected links. A DDoS attack is one of the most common web scripting viruses.
Disabling scripts is the easiest way to protect yourself from these scripting viruses. Some web browsers like TOR have built-in functionality that lets you disable scripts from the settings, but that is not the case with all browsers.
In that situation, you can use third-party script-blocking extensions in your browser. One of the best script-blocking extensions for Firefox that protect you against Flash and Java-based exploits is NoScript.
2. Keep your Ubuntu updated
Keeping your Ubuntu may seem overwhelming since Ubuntu releases new updates every six months. However, updating Ubuntu can help in many ways, especially with security and features.
For example, if you keep your Ubuntu updated, you will receive security updates for at least 18 months. On the other hand, the LTS releases provide regular security updates for the next three years.
If you don’t update your Ubuntu, you will not receive these security updates meaning your computer could be vulnerable.
3. Use a firewall
A firewall is a layer of security that regulates all the incoming and outgoing traffic on a network. Windows Defender is one of the most popular firewalls for Windows computers, and it comes pre-installed, but when it comes to Linux-based distros, people tend to overlook the need for a firewall.
One of the main reasons behind that is that most routers have a built-in firewall system that protects all the traffic and regulates all incoming and outgoing traffic.
These hardware-based firewalls are great for protecting you from incoming connections but do a poor job when it comes to deciphering outgoing traffic.
The hardware-based firewall allows the outgoing traffic for the apps connected through port 80. You need to install a software-based firewall system to help decipher programs that should be allowed to send traffic.
This way, as long as your firewall is updated and running, you will be protected from various types of viruses, such as botnets, trojans, and more.
One of the best firewalls for Ubuntu is Gufw. It is a graphical utility for Linux that allows you to manage an Uncomplicated Firewall (UFW).
It is mainly designed to install and configure a firewall on your Linux-based machine. It is an open-source utility that lets you easily add or remove firewall rules.
These are some of the best practices to protect your Ubuntu from virus attacks. Still, these practices are insufficient, especially if you often download files from unverified sources or plug USB drivers to copy files.
In those situations, you can install an antivirus program to add a layer of security.
You can follow the list of the best Ubuntu antivirus programs that we have shared below to pick the suitable Ubuntu antivirus for you.
So, here we go –
Best Ubuntu Antivirus To Safeguard Your Ubuntu OS
1. ClamAV
The first Ubuntu antivirus on our list is ClamAV, aka Clam AntiVirus. It is a free and open-source antivirus.
It was initially designed for Unix machines, but later, it introduced its support for a wide range of platforms, including Linux, macOS, and Windows. However, it didn’t gain such popularity amongst Windows and Mac users.
It is a command line scanner and is mainly designed to be used by system administrations and security professionals.
The best thing about ClamAV is that its database updates every four hours, making it a highly efficient and powerful antivirus program.
So far, it has tested over 80 million virus signatures, and almost 25,000 new viruses are added to its database daily. It also supports real-time virus protection, making it an excellent choice to keep your Ubuntu safe from antivirus.
Besides that, ClamAV is famous for scanning websites and emails for potential attacks such as phishing, malware, and more.
It also lets you update its virus database from some unofficial database sources such as Sanesecurity and Securiteinfo to make it more efficient for various types of threats.
I would say ClamAV is a fantastic antivirus program for Ubuntu computers. It can protect you from internet threats, and its thorough scan functionalities keep your files and database secured.
On top of that, it is completely free and open-source, so you have no reason not to try it.
Features:-
- Opensource
- Free
- Cross-platform works in Linux, Windows, and Mac OS
- Works from the terminal
- Support on-access scanning for mailing service
- Portable
ClamAV installation on Ubuntu
You can scan your whole ubuntu system by running the following command in the terminal window
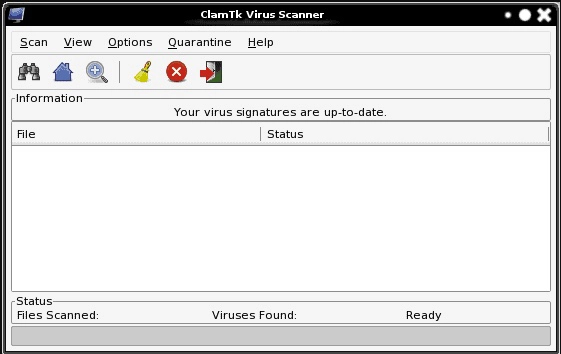
2. ClamTK
Next, we have ClamTK (Download Here) on our list. ClamTK is not a virus scanner on its own.
Instead, it provides a graphical user interface to the ClamAV that makes it easy to configure and use, especially for people who don’t want to get into technical and confusing CLI.
ClamTK can do almost everything you can do with ClamAV, but the GUI makes it easy to perform them. For example, you can easily configure ClamTK for both on-demand and scheduled scanning.
However, there is one difference between ClamTK and ClamAV. ClamAV is available for many devices, including macOS and Windows, while ClamTK is only available for Linux. Similarly, ClamTK is written in the Perl language, not C and C++.
The user interface of ClamTK has improved significantly in the recent few years. The latest versions are intuitive and feature-rich compared to the initially released versions of ClamTK.
To be frank, whether you use ClamTK or ClamAV is entirely up to you. If you are okay with CLI, go with ClamAV; otherwise, ClamTK isn’t wrong.
Features:-
- Opensource
- Easy to pick up
- Highly efficient
- Free
- Works from GUI
- Support quick scanning
- Portable
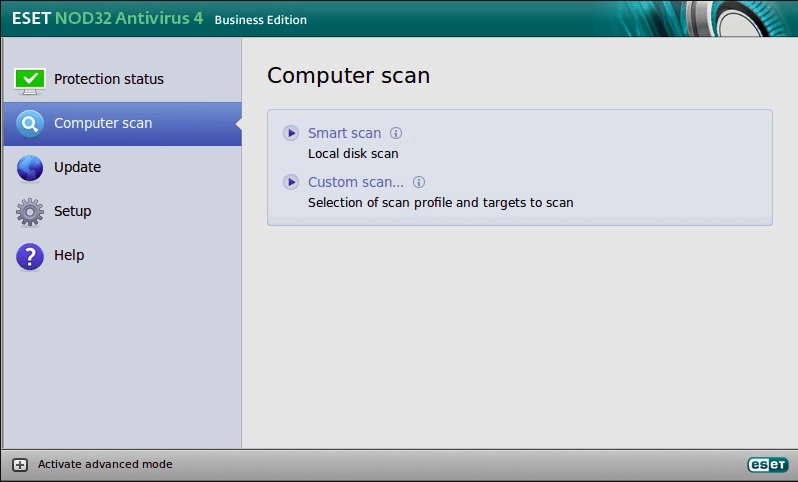
3. ESET NOD32 Antivirus
ESET NOD32 (Download Here) is not a free antivirus program, unlike the other two Ubuntu antiviruses we have discussed.
It is a fantastic antivirus program for Linux machines, but sadly, ESET has decided to terminate this product by the end of Q3 2022.
To replace it, ESET has introduced two new antivirus programs – ESET PROTECT Entry and ESET Endpoint Antivirus. Both antivirus programs are designed for companies and businesses but can be used by individuals too.
ESET PROTECT Entry is a modern multi-layered endpoint protection system that uses robust machine learning algorithms to protect your devices and virtual machines from viruses and malware.
It protects your company’s data while passing through available servers.
Other benefits of ESET Linux antivirus include an intuitive management dashboard, a single-click management function, easy installation, advanced reports, and custom notifications.
Besides that, if you want all-around performance, you can opt for the ESET Protect Advanced, which gives you access to full disk encryption, advanced threat defense, cloud app protection, mail security, and more. ESET Protect Advanced is mainly designed for businesses.
4. Sophos Antivirus
Sophos (Download Here) is one of the least-known names in the antivirus industry, but its competitive features make it an excellent choice. The best thing about Sophos is that here you can find products for almost anything, both free and paid ones.
Even though end-users might haven’t heard about Sophos that much, it is the industry leader in malware databases and advanced methods to fix malware-related issues.
It can detect viruses designed for various platforms, such as Linux, Windows, and macOS.
Sophos supports 14 popular Linux distros, including Debian, Ubuntu, Fedora, SUSE, and CentOS. It offers two versions on Linux machines – Sophos Antivirus for Linux X and Sophos Antivirus for Linux 9. Sophos Antivirus for Linux X is designed to manage and control various 64-bit systems.
On the other hand, Sophos Antivirus for Linux 9 is well suited for personal individuals. The sad part is that Sophos has officially announced that they are discontinuing Antivirus for Linux 9, and their support for it will end by July 2023.
Sophos Linux Antivirus’s best features include an on-demand malware scanner, firewall management via Sophos Central, real-time malware protection, scheduled scans, and more. It is pretty easy to use and supports both GUI and CLI.
However, one major drawback of Sophos antivirus for Linux is that it is not a free tool. You can opt for the free 30-day trial, but you must pay its cost once the trial duration ends.
The sad part is that they don’t have any official pricing list, and you will be quoted the price based on the devices you may use.
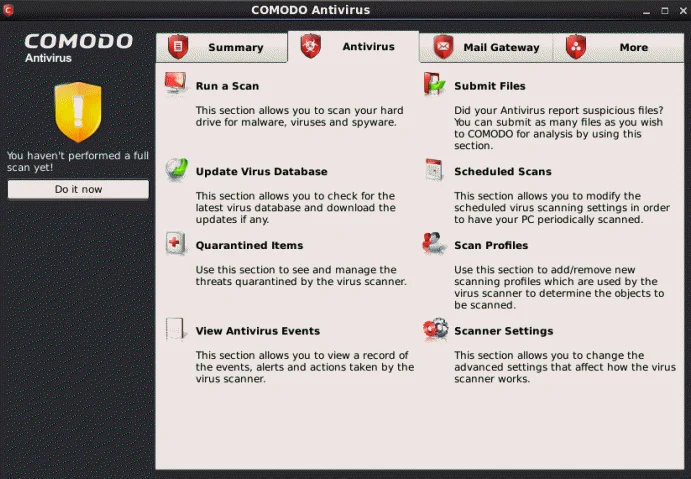
5. Comodo Antivirus for Linux
Next, we have Comodo Antivirus for Linux (Download Here) on our list. Comodo Antivirus has been around for over a decade, and in the meantime, it has received immense popularity.
One of the main reasons behind its popularity is that it offers a free version with limited access to features.
Comodo boasts a default deny protection functionality that automatically blocks all apps not in the whitelist.
This is a bit different than other antivirus programs, as most other antivirus programs rely on allowing all files except the ones that contain potential malware and viruses.
For this, Comodo argues that they have the most extensive database of legitimate programs; therefore, this functionality provides security benefits without any drawbacks.
Whenever Comodo scans a executable file but not in the list of whitelists, it runs the file in the quarantined environment.
They call this auto-sandbox technology, allowing you to run files that may have potential viruses without worrying about data leaks or other issues.
Besides that, Comodo boasts an email security function that automatically scans all your email inbox attachments for viruses, malware, and other threats.
Another fantastic feature of Comodo is its Game Mode. This mode disables annoying alerts and most other things during your gaming session, allowing you to focus on your games only.
On top of that, it also prevents Comodo from running in the background, offering optimal and stable gaming performance.
One of the best things about Comodo is that it offers a free tier. The free tier is good enough and offers plenty of features.
However, if you want access to features such as secure shopping, web filtering, or more, you must opt for the paid version.
6. Bitdefender GravityZone Endpoint Security Tools
Bitdefender GravityZone Endpoint Security (Download Here) is one of the best Ubuntu antiviruses. The best thing about this Ubuntu antivirus is that it is available for many Linux machines, including Debian, CentOS, Ubuntu, and Red Hat distributions.
This antivirus is mainly designed to provide state-of-the-art endpoint scanning for servers and networks but can also be used on personal computers.
It boasts a machine learning-based antivirus scanner, which delivers robust and efficient performance for testing malware and viruses.
It gives you access to Control Center, a cloud-based management tool that lets you monitor your machines, set security rules, manage firewalls, app sandboxing, website filters, and other things. The dashboard of this Control Center is quite intuitive and easy to use.
The firewall of this antivirus takes the security and performance of Ubuntu’s Uncomplicated Firewall to the next level. Besides that, it enables you to detect outgoing scripts, port knocking, MITM attacks, and more.
Hardcore Linux users may enjoy its CLI user interface that lets you run quick and deep scans, see past security events and quarantined files, see the status of your system, and more. If you don’t like CLI, you can install it with GUI.
Bitdefender GravityZone Endpoint Security is a premium tool, but it offers a 30-day free trial that you opt to test its services. On top of that, the pricing of this Ubuntu antivirus is quite flexible.
If you want to spend some bucks on your Ubuntu machine’s security, I highly recommend this antivirus program.
7. Kaspersky Antivirus
Lastly, we have Kaspersky Antivirus (Download Here) on our list. Like other Ubuntu antivirus programs, Kaspersky Antivirus is mainly designed for IT administrators, not end users.
But if you want, you can also get it for your Ubuntu computer. However, you must opt for a 10-device license, meaning you must convince your friends and family to use it.
If that is not a concern for you, Kaspersky is hands down one of the best security programs. It supports many Linux distributions, including Ubuntu, Red Hat Enterprise Linux, Linux Mint, CentOS, Debian, and more.
It also supports Windows and macOS, allowing you to quickly set up this antivirus in a hybrid environment. On top of that, its multi-layered protection protects your computers and the entire network from a wide range of cyber threats.
One great feature of Kaspersky Antivirus is Anti-Cryptor. This is a fantastic feature that protects your computer against ransomware threats.
For this, Kaspersky runs thorough scans regularly to see if any encryption is initiated, and if it notices something abnormal, it starts fixing it.
Besides, it provides real-time protection from zero-day attacks and offers features like behavior detection for proactive defenses and network threat protection.
It also automatically scans the removable drives to ensure your operating system won’t get infected.
Since this antivirus is primarily designed for organizations and companies, it offers no free tier.
It provides a subscription service that starts at $404 for ten computers. Again, I won’t recommend this antivirus if you are an individual, but it can be a great choice if you want it for a group of people.
8. Avast Core Security – Next-gen Linux server antivirus
Avast (Download Here) also stands among the best Linux antivirus. This antivirus also made it among the best in the AV-Test. It works with Ubuntu and other Linux distro’s 32-bit and 64-bit software architecture just like others.
This Linux antivirus supports core and network security and provides file server security. Users gearing up Avast with a system highly prefer servers. However, it performs equally well with home users.
It is one of the most certified performers regarding server security. Also performing cross-platform, it maintains its versatility.
Features:-
- Real-Time Protection and anti-spyware
- Planned scanning
- Server Security
- Core security, network security
- Home and industrial safety
- The regular update for assured defusing of a new threat
Our selection process to pick Ubuntu antivirus for this list
Creating a list of the best tools is never easy. You have to consider many things before coming to a conclusive decision. However, we kept a few things into account while selecting antivirus programs for this list which include –
Ease of use:-
The first thing we kept in mind is how easy it is to use that antivirus program. It was not a big deal for us since most Ubuntu users are comfortable using CLI and, therefore, are a bit techy.
Yet, we tried to pick antivirus programs that anyone can use.
Anti-malware capabilities:-
Another important thing that we looked for is anti-malware capabilities. It is essential to consider since antiviruses have only one task to complete: to protect you from viruses and malware, and if it isn’t capable enough of doing that, what’s the point of using it?
Pricing:-
We were least concerned about pricing since free Ubuntu antivirus programs such as ClamAV and ClamTK are capable enough to protect you from most cyber threats.
Therefore, if someone cannot afford to pay for premium Ubuntu antivirus programs, they can opt for these free tools to protect their device.
✅FAQ
Does Ubuntu need antivirus?
Ubuntu is less prone to malware and viruses than Windows, but it is not completely immune to them. Therefore, it is recommended to use antivirus software to protect your system from potential threats.
Does Ubuntu have antivirus software?
Ubuntu does not come with pre-installed antivirus software, but several antivirus options are available for Ubuntu users, such as ClamAV, Sophos Antivirus, and Bitdefender.
Best free antivirus for Ubuntu
Some of Ubuntu’s best free antivirus software includes ClamAV, Sophos Antivirus, and Comodo Antivirus.
Best antivirus for Ubuntu
Some of the best-paid antivirus software for Ubuntu include Bitdefender, Kaspersky, and ESET NOD32.
Is ClamAV a good antivirus?
ClamAV is a popular open-source antivirus software widely used in Linux-based systems, including Ubuntu. While it may not be as feature-rich as some paid options, ClamAV is a reliable and effective antivirus software that can provide basic protection against malware and viruses.
What is the default antivirus for Ubuntu?
Ubuntu does not have a default antivirus software, but ClamAV is a popular option that can be easily installed from the Ubuntu Software Center.
Is virus in Ubuntu better than Windows?
Ubuntu is generally considered less prone to viruses and malware than Windows due to its more secure design and lower market share. However, this does not mean Ubuntu is completely immune to viruses and malware.
How do I protect my Ubuntu?
To protect your Ubuntu system, it is recommended to keep your software up to date, use strong passwords, avoid opening suspicious emails and links, and use antivirus software.
How good is Ubuntu security?
Ubuntu is known for its strong security features, including its secure design, frequent security updates, and the use of the AppArmor security framework.
Should I have an antivirus on Linux?
While Linux systems are generally considered more secure than Windows, it is still recommended to use antivirus software to protect your system from potential threats.
What is the success rate of ClamAV?
The success rate of ClamAV in detecting and removing viruses and malware can vary depending on the specific threat and how up-to-date the software’s virus definitions are.
However, ClamAV is a reliable antivirus software that can provide basic protection against malware and viruses.
How to protect Ubuntu from viruses?
To protect your Ubuntu system from viruses, it is recommended to use antivirus software, keep your system up to date with security patches, and avoid downloading and installing software from untrusted sources.
How to clean malware in Ubuntu?
To remove malware from your Ubuntu system, you can use antivirus software like ClamAV or scan your system using a live CD. Removing any suspicious files and reverting to a backup if necessary is recommended.
Why is Ubuntu considered safe and not prone to viruses?
Ubuntu is considered safe and not prone to viruses due to its more secure design, frequent security updates, and sandboxing and access control measures to limit the potential impact of any security breaches.
Why is there no virus in Linux?
While Linux is not completely immune to viruses and malware, it is less prone to them than other operating systems like Windows due to its more secure design, open-source nature, and smaller market share.
How do I stop Ubuntu from spying on me?
To stop Ubuntu from collecting data and tracking your activities, you can disable certain features like the online search function and adjust your privacy settings. You can also use tools like Privacy Indicators to monitor and control your system’s privacy settings.
Is Ubuntu safe for net banking?
Ubuntu is generally considered safe for net banking if you take the necessary security precautions, such as using strong passwords, accessing banking sites only through secure connections, and using antivirus software to protect your system from potential threats.
Is everything in the Ubuntu software safe?
While Ubuntu’s software repository is generally safe, downloading and installing malicious software from untrusted sources is always a risk.
Therefore, it is recommended to only download and install software from trusted sources like the official Ubuntu Software Center.
Why is Ubuntu still the best?
Ubuntu is still one of the most popular Linux-based operating systems due to its user-friendly interface, frequent updates, strong security features, and a large community of users and developers.
How to install antivirus on Ubuntu?
Using the Ubuntu Software Center or the command line, you can install antivirus software like ClamAV on Ubuntu. For example, you can install ClamAV by running the command “sudo apt-get install clamav” in the terminal.
Is Linux safer than Windows viruses?
Linux is generally considered safer than Windows regarding virus and malware infections due to its more secure design, open-source nature, and lower market share.
Why Linux is more safer than Windows?
Linux is considered more secure than Windows due to its more secure design, frequent security updates, and the use of access control and sandboxing measures to limit the potential impact of any security breaches.
Is ClamAV a good antivirus for Linux?
ClamAV is a popular open-source antivirus software widely used in Linux-based systems, including Ubuntu. While it may not be as feature-rich as some paid options, ClamAV is a reliable and effective antivirus software that can provide basic protection against malware and viruses.
What is the hardest malware to remove?
Some of the hardest malware to remove include rootkits, which can hide deep in the system and are difficult to detect and remove.
Is ClamAV still supported?
Yes, ClamAV is still actively supported and maintained by its developers and community of users and developers.
Does McAfee work on Ubuntu?
McAfee is a commercial antivirus software primarily designed for Windows and Mac systems. While there is no official version of McAfee for Ubuntu, several other antivirus options are available for Ubuntu users, such as ClamAV and Bitdefender.
What is Ubuntu cleaner?
Ubuntu Cleaner is a free and open-source system cleaning tool that helps you to remove unnecessary files, cache, and packages from your Ubuntu system to improve its performance and free up disk space.
How to detect spyware in Ubuntu?
To detect spyware in Ubuntu, you can use antivirus software like ClamAV, scan your system using a live CD, or use a system monitoring tool like System Activity Monitor to monitor your system’s activity and detect any suspicious behavior.
What is the alternative for Malwarebytes in Ubuntu?
Malwarebytes is a popular antivirus software for Windows and Mac systems, but there is no official version of Malwarebytes for Ubuntu.
However, several alternative antivirus options are available for Ubuntu users, such as ClamAV, Sophos Antivirus, and Bitdefender.
Why don’t people use Ubuntu?
Some people may choose not to use Ubuntu due to its perceived complexity, lack of compatibility with certain software and hardware, or preference for other operating systems.
How common are Linux viruses?
While Linux viruses and malware are less common than Windows, they exist and can cause significant damage to a system if not detected and removed.
What is the most common malware in Linux?
Some of the most common malware in Linux include rootkits, backdoors, and Trojan horses.
Is Linux safe for banking?
Linux is generally considered safe for banking if you take the necessary security precautions, such as using strong passwords, accessing banking sites only through secure connections, and using antivirus software to protect your system from potential threats.
However, it is important to note that no system is completely immune to security breaches. It is always recommended to stay vigilant and take the necessary precautions to protect sensitive information.
Which antivirus is best for Ubuntu?
When choosing an antivirus for Ubuntu, a few good options exist. Some popular antivirus programs compatible with Ubuntu include ClamAV, Sophos, and ESET NOD32.
These programs are all well-regarded and have been proven effective at protecting against malware and other threats. Ultimately, the best antivirus for you will depend on your specific needs and personal preferences.
How do I protect my Ubuntu from malware?
Although Ubuntu is less vulnerable to malware than other operating systems, it is still essential to protect your system. Some ways you can protect your Ubuntu system from malware include:-
Keep your system up to date: Make sure you are running the latest version of Ubuntu, and regularly install security updates and patches to fix known vulnerabilities.
Use a reputable antivirus program: Several programs are compatible with Ubuntu, such as ClamAV, Sophos, and ESET NOD32 Antivirus. These programs can help protect your system from malware.
Be cautious when downloading and installing software: Only download and install software from reputable sources, and be sure to read reviews and check for security issues before installing anything.
Use a firewall: A firewall can help block incoming connections from malicious sources and can be a valuable tool in protecting your system from malware.
Be cautious when browsing the web: Avoid visiting suspicious websites, and be careful when clicking on links, downloading files, or entering personal information online.
These steps can help protect your Ubuntu system from malware and other threats.
What is a good antivirus for Linux Ubuntu?
A few good antivirus programs are compatible with Linux Ubuntu, including ClamAV, Sophos, and ESET NOD32 Antivirus.
These programs are well-regarded and have been proven effective at protecting against malware and other threats.
ClamAV is an open-source antivirus program popular among Linux users, while Sophos and ESET NOD32 Antivirus are commercial options that offer a more comprehensive range of features and support.
Ultimately, the best antivirus for you will depend on your specific needs and personal preferences.
Do I need an antivirus for Linux?
Whether or not you need an antivirus for Linux depends on how you use your system and what you use it for.
Linux systems, in general, are less vulnerable to viruses than other operating systems because they are built on a different architecture and are less commonly targeted by malware authors.
However, this does not mean that Linux systems are entirely immune to viruses and other forms of malware.
Using your Linux system to download and install software from the internet, browse the web, or connect to other devices is a good idea to use an antivirus program to protect your system.
This will help ensure that your system is protected against threats and that your data and personal information remain secure.
Are there Linux antivirus tools for personal use?
Yes, several Linux antivirus tools are suitable for personal use. Some popular options include ClamAV, Sophos, and ESET NOD32 Antivirus.
These programs are well-regarded and have been proven effective at protecting against malware and other threats.
ClamAV is an open-source antivirus program popular among Linux users, while Sophos and ESET NOD32 Antivirus are commercial options that offer a more comprehensive range of features and support.
Ultimately, the best antivirus for you will depend on your specific needs and personal preferences.
Are Linux antivirus tools hard to use?
In general, Linux antivirus tools are not difficult to use. Most antivirus programs for Linux have user-friendly interfaces that are easy to install and configure.
Some antivirus programs may require technical knowledge to set up and use, but many come with detailed instructions and support resources to help users get started.
Additionally, many Linux antivirus programs offer features like automatic updates and scheduled scans, which can help make it easier to keep your system protected without requiring a lot of manual effort.
If you are new to using antivirus tools on Linux, it is a good idea to research and compare different options to find one that is user-friendly and easy to use.
Is Ubuntu more secure than Windows?
Yes, there is no doubt that Ubuntu is more secure than Windows. Just as Windows is more prone to virus and malware attacks, you will not find the regularity on Ubuntu systems.
Furthermore, there are millions of Windows users around the world for all purposes, while for that, Ubuntu is far fewer.
Why does Linux generally not Require An Antivirus?
Most people agree that Linux OS does not require any antivirus. The reason this is true in multiple ways is that users around the world do not often prefer this operating system.
Hence, not many programs are created to infect the system. Also, even if your system encounters any bug in the system or even any app installed, the community is quick to fix those errors.
How do I check for viruses on Ubuntu?
To check if your Ubuntu system has viruses, you can use a popular software called ClamAV.
It is an open-source program that allows users to check the current viruses on their operating systems. After this, you can use another antivirus software to remove the malware and virus.
Closing Comments
There you have it – a detailed guide on Ubuntu Antivirus.
I fully agree when people say that the chances of your Linux-based machine getting infected by viruses are pretty low, but that doesn’t mean Linux machines are completely virus-free or you don’t have to worry about Linux viruses at all. Therefore, you have to be a bit cautious.
However, if you are using Ubuntu, I can assume you are a bit techy guy. Therefore, I won’t recommend you opt for the premium Ubuntu antivirus programs.
Instead, I will suggest you follow the tips I shared at the beginning of this article and install a free scanner – either ClamAV or ClamTK. This combination will be more than sufficient to keep you protected from viruses.
But if you don’t want to put yourself into all this stuff, you can opt for any premium Ubuntu antivirus. These antivirus programs are good enough to keep your device safe from malware, ransomware, and other cyber threats.
Even the “Security by Obscurity” sometimes fails regarding viruses. You may have the intuition that Ubuntu won’t face a severe threat due to viruses but you get wrong here. Using an Anti-virus helps you in any way and assures you of your security.
A simple “No threats found” is a relief for many who fear getting hacked. One should choose an apt Ubuntu Antivirus according to their need. We have mentioned it all: industrial or home, terminal or non-terminal.
Using an Ubuntu Antivirus will do you no harm and you will have the upper hand, as “Prevention is better than cure”.